by Cesar Navas
According to NIST Special Publication 800-123, Guide to General Server Security, “It is essential to first define the threats that be mitigated.” Many threats occur from bugs in operating systems, software, or applications with exploitable vulnerabilities, misconfigurations, or missing patches. Likewise, Compliance to organizational standards is sometimes a difficult item to track. Windows servers that are vulnerable and not compliant with organizational policy based on current accepted standards, present great risks to an organization, including the threats of network intrusion and data disclosure. Unprotected end servers running vulnerable applications may become a target and entry point for malicious attacks against the organization.
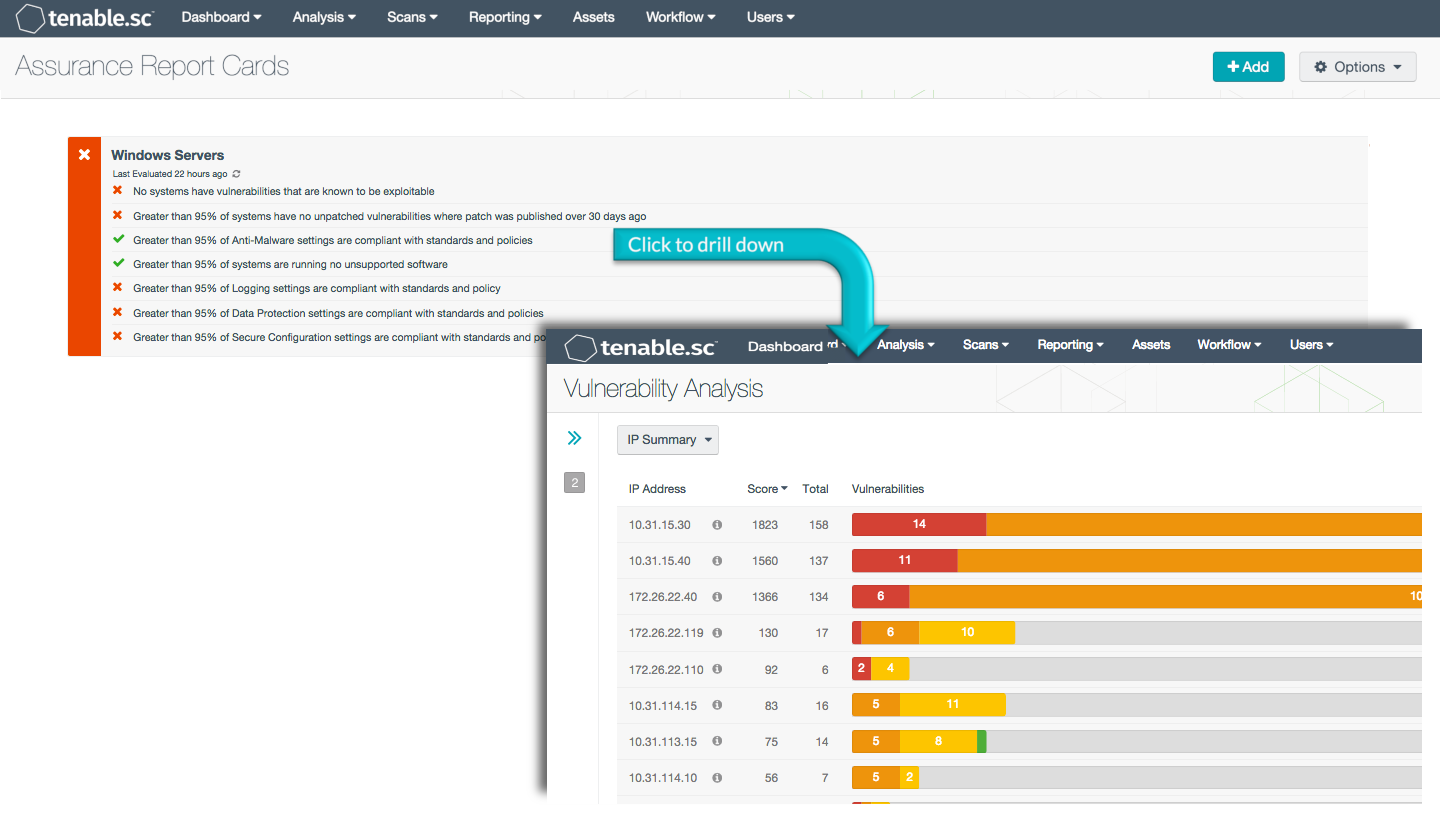
An important element of planning appropriate security controls within the organization is an understanding of the threat landscape for the environment. Traditional vulnerability scanning and review is a labor-intensive activity. The Windows Server Assurance Report Card (ARC) presents policy statements that provide configuration details on Windows servers. This makes reviewing policy compliance in real time quick and easy. This is accomplished utilizing assets that define all Windows Server specific operating systems, with filters for individual specific policy requirements to present accurate, relevant, and important compliance data.
This ARC makes use of standards such as NIST 800-53, DoD Instruction 8500.2, and the PCI Data Security Standard to highlight compliance failures on Windows servers. Checks against organizational policies, based on established standards and policies, such as secure configurations, malware, unsupported software/applications, and data protection are conducted in an effort to present Compliant/Non-Compliant conditions. This serves to highlight conditions that may lead to exploit based attacks, and to identify unpatched vulnerabilities in the environment.
Security controls and organizational policies should be based on appropriate current accepted standards. Servers should be protected based on the potential impact of loss to the organization of Confidentiality, Integrity or Availability.
The information in this ARC will allow the Compliance Manager to continuously monitor policy compliance for Windows servers, so that weak policies and weak policy enforcement can be identified and corrected and the network made more secure. This ensures that current policies are being enforced and are effective.
More details on each of the policy statements included in the ARC are given below. The Compliance Manager can click on a policy statement to bring up the analysis screen to display details on any compliance failures related to that policy statement. In the analysis screen, setting the tool to IP Summary will display the systems on which the compliance failures are present.
This ARC relies both on audit results obtained from Nessus scans of the systems on the network using appropriate audit files, and on vulnerability information collected by Nessus and PVS. The descriptions of the policy statements below include information on what details are used to find those checks relevant to the policy statement and what the percentage pass rate must be to be considered compliant. The audit files and ARC policy statement parameters are guides that can be customized as necessary to meet organizational requirements.
More details on each of the policy statements included in the ARC are given below. This ARC is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The ARC requirements are:
- Tenable.sc 5.0
- Audit results
- Nessus
- NNM
Tenable.sc Continuous View (Tenable.sc CV) is the market-defining continuous network monitoring platform. Tenable.sc CV includes active vulnerability detection with Nessus and passive vulnerability detection with Tenable's Nessus Network Monitor (NNM), as well as log correlation with Tenable's Log Correlation Engine (LCE). Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its network, in order to best measure compliance against complex standards.
ARC Policy Statements:
- No systems have vulnerabilities that are known to be exploitable. This policy statement displays Compliant in green if no Windows servers have vulnerabilities that are known to be exploitable.
- Greater than 95% of systems have no unpatched vulnerabilities where patch was published over 30 days ago. This policy statement displays Compliant in green if 95% or more of Windows servers have no unpatched vulnerabilities where the patch was published over 30 days ago. Applying patches or upgrades to protect against known vulnerabilities is an essential practice.
- Greater than 95% of systems are running no unsupported software. This policy statement displays Compliant in green if 95% or more of Windows servers are running no unsupported applications or software.
- Greater than 95% of Secure Configuration settings are compliant with standards and policies. This policy statement displays Compliant in green if 95% or more of the compliance checks on Secure Configuration settings have passed.
- Greater than 95% of Anti-Malware settings are compliant with standards and policies. This policy statement displays Compliant in green if 95% or more of the compliance checks on Anti-Malware settings have passed. Anti-Malware software protects the local OS from malware and assists in the eradication of any infections that occur.
- Greater than 95% of Data Protection settings are compliant with standards and policies. This policy statement displays Compliant in green if 95% or more of the compliance checks on Data Protection settings have passed.
- Greater than 95% of Logging settings are compliant with standards and policy. This policy statement displays Compliant in green if 95% or more of the compliance checks on Logging settings have passed. Capturing and monitoring log data is vital, and logging is the cornerstone of a sound security posture.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success