by Josef Weiss
Risk-based vulnerability management is a process that reduces vulnerabilities across the organization by prioritizing remediation based on organizational risk. Large organizations often struggle to get a big-picture view of their vulnerability management posture. Summarizing vulnerability data from large number of assets, applications, and services is a challenging task.
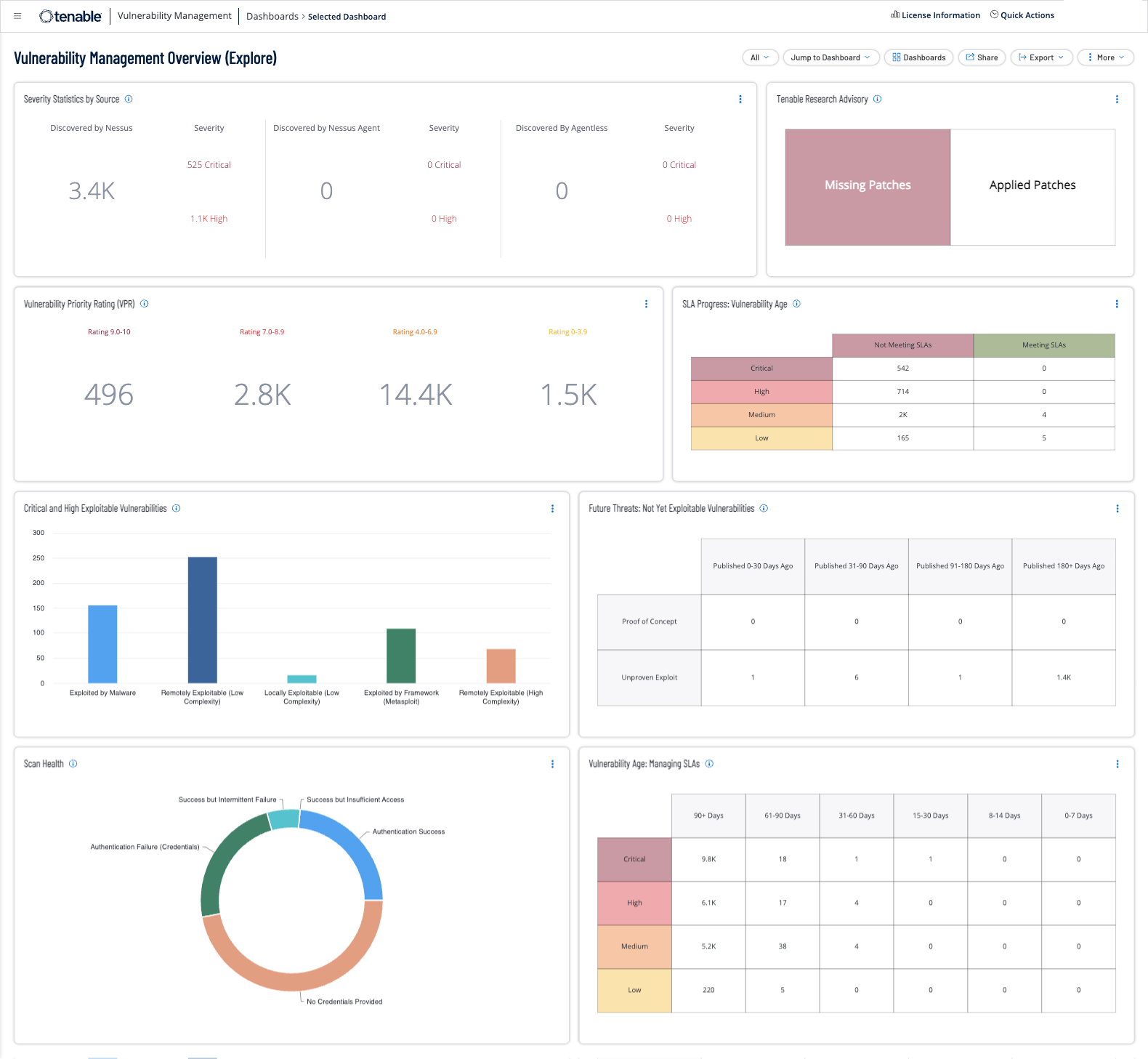
The Vulnerability Management Overview dashboard provides executive management a summary of risk information at a glance, while enabling security analysts to drill down into technical details by clicking on the widgets.
The widgets in this dashboard provide detailed information on vulnerability severity and mitigation status. Information is provided to help Risk Managers determine compliance with Service Level Agreements. Security Analysts can use the information in the Scan Health widget to determine if scans are running as intended to ensure accuracy of scan data. Executive Management and Security Analysts can leverage the information provided in this dashboard to ensure their vulnerability management program aligns with organizational goals.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.io discovers and analyzes assets continuously to provide an accurate and unified view of an organization's security posture. The requirements for this dashboard are: Tenable.io Vulnerability Management (Nessus, NNM)
Widgets
- Severity Statistics by Source - This widget provides a count of vulnerabilities collected through multiple sources: Nessus scan, Nessus Agent, Agentless Assessment, and Frictionless Assestment.
- Tenable Research Advisory - This widget provides two indicators for current major threats discovered by Tenable Research.
- Vulnerability Priority Rating (VPR) - This widget displays vulnerabilities grouped by Vulnerability Priority Rating (VPR).
- SLA Progress: Vulnerability Age - This widget helps organizations manage Service Level Agreements (SLAs) by providing a vulnerability view that is organized by Vulnerability Priority Rating (VPR) Score and Vulnerability Age.
- Critical and High Exploitable Vulnerabilities - This widget focuses on the most severe current threats, critical and high exploitable vulnerabilities to help prioritize remediation.
- Future Threats: Not Yet Exploitable Vulnerabilities - This widget provides a view of vulnerabilities based on exploit code maturity and vulnerability publication date.
- Scan Health - This widget provides a summary of scan health in relation to authentication success and failures.
- Vulnerability Age: Managing SLAs - This widget provides a view of vulnerabilities based on severity and age.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success