by Josef Weiss
February 26, 2015
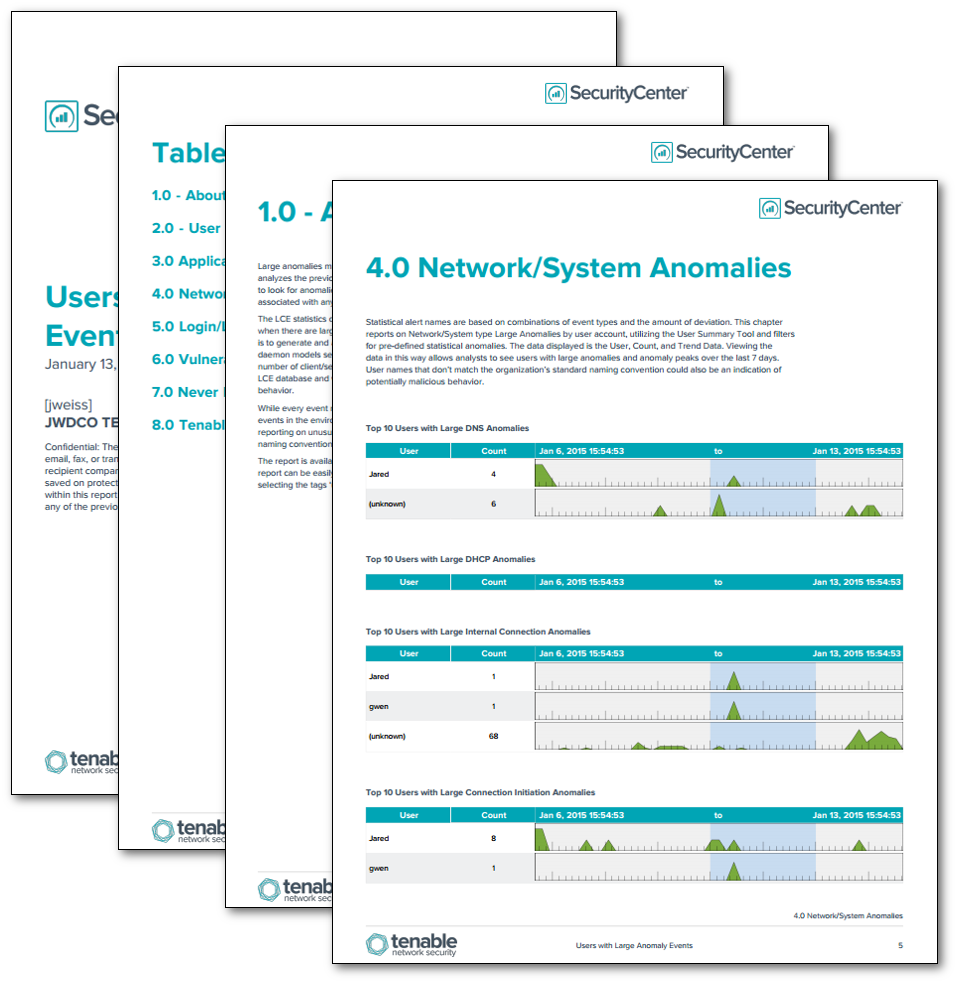
Large anomalies may be indicative of malicious behavior or network failure. Each hour, the LCE stats daemon analyzes the previous hour of activity and attempts to identify any series of events on every monitored host to look for anomalies. This report displays results utilizing the user summary tool to display user accounts associated with any existing large anomalies in the environment.
The LCE statistics daemon is designed to monitor LCE database files in real-time and generate new events when there are large changes in the behavior of events for a particular host. The sole purpose of the daemon is to generate and alert when a large statistical increase in any type of activity has been observed. The stats daemon models several characteristics of each host, including: inbound/outbound/internal connections, number of client/server connections, and the number of specific events. The statistics are maintained in the LCE database and when certain thresholds are crossed, events are generated that indicate these changes in behavior.
While every event may not be critical in nature, correlation can assist the analyst with detecting significant events in the environment. This supports the overall monitoring strategy by profiling normal activity and reporting on unusual activity as deviations occur. User names that don’t match the organization’s standard naming convention could also be an indication of potentially malicious behavior.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 4.7
- LCE 4.4.0
- PVS 4.0.3
SecurityCenter Continuous View (CV) allows for the most comprehensive and integrated view of network health. SecurityCenter CV provides a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. SecurityCenter CV also enables the analyst to react to advanced threats, zero-day vulnerabilities, and new forms of regulatory compliance. LCE provides deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities.
The report contains the following chapters:
- User Summary
- Application/Process Anomalies
- Network/System Anomalies
- Login/Logout Anomalies
- Vulnerability/Compliance Anomalies
- Never Before Seen/Unnormalized Anomalies
- Tenable Anomalies
Statistical alert names are based on combinations of event types and the amount of deviation. The chapters reports on Large Anomalies by user account, utilizing the User Summary Tool and filters for pre-defined statistical anomalies. The data displayed is the User, Count, and Trend Data.
Viewing the data in this way allows analysts to see users with large anomalies and anomaly peaks over the last 7 days. User names that don’t match the organization’s standard naming convention could also be an indication of potentially malicious behavior.