by Josef Weiss
August 7, 2015
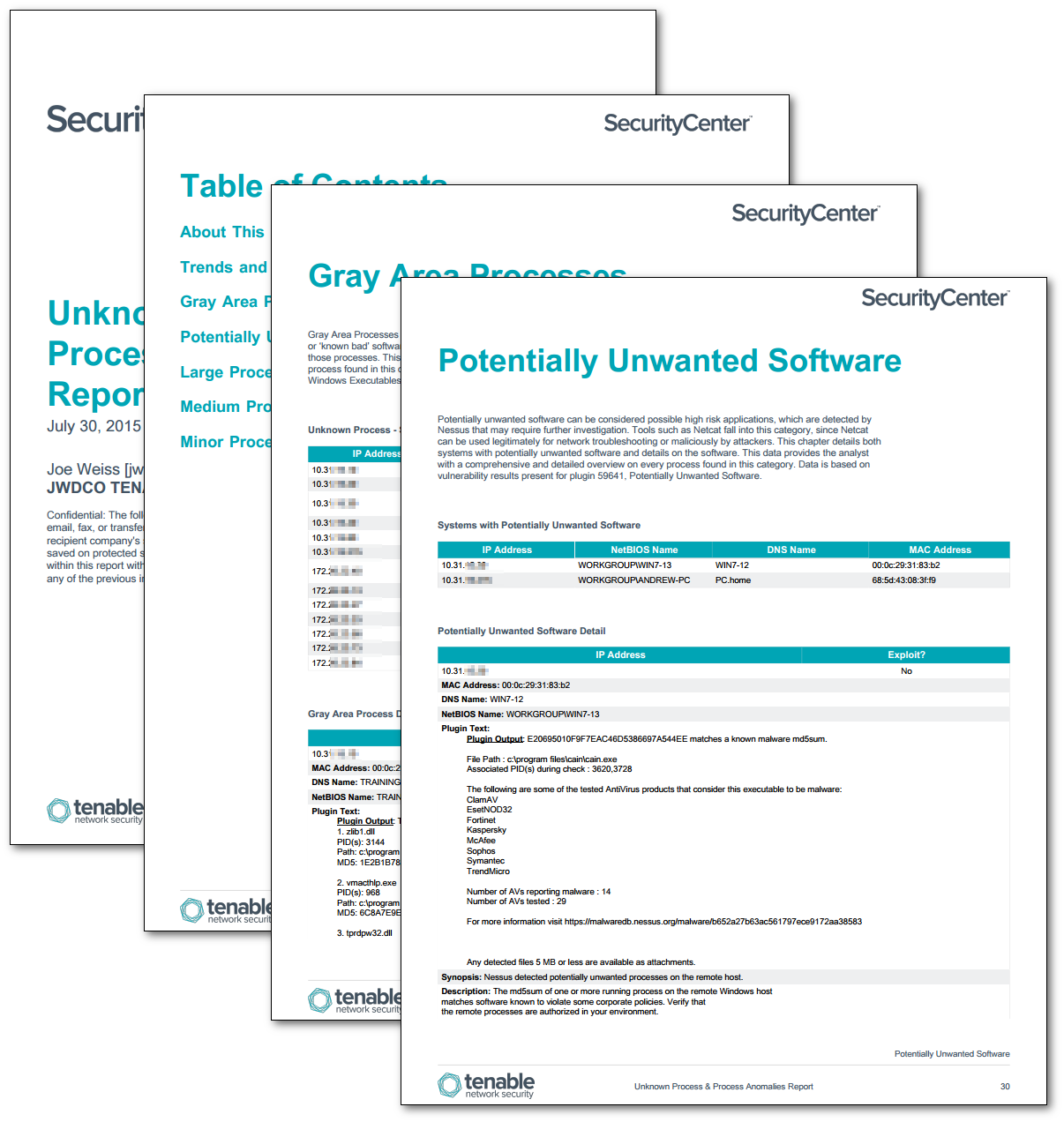
This report presents data on systems with process anomalies, never before seen anomalies, gray area processes, and potentially unwanted software. Process anomalies are generated by statistical alerts bases on a combination of events and the amount of deviation by Tenable’s Log Correlation Engine (LCE). LCE tracks every possible normalized event and creates a ‘never before seen’ alert and log when new events occur. The trend for Never Before Seen Anomalies displays these events over the previous 48 hours. Gray Area Processes are those running processes that are not present in a database of ‘known good’ or ‘known bad’ software. Potentially unwanted software can be considered possible high risk applications, which are detected by Nessus and may require further investigation. Tools such as Netcat fall into this category, since Netcat can be used legitimately for network troubleshooting or maliciously by attackers.
An increase in the number of statistical alerts, in the form of process anomalies, is an indication of higher loads on a system. This could be from increased usage, or the result of a denial of service attack. Systems that are also showing alerts, such as never before seen anomalies, gray area processes, or potentially unwanted software, should be investigated further.
Normalized events that are collected for each device are analyzed by LCE to determine if changes in expected behavior have occurred. If abnormal activity has been detected, such as deviations in the form of increased event types or connections have occurred, a process anomaly event will be generated. Data on the normalized events are compared hourly to the previous days same time period for the host in question. These events are categorized as large, medium, or minor process anomalies according to the size of the deviation.
The Unknown Process & Process Anomalies Report assists the analyst with determining which systems may be at a potential higher risk and which systems may require further investigation. In addition, this also aids in the detection of potential malware or malicious system processes within the environment by profiling device behavior, and detecting deviations from baseline activity.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 5.0.1
- Nessus 6.4.2
- LCE 4.4.1
Tenable's SecurityCenter Continuous View (SecurityCenter CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus, as well as log correlation with Tenable's Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network.
The following chapters are included in the report:
- Trends and Logs - The trend for Never Before Seen Anomalies displays these events over the previous 48 hours. Process anomalies are generated by statistical alerts based on a combination of events and the amount of deviation by Tenable’s Log Correlation Engine (LCE). LCE tracks every possible normalized event and creates a ‘never before seen’ alert and log when new events occur. The Anomaly log displays the last 100 anomaly events, in syslog format, from the previous 48 hour period.
- Gray Area Processes – Gray Area Processes are those running processes that are not present in a database of ‘known good’ or ‘known bad’ software. This chapter details both systems with Gray Area Processes and details on those processes. This data provides the analyst with a comprehensive and detailed overview on every process found in this category. Data is based on vulnerability results present for plugin 70768, Reputation of Windows Executables.
- Potentially Unwanted Software – Potentially unwanted software can be considered possible high risk applications, which are detected by Nessus that may require further investigation. Tools such as Netcat fall into this category, since Netcat can be used legitimately for network troubleshooting or maliciously by attackers. This chapter details both systems with potentially unwanted software and details on the software. This data provides the analyst with a comprehensive and detailed overview on every process found in this category. Data is based on vulnerability results present for plugin 59641, Potentially Unwanted Software.
- Large Process Anomalies – Process anomalies are generated by statistical alerts based on a combination of events and the amount of deviation by Tenable’s Log Correlation Engine (LCE). Data on the normalized events are compared hourly to the previous days same time period for the host in question. These events are categorized as large, medium, or minor process anomalies according to the size of the deviation. This chapter presents data on Large Process Anomalies reporting in categories for systems with Large Anomaly Events and Large Process Anomaly details. This data provides the analyst with a comprehensive and detailed overview on every process found in this category. This is accomplished using filter for the appropriate normalized event with a timeframe over the last 7 days.
- Medium Process Anomalies – Process anomalies are generated by statistical alerts based on a combination of events and the amount of deviation by Tenable’s Log Correlation Engine (LCE). Data on the normalized events are compared hourly to the previous days same time period for the host in question. These events are categorized as large, medium, or minor process anomalies according to the size of the deviation. This chapter presents data on Medium Process Anomalies reporting in categories for systems with Medium Anomaly Events and Medium Process Anomaly details. This data provides the analyst with a comprehensive and detailed overview on every process found in this category. This is accomplished using filter for the appropriate normalized event with a timeframe over the last 7 days.
- Minor Process Anomalies – Process anomalies are generated by statistical alerts based on a combination of events and the amount of deviation by Tenable’s Log Correlation Engine (LCE). Data on the normalized events are compared hourly to the previous days same time period for the host in question. These events are categorized as large, medium, or minor process anomalies according to the size of the deviation. This chapter presents data on Minor Process Anomalies reporting in categories for systems with Minor Anomaly Events and Minor Process Anomaly details. This data provides the analyst with a comprehensive and detailed overview on every process found in this category. This is accomplished using filter for the appropriate normalized event with a timeframe over the last 7 days.