by Cesar Navas
An organization spends a considerable amount of time and resources to identify vulnerabilities within the environment. Locating vulnerabilities is only a single step towards addressing risk. Typical vulnerability findings to not include remediation information. Many times, those vulnerabilities are not remediated in a timely manner. Yet addressing vulnerabilities is a critical step in the vulnerability management process. Verizon’s 2015 Data Breach Investigations Report (DBIR) concluded that the vast majority of exploited vulnerabilities were compromised more than a year after the associated CVE was published.
The goal of any vulnerability management program is to reduce the number of vulnerabilities, thereby reducing risk to the organization. Reducing risk involves assessing the vulnerabilities and the risks they present, then remediating those vulnerabilities. Allocating and drawing upon the required resources may cause organizations to make tough decisions about what vulnerabilities to remediate, and which ones will be allowed to remain.
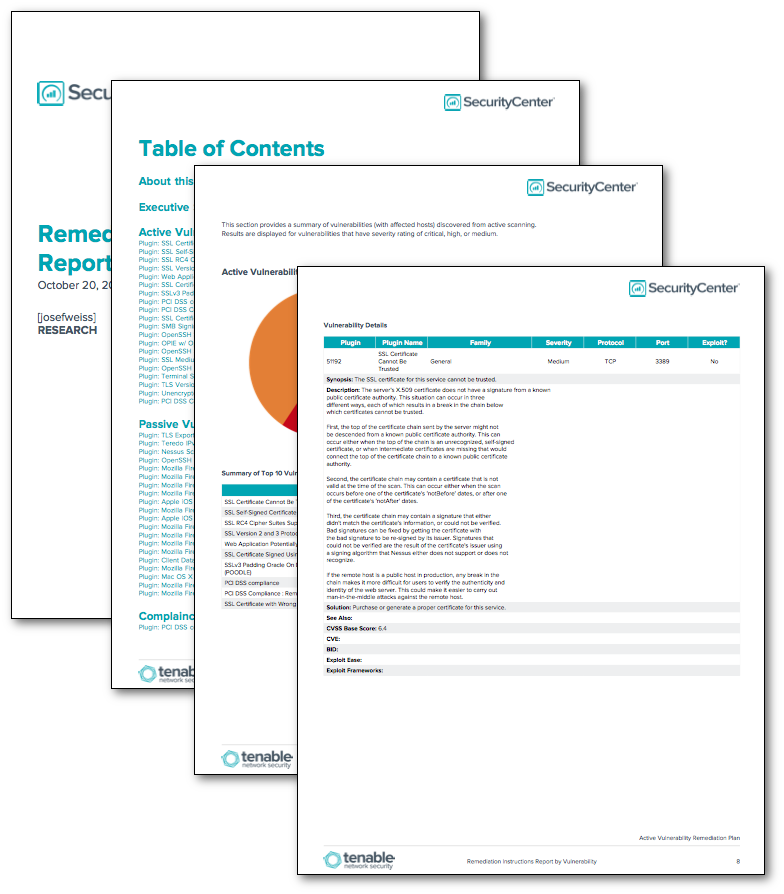
This report provides detailed information on the top discovered vulnerabilities, and lists the affected hosts tracked within Tenable.sc. This report also contains steps to mitigate the risk of the vulnerabilities, including resources from CVE, BID, and vendor knowledge base articles. Additionally, this report indicates if the vulnerability is exploitable and by which exploit platform.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment.
The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
- NNM 5.9.1
Tenable's Tenable.sc Continuous View (Tenable.sc CV) is the market-defining continuous network monitoring platform. Tenable.sc CV includes active vulnerability detection with Nessus and passive vulnerability detection with Nessus Network Monitor (NNM). Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its network.
This report contains the following chapters:
- Executive Summary - This chapter provides a top 10 summary of vulnerabilities (with affected hosts) discovered from active scanning, passive scanning, and compliance check failures performed by the Nessus vulnerability scanner and the Passive Vulnerability Scanner.
- Active Vulnerability Remediation Plan - This chapter provides a top 20 summary of vulnerabilities (with affected hosts) discovered from active scanning performed by the Nessus vulnerability scanner. Active vulnerability scanning sends packets to a target machine to provide a snapshot of the network services and applications installed, and to determine if vulnerabilities are present. Active scanning can perform highly accurate and rapid patch, configuration, and vulnerability audits across many systems, including Unix, Linux, Windows, network devices, and database systems.
- Passive Vulnerability Remediation Plan - This chapter provides a top 20 summary of vulnerabilities (with affected hosts) discovered from passive scanning performed by the Nessus Network Monitor (NNM). NNM is an advanced network monitoring application designed to detect vulnerabilities on the network by listening to network communications. Through passive monitoring, NNM can reveal devices and software on the network that are not authorized, or that may indicate a network compromise.
- Compliance Check Remediation Plan - This chapter provides a top 20 summary of compliance check failures discovered through performing scans with audit files in Tenable.sc. The compliance checks may vary in importance, depending on the environment. In this report, the checks that fail are listed as high severity.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success