by Cody Dumont
November 11, 2014
The Criminal Justice Information System (CJIS) Security Policy was created by the Federal Bureau of Investigation (FBI) to provide guidance to organizations dealing with Criminal Justice Information (CJI). The policy outlines roles and responsibilities for organizations, proper handling of CJI, and the implementation of both technical and physical security policies. The CJIS policy was designed to provide a base-level security policy for all entities that have access to CJI, and all organizations that interact with CJI must comply with the CJIS policy.
This report focuses on the CJIS Security Policy. Tenable’s Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring platform, which includes active vulnerability detection with Nessus, passive vulnerability detection with the Nessus Network Monitor (NNM), and log correlation with the Log Correlation Engine (LCE). Tenable.sc CV assists organizations in discovering compliance and vulnerability concerns on the network, assessing their impact, reporting on the results, and taking action to remediate issues. Tenable.sc CV provides proactive continuous monitoring across the organization to assist in responding to existing CJIS compliance requirements, as well as preparing for any changes to requirements that may arise in the future.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 4.8.1
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
For the related Tenable.sc dashboard, see the CJIS Security Policy dashboard.
Download the Analysis and Compliance to Meet CJIS and FTI Security Standards whitepaper.
The following chapters are included in the report:
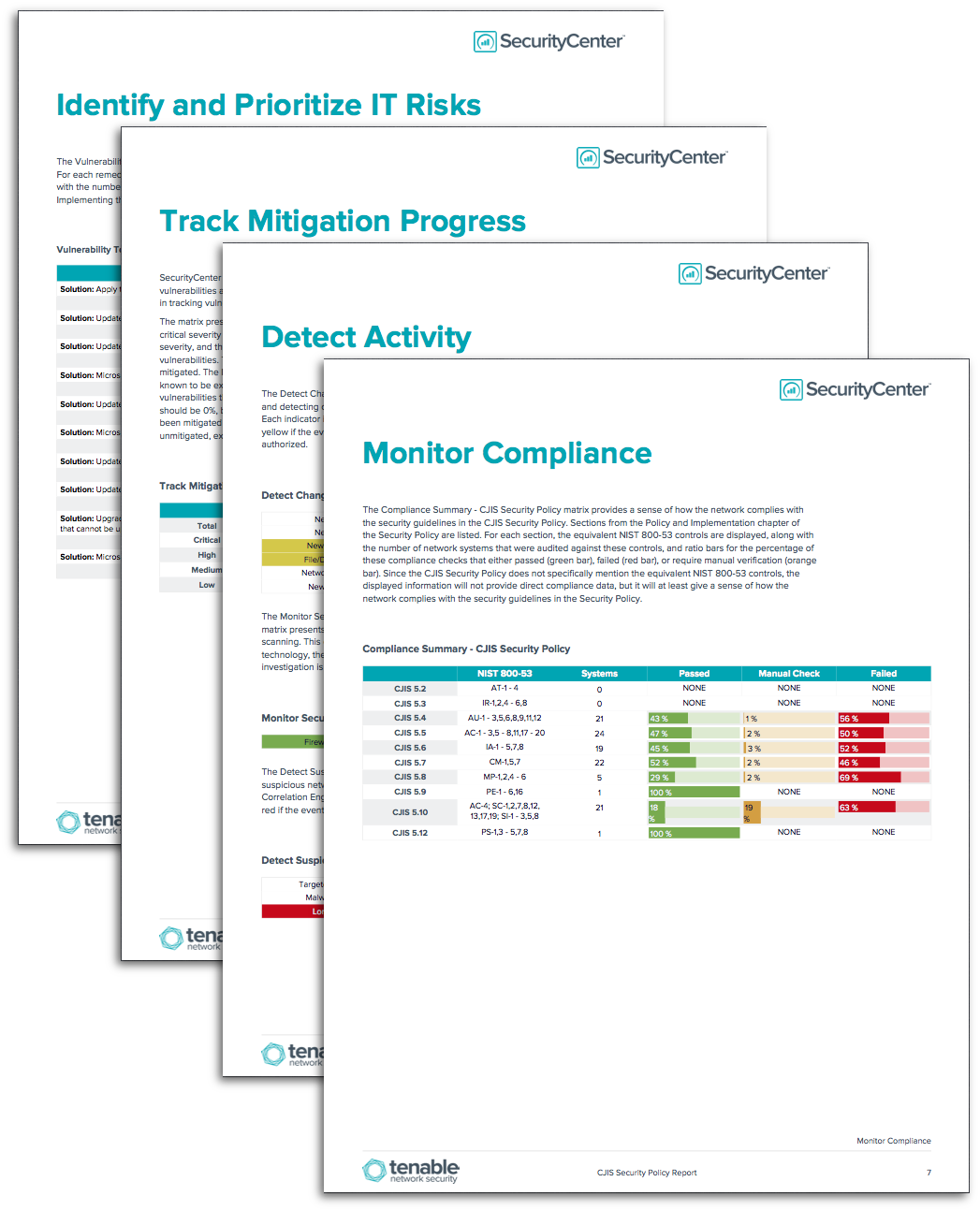
- Identify and Prioritize IT Risks - This chapter presents information about the vulnerability of the environment, including the top exploitable vulnerabilities and the top most vulnerable hosts found in the environment. Also presented are the top remediation opportunities.
- Track Mitigation Progress - This chapter presents information that can assist in tracking vulnerability mitigations in the environment.
- Detect Activity - This chapter presents information that can assist in monitoring the network, including alerts for detected changes, suspicious activity, and potential data leakage.
- Monitor Compliance - This chapter provides a sense of how the network complies with the security guidelines in the CJIS Security Policy, by measuring compliance with the equivalent NIST 800-53 controls.