Monitoring Unix and Linux hosts for vulnerabilities is an essential piece of securing a network. Various distributions can be susceptible to different vulnerabilities, so understanding which Unix or Linux distributions are used in the environment is important. Tenable.sc integrates with Nessus to monitor Unix and Linux hosts for vulnerabilities across various distributions.
The Unix and Linux Distribution Vulnerabilities dashboard assists security teams with monitoring Unix and Linux hosts within their network. Specific plugin families are used to identify vulnerabilities by distribution and severity. Detailed information is included about specific vulnerabilities detected across distributions. Plugin IDs are used to identify hosts with Unix or Linux operating systems and list the results by count. By monitoring Unix and Linux hosts in the environment, security teams can more effectively identify and remediate associated vulnerabilities.
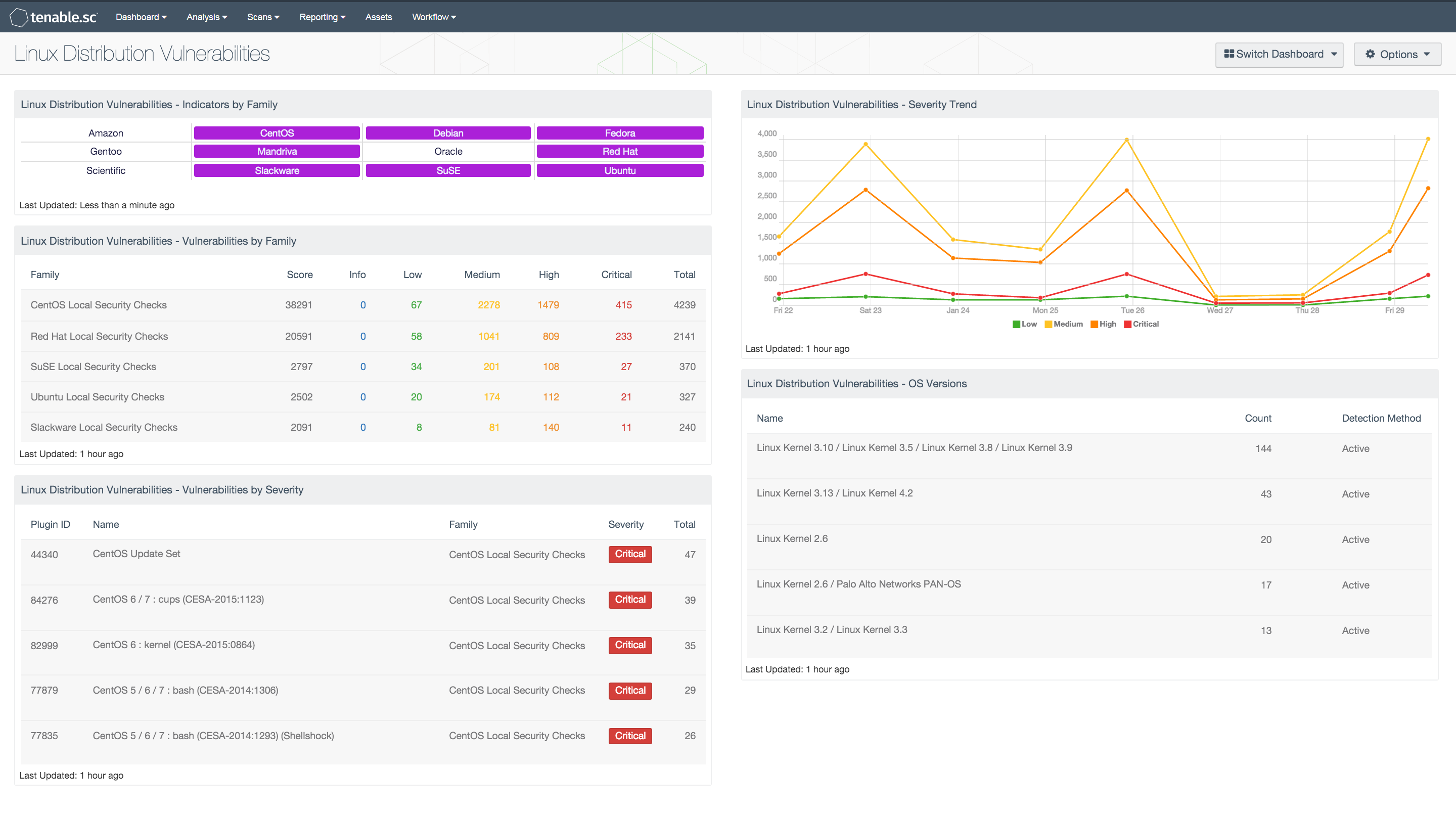
The components in the Unix and Linux Distribution Vulnerabilities dashboard present vulnerabilities and distributions. Tables list specific information about vulnerabilities by severity and distribution. An indicator matrix shows whether vulnerabilities have been detected on specific distributions in the environment. A trend chart demonstrates the rates of vulnerabilities by severity over the past week. Each component can be modified to focus on subnets or distributions of particular concern. Organizations can use the information provided to better monitor the presence of vulnerabilities across Unix and Linux distributions.
Note: Credentialed scans of the target machines are necessary to retrieve information from the local security check plugins.
This dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. This dashboard can be easily located in the Tenable.sc Feed under the category Monitoring. The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.6.0
- Local Security Checks
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. By integrating with Nessus, Tenable.sc CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
This dashboard includes the following components:
- Indicators by Family: The Indicators by Family matrix shows which Unix and Linux plugin families have detected vulnerabilities.
- Vulnerabilities by Family: The Vulnerabilities by Family table lists Unix and Linux plugin families in order of total vulnerabilities.
- Vulnerabilities by Severity: The Vulnerabilities by Severity table lists Unix and Linux vulnerabilities in order of severity.
- Severity Trend: The Severity Trend chart displays the trend of Unix and Linux vulnerabilities by severity over the past seven days.
- OS Versions: The OS Versions table lists the Unix and Linux operating systems detected by count.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success