by Cesar Navas
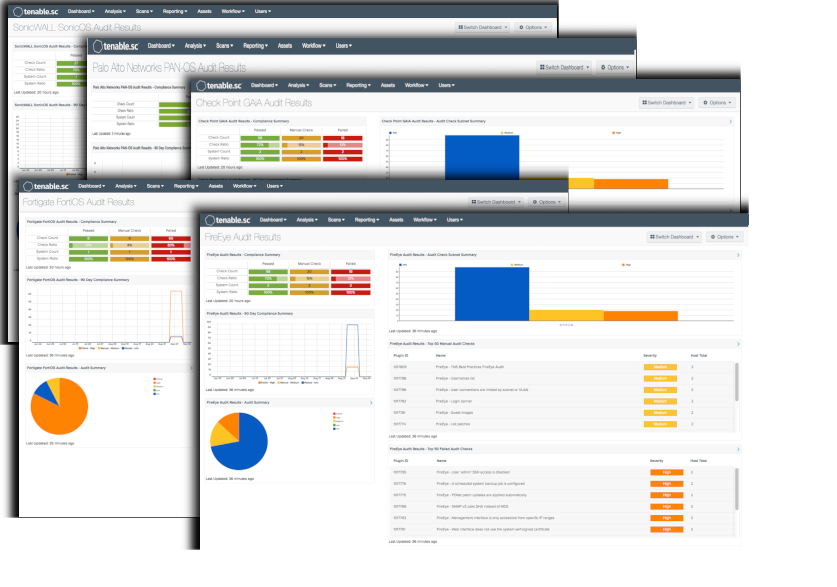
Governance, Risk Management, and Compliance (GRC) is a substantial part of any information assurance program. A GRC requires information systems to be audited, regardless of the standard to which the audit is performed. These dashboards provide the audit results for Check Point GAiA, FireEye, Fortigate, Palo Alto, and SonicWALL.
One of the initial steps in a successful GRC program is to set configuration guidelines and establish a supportable set of security policies. Tenable.sc Continuous View (CV) can measure compliance using audit files that cover a wide range of major regulations and other auditable standards. Tenable provides over 500 audit files, which are available for download from the Tenable Support Portal, in categories such as operating systems, applications, databases, and network devices. Tenable products can be used to audit systems based on SCAP content, and many Tenable audit policies have been certified by the Center for Internet Security (CIS). More information about audit files can be found in the Tenable Discussion Forums, Tenable Support Portal, Nessus Compliance Checks, and Nessus Compliance Reference.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments.
The dashboard requirements are:
- Tenable.sc 4.8.1
- Nessus 8.5.2
- Compliance Data
Audit files can be customized to match the values defined by an organization's corporate policies. Audit files are easily created or modified to support the organizations existing security policies. When an audit is performed, for each individual compliance check, Nessus attempts to determine if the host is compliant, non-compliant, or if the results are inconclusive and need to be verified manually. Unlike a vulnerability check that only reports if the vulnerability is actually present, a compliance check always reports a result. This way, the data can be used as the basis of an audit report to show that a host passed or failed a specific test, or if it could not be properly tested.
Tenable.sc CV is the market leader in providing a unique combination of vulnerability detection, compliance auditing, and reporting. Tenable.sc CV supports auditing more technologies than any other vendor, including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. This makes Tenable.sc CV the market-defining continuous network monitoring platform, and Nessus the market-defining vulnerability scanning for auditors and security analysts.
Check Point GAiA - Tenable.sc CV using Nessus has the ability to access the APIs used to audit systems running the Check Point GAiA software. Check Point GAiA is the most recent version of a secure operating system for all Check Point Appliances, open servers and virtualized gateways.
FireEye - Tenable.sc CV using Nessus has the ability to access the APIs used to audit systems running FireEye systems. The FireEye audit is based off of product documentation from FireEye and common criteria guidelines. The audit includes checks for auditing, identification and authentication, appliance management, intelligent platform management interface (IPMI), enabled services, encryption, and malware detection system configuration.
Fortigate - Tenable.sc CV using Nessus has the ability to access the APIs used to audit systems running FortiOS systems. The Fortinet FortiOS audit includes checks for password policy, malware detection configuration, enabled services, license information and status, log threshold configuration, NTP configuration, SNMP configuration, administrator user enumeration, patch update method, audit and log configuration, as well as authentication.
Palo Alto - Tenable.sc CV using Nessus has the ability to access the APIs used to audit systems running Palo Alto's PAN-OS. The compliance checks for Palo Alto use the XSL Transforms (XSLT) to extract the relevant pieces of information. Palo Alto Firewall responses are in XML format for most of the API requests, making XSLT the most efficient method for auditing.
SonicWALL - Tenable.sc CV using Nessus has the ability to access the APIs used to audit systems running the SonicWALL SonicOS. The SonicWALL SonicOS audit includes checks of the SSL configuration, password policy, banner configuration, administrative access ports, inactivity timeout setting, flood protection setting, client AV enforcement policy, logging & audit settings, enabled security services, gateway anti-virus configuration, authorization & authentication settings, and intrusion prevention service configuration.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success