by Ryan Seguin
The Qatar 2022 Cybersecurity Framework, The Capability Description – Network Security section (Chapter 5) focuses on protecting network and infrastructure systems. The framework describes the need for protecting the infrastructure and hardware used with interconnected devices and systems internally and externally. Entities determine which baseline standards to use, while the framework describes how to implement the processes, controls, and technologies required to build an effective network security program that is aligned to the business. Throughout the framework, details are provided about several standards such as NIAv2, PCI, HIPAA, and more. Using these references entities are able to audit and identify systems with configuration problems, and assess overall compliance.
In order to empower entities to focus on ‘Network Security’ capability defined under the ‘Prevention’ pillar of world cup cybersecurity regulations, Tenable.sc is equipped with tools that assist with meeting the various prerequisites to accomplish these capabilities. Entities must prove that risk is identified, assets are protected and inventoried, patch management processes are followed, and that all relevant industry regulations are complied with. Tenable.sc achieves this through successful integration throughout the Network Security Capability Model, (section 5.3) and grants in-depth visibility into each relevant layer.
Network infrastructure assets must be protected using well established best practices, which are described in this chapter, Network Security and the following chapters: Cybersecurity Governance, Data Protection, Application security, Data privacy and Cloud security. All assets connected to the corporate network must have information security policies applied and any changes or deviations should be authorized through change and patch management (refer Change and Patch management capability chapter). Therefore, the compliance data presented in this dashboard aims to identify relevant asset configurations to quickly and efficiently highlight needed configuration changes. Compliance data focused on standards like PCI, HIPAA, CIS, and other benchmarks are made available to provide a thorough overview. Entities can use this data to drill-down on a wide variety of assets from Point of Sale to Industrial Security. This compliance data visibility ensures that all capabilities are achievable in an efficient manner.
To better align and support analysis, the risk managers can create asset lists in Tenable.sc that align with the various assets defined in the technology section (section 5.7). When importing this dashboard, these assets can be used to set the focus of their data. Risk managers and network administrators gain greater focus on technologies outlined in the framework. Setting this focus allows for the creation of separate iterations of this dashboard with different asset lists to focus on Enterprise Networks, (section 5.8) if needed.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
• Tenable.sc 5.15.0
• Nessus 8.11.1
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess an organization’s adherence to best practice configuration baselines. Tenable.sc provides customers with a complete Cyber Exposure platform for completing effective cybersecurity practices.
Components
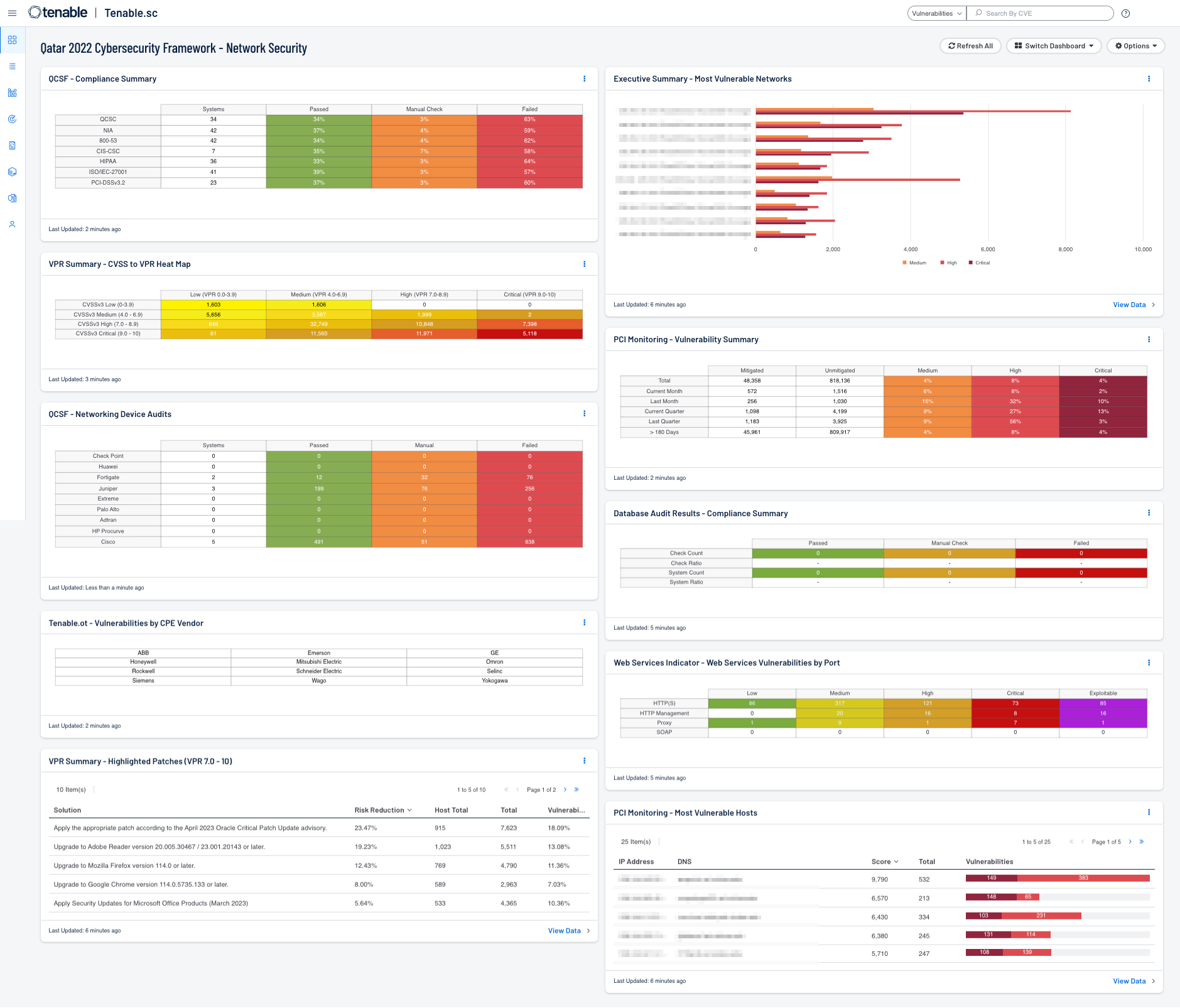
- QCSF - Compliance Summary - The Qatar Framework Network Security Compliance Summary matrix displays a summary of international compliance checks referenced by the Qatar Framework.
- VPR Summary - CVSS to VPR Heat Map - This component provides a correlation between CVSSv3 scores and VPR scoring for the vulnerabilities present in the organization.
- QCSF - Networking Device Audits - This matrix component presents a summary of audit checks performed on systems known as networking devices, such as routers, switches, and firewalls.
- Tenable.ot - Vulnerabilities by CPE Vendor - This component identifies vulnerabilities based on the Common Platform Enumeration (CPE) string and denotes vulnerabilities by device manufacturer. The CPE is broken down into separate strings and separated using a colon “:”. The first string denotes the manufacturer of the device. If the indicator is purple there is a match for the respective pattern.
- VPR Summary - Highlighted Patches (VPR 7.0 - 10) - The component uses the High and Critical VPR levels (VPR 7.0 - 10) combined with the remediation summary tool to provide a focused view of patches that should be considered at a higher priority than other patches.
- Executive Summary - Most Vulnerable Networks - This component contains a bar chart of the top 10 most vulnerable networks.
- PCI Monitoring - Vulnerability Summary - The “PCI Monitoring - Vulnerability Summary” matrix component displays an overview of vulnerabilities over time.
- Database Audit Results - Compliance Summary - The Database Compliance Summary matrix provides a high-level view of the Database compliance status.
- Web Services Indicator - Web Services Vulnerabilities by Port - The “Web Services Vulnerabilities by Port” matrix component provides insight into vulnerabilities by the listed service with a corresponding set of common ports.
- PCI Monitoring - Most Vulnerable Hosts - The “PCI Monitoring - Most Vulnerable Hosts” table lists the top 25 most vulnerable hosts by score.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success