by Ryan Seguin
January 26, 2021
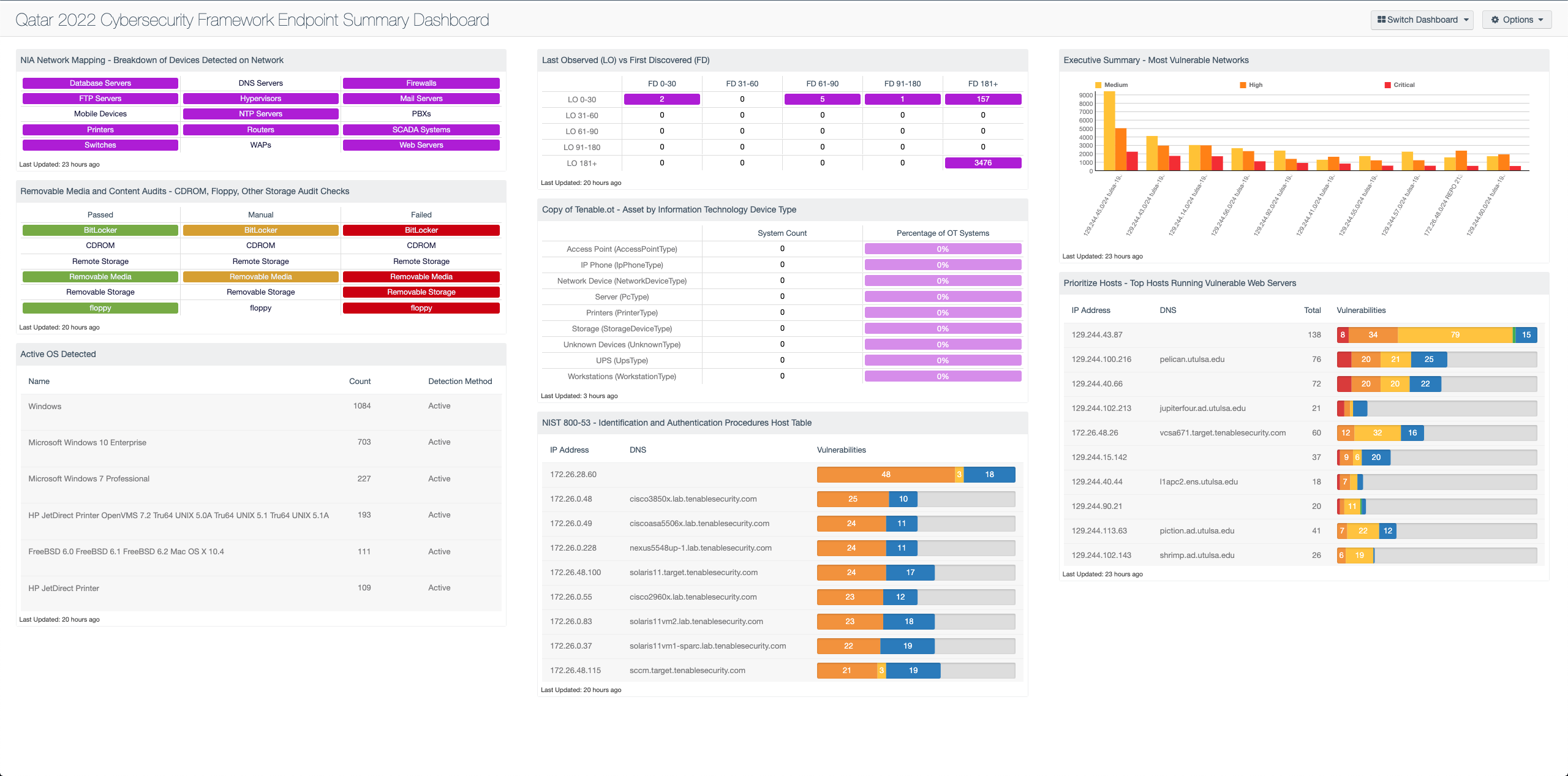
Massive events such as the FIFA 2022 World Cup™ present a significant attack surface and target rich environments for the criminally motivated. The State of Qatar is taking this seriously and setting cybersecurity and privacy at the top of the FIFA 2022 World Cup™ event agenda, requiring entities to adopt and implement The Qatar 2022 Cybersecurity Framework, and elevate endpoint security in preparation for the World Cup.
The Cybersecurity Frameworks Capability Description – Endpoint Security section (Chapter 3) focuses on protecting all endpoints such as servers, desktops, laptops, wireless devices, mobile devices and other OT/IoT devices from cyber threats. Tenable.sc enables entities to monitor and report on the implementation of the operational processes, security controls and other technologies required to build a sustainable endpoint protection program. By understanding the current risk associated with the endpoints, the Risk Manager can better align the mitigation efforts with the business objectives to support the World Cup services.
Modeled from the Cybersecurity Governance Capability within the framework, this dashboard is organized to highlight current endpoint risk. The IT operations team is given insights into the compliance status of a wide range of removable media and network devices. This data can be used to prioritize devices that are not properly configured, and need to be addressed before they can be used by the organization.
The framework’s endpoint security goals are to secure devices and ensure that unauthorized access and malicious activity is prevented. Vulnerability data is provided by device type and subnet so that entities can align their vulnerability management plans with the Cybersecurity Framework goals. By utilizing this dashboard, entities can be confident that their devices are hardened, managed, and monitored according to the requirements outlined in the cybersecurity framework.
Risk Managers can choose which area within the organization requires remediation. The first and last observed tables help guide scanning and remediation efforts for endpoints that have not been connected or recently scanned. Managers can cross reference that information to ascertain whether or not those devices have not been addressed properly within organizational SLAs, or if those devices have been disconnected.
The Qatar 2022 CSF clearly outlines the compliance and risk management requirements to ensure a secure environment for the 2022 World Cup. The tools within this dashboard offer managers a decisive way to confidently make decisions regarding the enterprise that they direct. Equipped with proper knowledge and tools, entities ensure that their organization’s needs are fully met.This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
• Tenable.sc 5.15.0
• Nessus 8.11.1
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess an organization’s adherence to best practice configuration baselines. Tenable.sc provides customers with a complete Cyber Exposure platform for completing effective cybersecurity practices.
Components
- NIA Network Mapping - Breakdown of Devices Detected on Network - This matrix presents a breakdown of detected network systems by type. This information assists an organization in maintaining an accurate inventory and detecting any unauthorized systems.
- Removable Media and Content Audits - CDROM, Floppy, Other Storage Audit Checks - This component focuses on compliance data, filtering on several strings containing CDROM, floppy, and other removable storage devices in the plugin name.
- Active OS Detected - This table provides the summary of operating systems detected using the List OS tool and plugin 11936 (OS Identification).
- CMMC - Last Observed (LO) vs First Discovered (FD) - This component compares First Discovered and Last Observed dates which gives insights into scan health.
- Tenable.ot - Asset by Information Technology Device Type - This component helps to group the Information Technology devices so risk managers can understand how IT and OT risk is calculated. The first column is a count of hosts, where the defined value is present in the Asset Identification plugin. The second column is the percentage of overall systems with plugins in the 500k range.
- NIST 800-53 - Identification and Authentication Procedures Host Table - This component displays a table of hosts that have been checked for NIST compliance checks related to an organization's identification and authentication.
- Executive Summary - Most Vulnerable Networks - This component contains a bar chart of the top 10 most vulnerable networks.
- Prioritize Hosts - Top Hosts Running Vulnerable Web Servers - This table displays the top hosts on the network that are running vulnerable web servers.