by Ryan Seguin
February 21, 2021
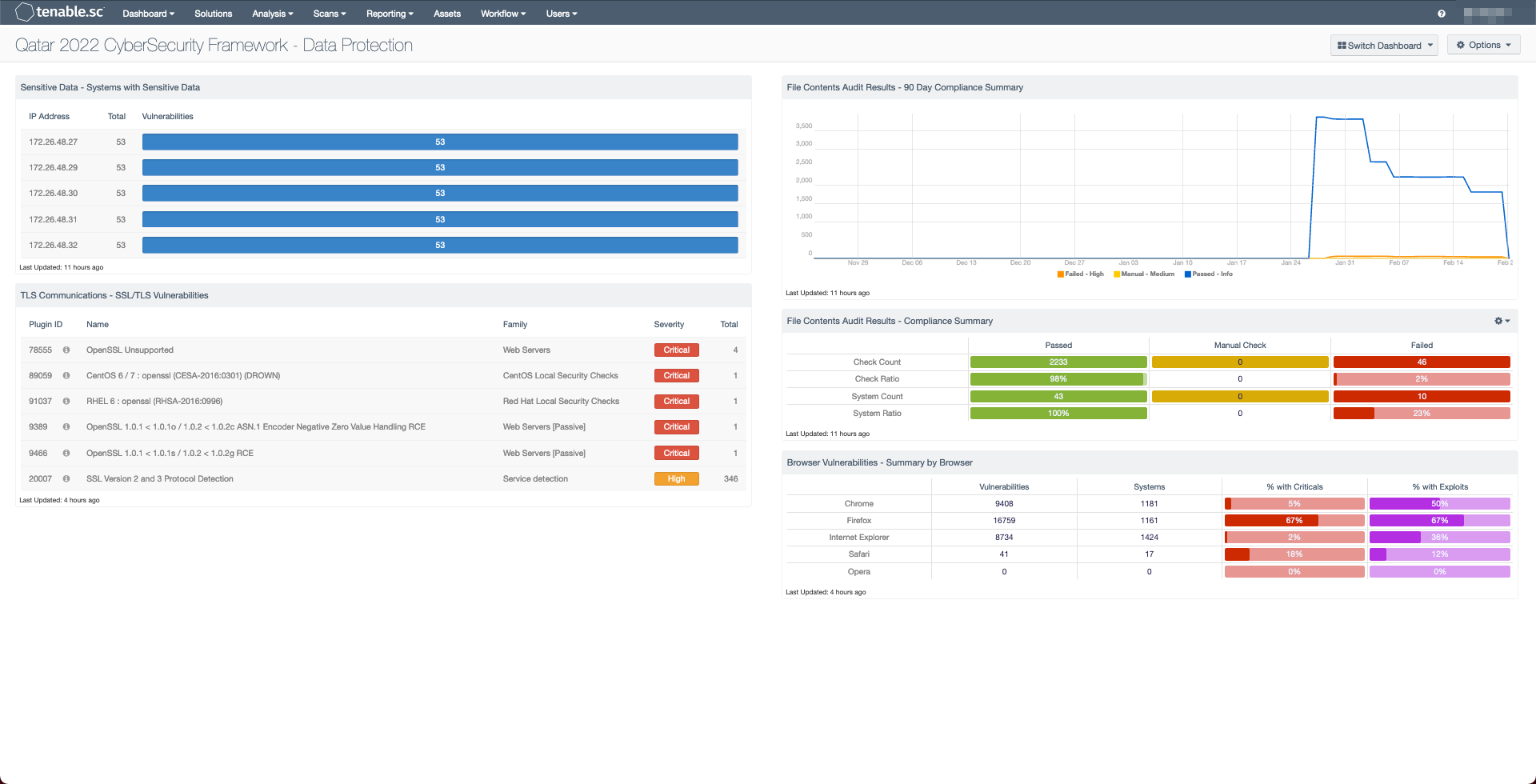
Massive events such as the FIFA 2022 World Cup™ present a significant attack surface and target rich environments for the criminally motivated. The State of Qatar is taking this seriously and setting cybersecurity and privacy at the top of the FIFA 2022 World Cup™ event agenda, along with elevating endpoint security in preparation for the World Cup. The tools within this dashboard offer managers a decisive way to confidently make decisions regarding the enterprise that they direct. Equipped with proper knowledge and tools, entities can ensure that their organization’s needs are fully met.
The Cybersecurity Frameworks Capability Description – Capability Description – Data Protection section (Chapter 6) focuses on preventative measures that data in motion is effectively secured to prevent data loss. Risk Managers need to see which systems have Personally Identifiable Information (PII) and which systems may be at risk of data exposure from an attacker. Tenable Audit scans looking for PII related data can identify common identification attribute like credit cards, and social security numbers.
Compliance data consists of multiple kinds of checks, primarily either configuration compliance or file content checks. This dashboard utilizes the file content checks to identify sensitive data. File content checks match different kinds of data contained in readable text files. In order to gain the required data needed for this dashboard, proper file content scan data must be gathered. The scanned files must not be encrypted, and must be contained in files that the credentials used in the scans.. Scans are also recommended to only be included in specific targeted scans to avoid excessive disk usage on targets, and the relevant PII data must be within the first 50 kilobytes of a scanned document.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
• Tenable.sc 5.15.0
• Nessus 8.11.1
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess an organization’s adherence to best practice configuration baselines. Tenable.sc provides customers with a complete Cyber Exposure platform for completing effective cybersecurity practices.