by Cody Dumont
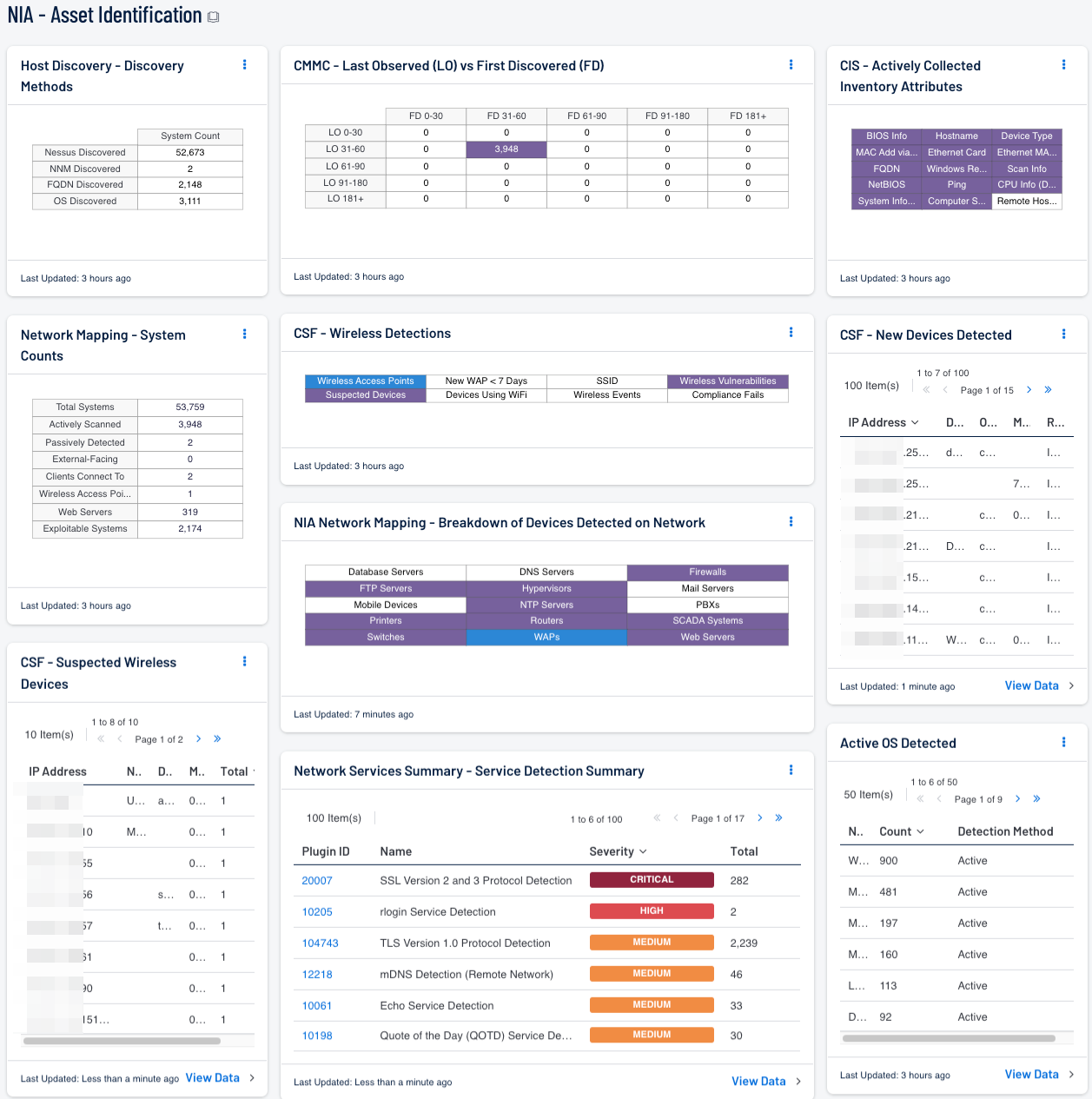
The National Information Assurance (NIA) Policy v2.0 requires that agencies have appropriate inventory management solutions in place. Tenable recommends using the Cyber Exposure Life Cycle model in conjunction with NIAv2 compliance efforts. The first stage, Discovery, of the Cyber Exposure lifecycle includes identifying and mapping assets across any computing environment. In order to maintain proper inventory of assets, the risk manager must understand when new assets are added to the network and keep an inventory of them. Tenable.sc provides multiple methods of detecting assets including active and passive scanning. Using this dashboard a risk manager is able to track new and existing assets.
In order to maintain an asset inventory, assets need to be appropriately categorized. Detailed information should also be available to help answer questions about the asset. For example:
- Where is it?
- What does it do?
- Who owns it?
Tenable.sc uses active and passive plugins to collect asset information including asset name, type, IP address, MAC address, location, serial number, and other important information. One method of identifying the device category is using the plugin “Device Type (54615)”. This plugin maps operating systems and other asset behaviors to different categories such as a server, router, or firewall. Other methods are also used to identify device categories such running services or open ports. Tenable.sc provides several scalable approaches to identifying asset types.
Tenable.sc uses two dates to track assets and vulnerabilities, they are: First Discovered and Last Observed. The First Discovered date indicates the date an asset is first seen by Tenable.sc, while the Last Observed date indicates the most recent time the same asset was observed. Insight into scanning health can be attained when these two dates are compared over time. A normal scanning program will show First Discovered assets covering a fairly even spread over time. Assets that have similar First Discovered and Last Observed times are new, while assets with older Last Observed dates may no longer be present in the environment or are not being scanned. The comparison of First Discovered and Last Observed dates can help ensure all assets are accounted for and regularly scanned. Tenable.sc utilizes active scan plugins to show a variety of wireless device information. Suspected wireless devices, access points, wireless vulnerabilities, and more can all be shown using active plugin searches. Compliance data can also be mined for related configuration settings.
The dashboard and its components are available in the Security Center Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Security Center Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Security Center 5.14.1
- Nessus 8.10.1
- Compliance data
Security Center is the market-defining On-Prem Cyber Exposure Platform. Security Center provide the ability to continuously Assess an organization’s adherence to best practice configuration baselines. Security Center provides customers with a full and complete Cyber Exposure platform for completing an effective Information Security Management System program prescribed by the NIA standard.
Components
Last Observed (LO) vs First Discovered (FD) : This component compares First Discovered and Last Observed dates which gives insights into scan health.
Host Discovery - Discovery Methods: This maxtrix provides a list of host detection methods allowing the organization to monitor the coverage of each sensor.
CSF Wireless Detections : This component presents a breakdown of detected wireless access points, wireless vulnerabilities, and wireless event activity on the network.
CSF - Suspected Wireless Devices : Along with wireless devices, many stand-alone devices today include wireless access capabilities such as printers, digital cameras, and more. This component presents detected suspected wireless devices on hosts within a network.
NIA Network Mapping - Breakdown of Devices Detected on Network: This matrix presents a breakdown of detected network systems by type. This information assists an organization in maintaining an accurate inventory and detecting any unauthorized systems.
Network Mapping - System Counts: This component presents the counts of systems detected on the network in various categories.
Network Services Summary - Service Detection Summary: This component presents a list of services detected on internal network hosts. Services presented within this table can include network protocols, databases, servers, remote desktop services, and more.
CIS - Actively Collected Inventory Attributes: This matrix provides a series of saved searches that contain hardware attributes, collected actively as part of a hardware inventory.
CSF - New Devices Detected : This component presents New hosts detected within the last 48 hours.
Active OS Detected : This table provides the summary of operating systems detected using the List OS tool and plugin 11936 (OS Identification).
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success