by Cesar Navas
On December 9, researchers published proof-of-concept (PoC) exploit code for a critical vulnerability in Apache Log4j, a Java logging library used by a number of applications and services. This vulnerability, identified as CVE-2021-44228, is a remote code execution (RCE) vulnerability in Apache Log4j. This vulnerability impacts a number of services and applications used widely across the internet, and is actively being exploited with multiple proofs of concept now appearing on GitHub.
According to the published CVE, all Apache Log4j versions 2.14.1 or less are vulnerable. An unauthenticated remote attacker could exploit this flaw by sending a specially crafted request to a server running a vulnerable version of Log4j. The crafted request uses a Java Naming and Directory Interface (JNDI) injection via a variety of services including:
- Lightweight Directory Access Protocol (LDAP)
- Secure LDAP (LDAPS)
- Remote Method Invocation (RMI)
- Domain Name Service (DNS)
Successful exploitation could lead to RCE. In Log4j version 2.15.0 and higher, this behavior is disabled by default.
The solution is complex because Log4j version 2.15.0 requires Java 8 to be installed. Therefore organizations using older versions of Java will be required to upgrade Java before applying the patched version. Log4j is also used by a number of cloud service providers, making the full scope of this vulnerability unknown at this time. A list of Tenable plugins to identify this vulnerability will appear here as the plugins are released.
Tenable has provided the log4shell Critical Vulnerability dashboard to assist organizations with the identification of whether Log4j is installed and currently running on any previously scanned assets. Because the update also requires Java 8 to be installed as a prerequisite, information on Java installations is also provided. This information can be used by organizations to determine the scope of their mitigation efforts. Tenable Research has also released a blog post that outlines additional steps that organizations can take to protect themselves from this vulnerability.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Security Industry Trends.
The dashboard requirements are:
- Tenable.sc 5.19.1
- Nessus 10.0.1
The Security Response Team (SRT) in Tenable Research works to dig into technical details and test proof-of-concept attacks, when available, to ensure customers are fully informed of the risks. The SRT also provides breakdowns for the latest vulnerabilities in the Tenable Blog. Tenable Research has released over 165,000 plugins and leads the industry on CVE coverage. Tenable's SRT team continuously works to help organizations prioritize and create remediation plans for the new threats, which often leave very little time for reflection.
This dashboard contains the following components:
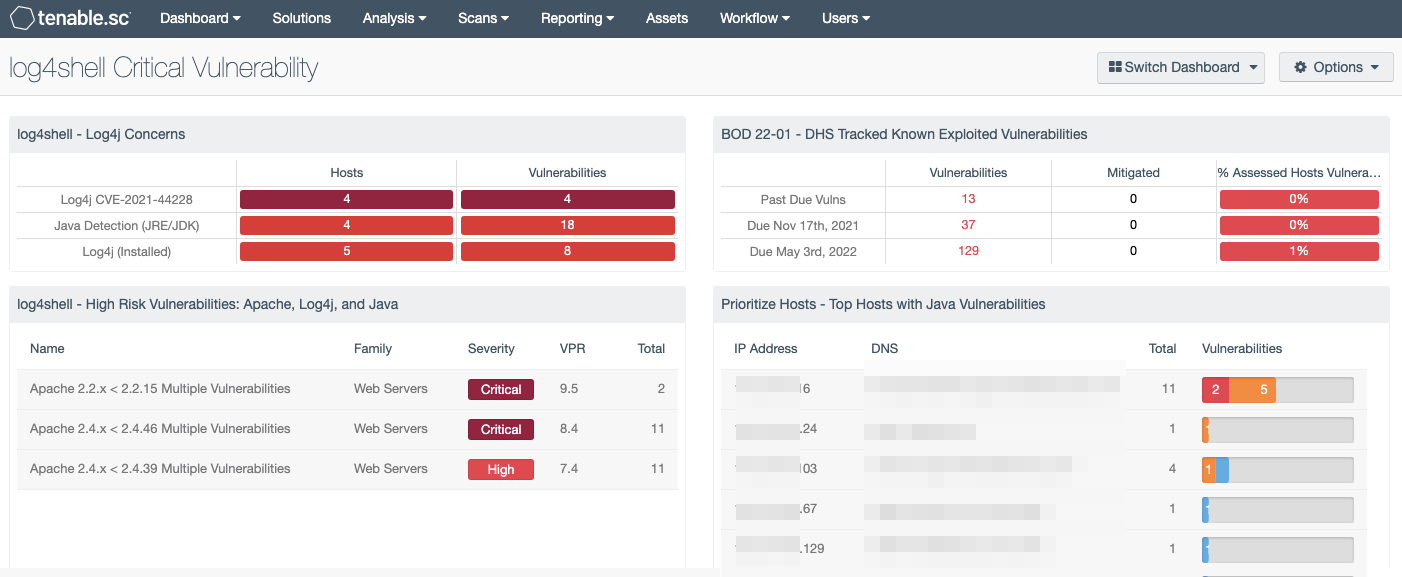
log4shell - Log4j Concerns: The log4shell - Log4j Concerns indicator matrix alerts organizations to potential concerns regarding the Log4j vulnerability.
log4shell - High Risk Vulnerabilities: Apache, Log4j, and Java: This table lists the critical vulnerabilities related to Apache, Log4j, and Java software as well as services detected in the environment.
BOD 22-01 - DHS Tracked Known Exploited Vulnerabilities: This component displays vulnerability status counts on past due vulns, vulns due Nov 17th 2021, and vulns due May 3rd 2021.
Prioritize Hosts - Top Hosts with Java Vulnerabilities: This table displays the top hosts on the network that have actively or passively detected Java vulnerabilities.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success