by Cody Dumont
April 10, 2014
This dashboard reports on the newly identified HeartBleed vulnerability. Using all the tools available to SecurityCenter users, Tenable has several methods of identifying vulnerable systems. As discussed by Tenable’s Ken Bechtel http://www.tenable.com/blog/beware-of-bleeding-hearts-updated the HeartBleed vulnerability is a serious issue that all IT professionals should be working to address. Fortunately for SecurityCenter customers, the identification of vulnerable systems just got easier.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Security Industry Trends.
The dashboard requirements are:
- SecurityCenter 4.8.0
- Nessus 5.2.6
- LCE 4.2.2
- PVS 4.0.2
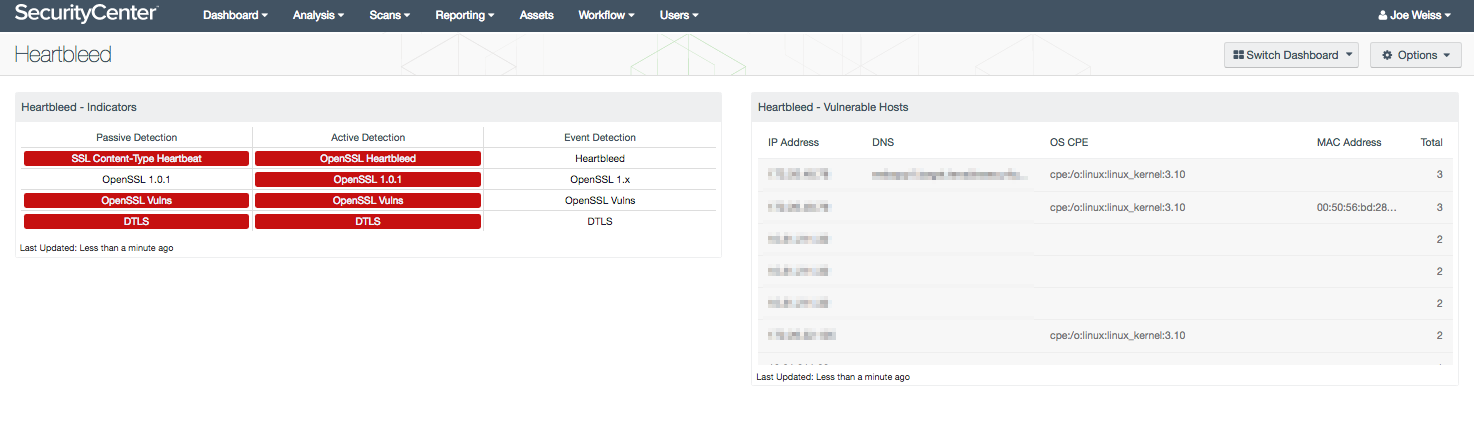
This dashboard is comprised of two components, which focus on vulnerabilities discovered by Nessus, PVS and LCE. The indicators matrix separates the discovery method and the vulnerabilities identified. The table component displays a list of known vulnerable hosts.
The components included with this dasboard are:
HeartBleed - Indicators
This component provides a series of indicators of systems that may be at risk to the HeartBleed vulnerability. The matrix is organized by column to provide indication of the identification method. Each row then displays indicators of vulnerabilities discovered.
The first row will turn red for systems that have been identified to have the HeartBleed vulnerability. The second row reports on the OpenSSL version 1.0.1 vulnerabilities, and will turn red if a system is discovered. The third row provides a listing for all OpenSSl vulnerabilities, while the fourth row provides the DTLS vulnerabilities. The indicators for the OpenSSL and DTLS will turn red for the active and passive detection, and will turn orange for the event detections. With event detections, the severity can not always be discovered, therefore many of the logs have a severity level of info. Thus, the indicators will be orange to indicate a warning and manual review and verification is required.
Heartbleed - Vulnerable Hosts
This component provides a table of systems that are at risk to the HeartBleed vulnerability. The table collects data from Nessus, LCE and PVS to identify vulnerable systems. The table is sorted by total vulnerabilities found on the system. Any systems in this table should be patched immediately.