by Ryan Seguin
Understanding and analyzing risk requires an easy to understand assessment method like the Common Vulnerability Scoring System (CVSS). Using the CVSS score is the preferred method of assigning a severity to a vulnerability, thus allowing Tenable.sc to quickly identify the most vulnerable hosts on your network. This dashboard maps clusters of targets by their total CVSS scores to more swiftly address the most dangerous machines first.
This dashboard focuses on the exploitability and remediation level metrics. The exploitability metric represents the current state of exploit techniques and availability of exploit code. As exploit code becomes easier to use and the number of attackers increase, the severity of the vulnerability will also increase. The remediation level of a vulnerability will factor into prioritization. When initially published, a vulnerability is unpatched. During the life cycle of the vulnerability, the remediation level will change through the respective stages. The higher risk is in direct proportion to the lesser the degree that a fix is official and permanent.
This dashboard effectively provides ease of identification for the most exploitable systems in the network. By providing a heat map of assets based on their total scores, this allows analysts and systems administrators to prioritize their approach towards vulnerability management.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- Tenable.sc 5.4.5
- Nessus 8.6.0
Tenable's Tenable.sc is the market-defining continuous network monitoring solution, which assists organizations in securing their internal network. Tenable.sc utilizes the CVSS scoring system for vulnerabilities; providing a uniform approach to vulnerability assessment, and Tenable.sc obtains information on environmental vulnerabilities through active scanning. Nessus Agents enable scanning and detection of vulnerabilities on transient and isolated devices. Tenable.sc provides an organization with the most comprehensive view of risks within the network and the intelligence needed to support effective vulnerability remediation efforts.
Components
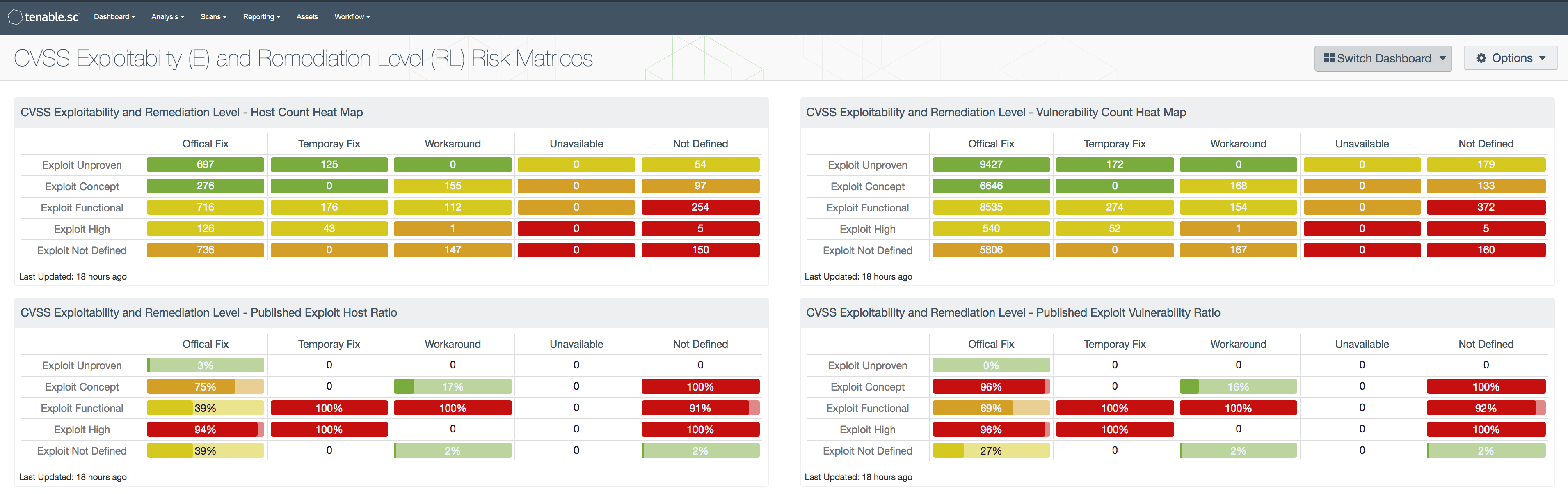
CVSS Exploitability and Remediation Level - Host Count Heat Map: This component displays a heat map of using the CVSS Temporal Exploitability and Remediation Level metrics. The number within each cell displays the IP Count, and when the user clicks on the cell, the IP summary will be displayed.
CVSS Exploitability and Remediation Level - Published Exploit Host Ratio: This component displays a table with the exploitable host ratio of each CVSS Temporal Exploitability and Remediation Level combination metric. The ratio within each cell displays the percentage of hosts with vulnerabilities with a published exploit, and when the user clicks on the cell, the IP summary will be displayed.
CVSS Exploitability and Remediation Level - Vulnerability Count Heat Map: This component displays a heat map of using the CVSS Temporal Exploitability and Remediation Level metrics. The number within each cell displays the IP Count, and when the user clicks on the cell, the vulnerability summary will be displayed.
CVSS Exploitability and Remediation Level - Published Exploit Vulnerability Ratio: This component displays a table with the exploitable vulnerability ratio of each CVSS Temporal Exploitability and Remediation Level combination metric. The ratio within each cell displays the percentage of vulnerabilities with a published exploit, and when the user clicks on the cell, the IP summary will be displayed.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success