by Cody Dumont
The Cybersecurity Maturity Model Certification (CMMC) was developed to create a framework to assess an organization's implementation of cybersecurity practices evenly across the defense industrial base. Using NIST 800-53 and NIST 800-171 as the baseline, the primary objective of CMMC is to consolidate the two security catalogs into a single measurable framework. Over the next 5 years, starting in June 2020, organizations that create Government off-the-shelf (GOTS) products, handle Federal Contract Information (FCI), or Controlled Unclassified Information (CUI) will need to show compliance at 1 of the 5 levels. Only Certified 3rd Party Assessment Organizations (C3PAO) will be able to certify an organization as compliant or not. Tenable.sc provides on-prem solutions for assessing Cyber Exposure practices and maps these practices to known assessment regulations such as NIST, CSF, and others. This dashboard showcases practices from:
- Asset Management (AM)
- Configuration Management (CM)
- Media Protection (MP)
- System & Information Integrity (SI)
The AM security domain contains activities that help identify assets on the network. AM.4.226: “Employ a capability to discover and identify systems with specific component attributes (e.g., firmware level, OS type) within your inventory” does apply until Level 4. If the security operations team is not aware of an asset, they will not be able to properly assess the risk nor identify any classified information on the asset. This dashboard provides components that identify asset counts based on detection method and groups them by subnet.
The CM domain begins at Level 2 when hardening policies must be defined. The use of a tool to detect hardening configurations works at all levels, and is a key feature in using Tenable.sc. The requirement “CM.2.061: Establish and maintain baseline configurations and inventories of organizational systems (including hardware, software, firmware, and documentation) throughout the respective system development life cycles” requires hardening standards to be defined. Many of the MP and SI requirements also tie back to hardening standards.
These standards are key to the success of the organization cyber security program and are easily located using the Defense Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs) or the Center for Internet Security (CIS) benchmarks. Either repository has well documented configuration standards and are supported by Tenable.sc using the audit files. If needed, audit files can be modified to an organization’s specific requirements. Additional information on how to edit audit files can be found within the “Nessus Compliance Checks” document in the Tenable Documentation Center.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.12.0
- Nessus 8.9.0
- Compliance Data
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess an organization’s adherence to best practice configuration baselines. Tenable.sc provides customers with a full and complete Cyber Exposure platform for completing an effective cybersecurity practices prescribed by CMMC standard.
Components
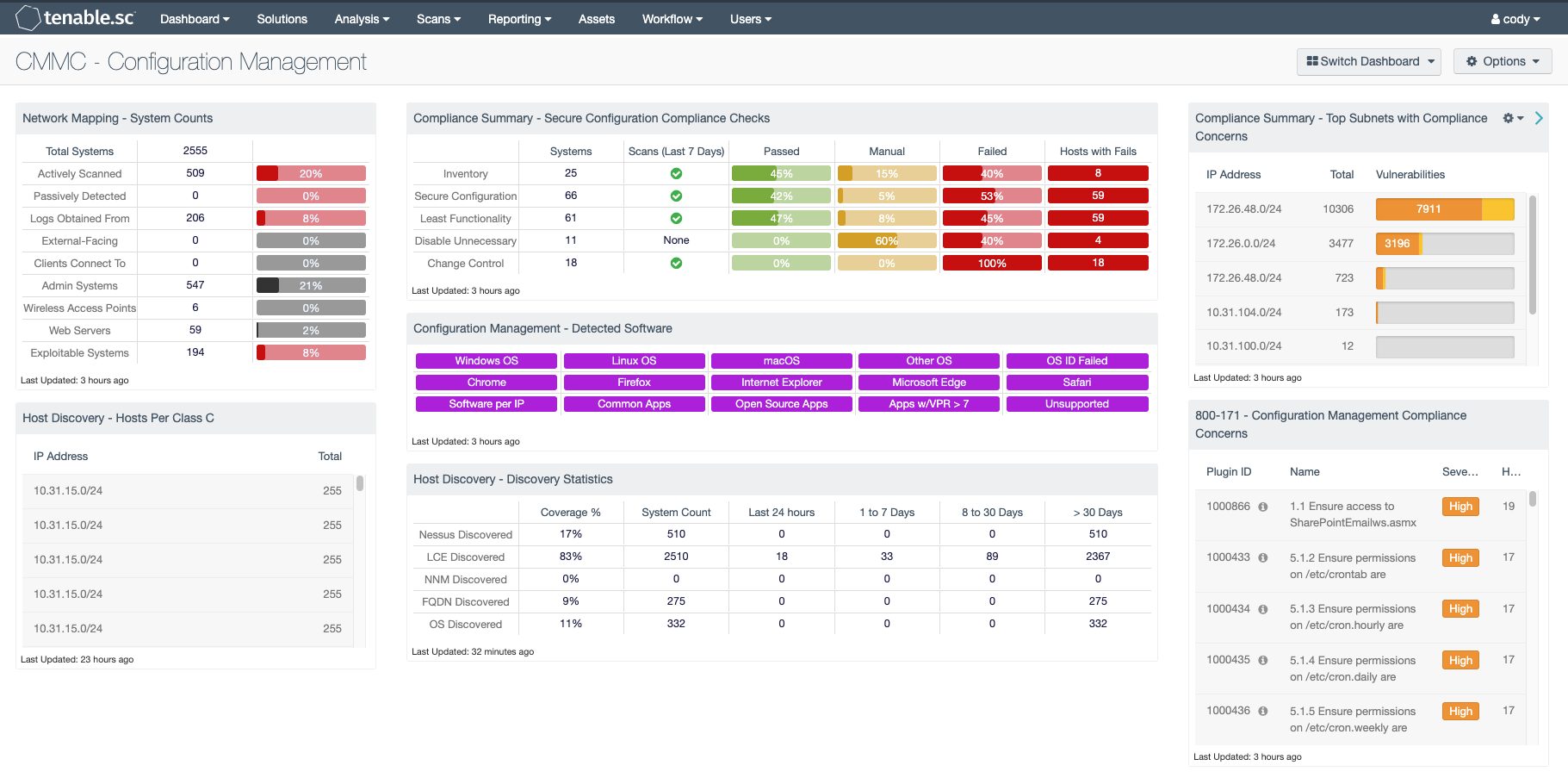
Network Mapping - System Counts: This component presents the counts of systems detected on the network in various categories. The total number of systems is displayed, along with the counts of actively scanned systems detected by Nessus, passively detected systems discovered by NNM, and systems from which LCE obtained logs. For these, percentages of the total system count are displayed. The percentage bar color reflects coverage and will be red for a low percentage of total systems, yellow for a medium percentage, and green for a high percentage. In addition, counts of external-facing systems, systems that clients connect to (servers), admin systems, wireless access points, and web servers are also displayed. For each of these, percentages of the total system count are displayed with black bars. Finally, the count of exploitable systems on the network is displayed, along with a percentage bar displayed in red. Using this matrix, organizations will be able to gain a more complete picture of existing assets and high-valued systems on the network.
Host Discovery - Hosts Per Class C: This table displays hosts detected across /24 network blocks using active scanning, passive listening and host data. The table is sorted by host count in descending order. Security teams can modify the component to report across /16 or /8 network blocks. The data in this table does not count against the SecurityCenter licensing.
Compliance Summary - Secure Configuration Compliance Checks: This component presents the results of compliance audits to verify the secure configuration of systems, including least functionality, disabling unnecessary services, and inventory and change control settings. Each row includes the system count, whether scans were performed in the last seven days, and the percentage of checks that passed, failed, or require manual verification. Passed checks are displayed in green, failed checks are in red, and checks that require manual verification are in orange. The count of hosts with failed checks is also given. Clicking on a highlighted indicator will bring up the vulnerability analysis screen to display details on the compliance checks and allow further investigation. In the vulnerability analysis screen, setting the tool to Vulnerability Detail List will display the full details on each compliance check, possibly including further information such as the expected and actual policy values and the specific sections of the various standards to which the compliance check relates.
Configuration Management - Detected Software: This matrix presents indicators for operating systems, browsers, unsupported, and other software installations on systems within a network. Indicators will turn purple when a match is found and will display a list of detected software. Analysts will find this information useful in tracking software licenses, and identify hosts running unauthorized or malicious software. Additionally, the data provided within this component can be used to monitor systems running unsupported software, which can contain vulnerabilities and place critical systems at risk. Filters within this component can be modified to include additional or specific software per organizational requirements.
Host Discovery - Discovery Statistics: This matrix provides a high-level historic view of when hosts were discovered. Each row depicts a different detection method and each column uses the Vulnerability First Discovered filter to identify when a plugin was first detected. The Vulnerability First Discovered field is set when a plugin, IP address and repository combination is first encountered. This value is reset when a vulnerability is moved from the mitigated database to the cumulative database. Analysts can use this table to gain an understanding of how and when devices are first detected. The data in this matrix does not count against the SecurityCenter licensing.
Compliance Summary - Top Subnets with Compliance Concerns: This table presents the top Class C subnets with the most compliance concerns. High severity indicates compliance failures, and medium severity indicates compliance advisories or checks that must be performed manually. The table is ordered so the subnet with the most compliance concerns is at the top. This information will help an analyst to identify which subnet needs the most attention in terms of compliance.
800-171 - Configuration Management Compliance Concerns: This table presents the top compliance concerns that specifically reference the NIST SP 800-171 Configuration Management family of requirements (section 3.4). High severity indicates compliance failures, and medium severity indicates compliance advisories or checks that must be performed manually. Each compliance concern also displays the number of hosts that the concern is found on. This information will help an analyst to determine the top NIST SP 800-171 configuration management compliance concerns that need to be addressed.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success