Tenable versus Rapid7
Four times as many customers choose Tenable over Rapid7.1
Why? Tenable’s proven accuracy, comprehensive coverage and unmatched support for your security needs.
See Tenable in action
Want to see how Tenable can help your team expose and close the priority cyber weaknesses that put your business at risk?
Complete this form to get a custom quote or demo.
Why customers choose Tenable over Rapid7
Compare Tenable to Rapid7
Overall asset coverage
Wide variety of assets: endpoints, network devices, operation technology (OT), identity systems, cloud workloads, web apps
Lacks coverage for operational technology (OT) devices, identity security systems and Azure AD
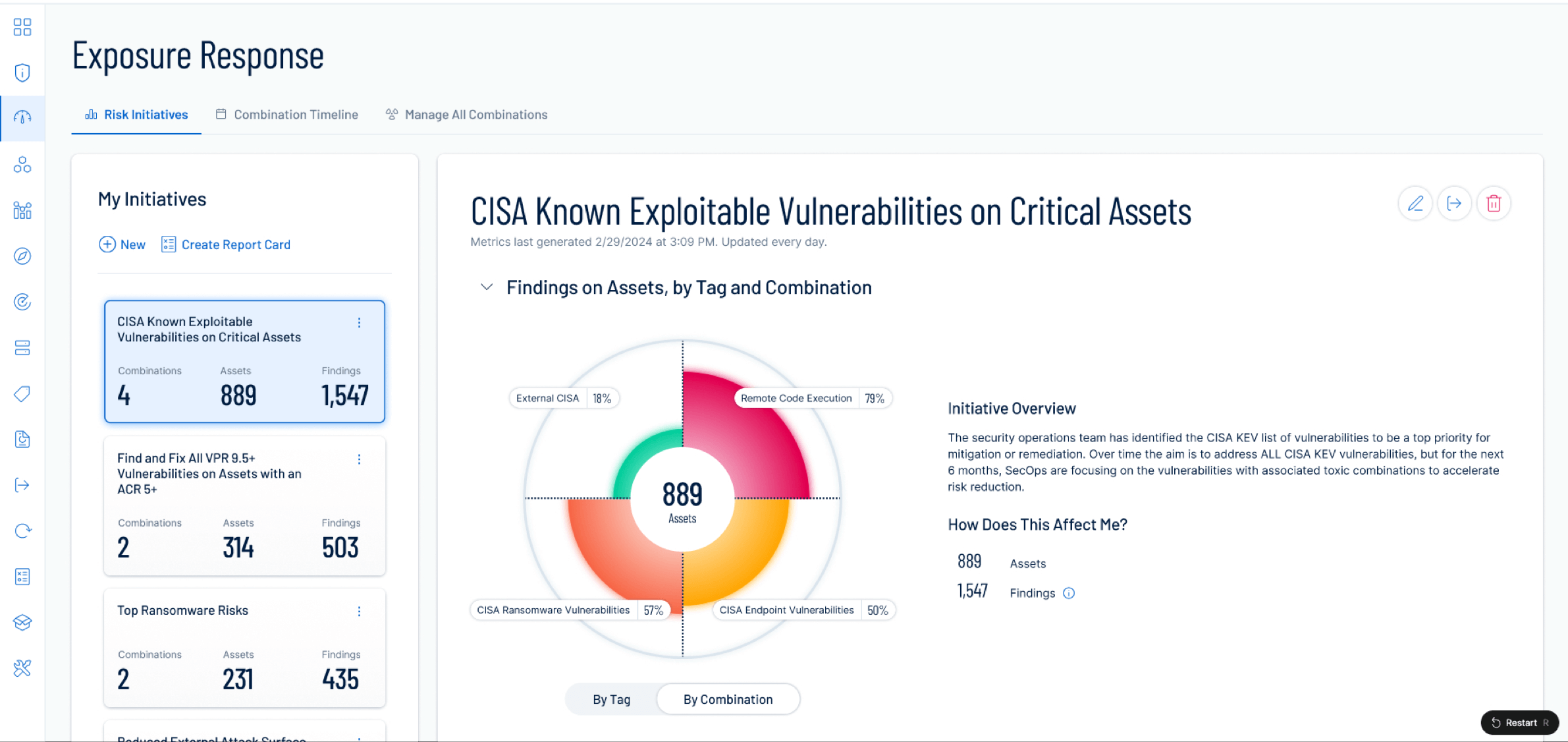
Exposure management analytics
Tenable One is an exposure management platform that combines integrated risk metrics across vulnerability management, web application security (WAS), cloud, identity, OT and attack surface management
Doesn’t offer OT and identity systems management.
Internal and peer benchmarking
Enables organizations to benchmark themselves internally and against industry peers
Not offered
Prioritization and asset criticality
Vulnerability priority rating (VPR) leverages threat, vulnerability and asset data to predict vulnerability exploitation risk
Confusing and non-intuitive asset criticality scores make it harder to prioritize critical vulnerabilities
Vulnerability intelligence
Provides rich vital context on any given vulnerability including the likelihood of exploitation and potential impact
Lacks a robust vulnerability database with enriched metadata and advanced search/filtering capabilities
On-prem and cloud coverage
Offers both on-prem (Tenable Security Center) and cloud (Tenable Vulnerability Management) options
Prioritizing cloud-based InsightVM over the on-prem Nexpose6
Partner ecosystem
100% committed to partners, 125 partners and 250 pre-built integrations
Rapid7 sunsetted integrations with BeyondTrust and doesn’t support popular tech like HashiCorp or HCL BigFix7
Patch management and remediation
Fully-fledged patch management integrated with Tenable Vulnerability Management, as well as integration with the leading third-party remediation tools
Not offered by Rapid7, limited support for third-party tools
Trust a leader
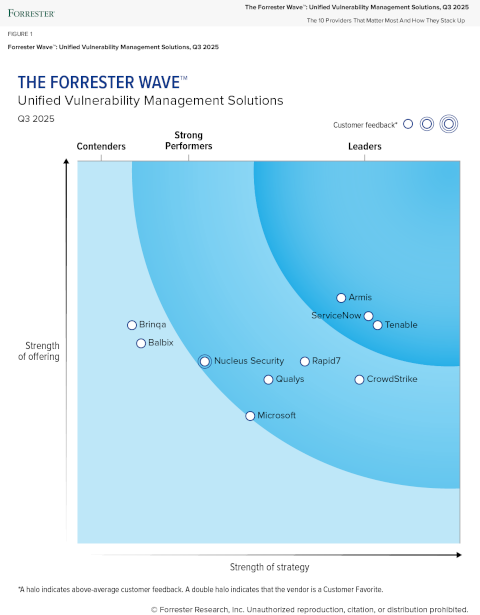
Tenable has been named a Leader in The Forrester Wave™: Unified Vulnerability Management, Q3 2025
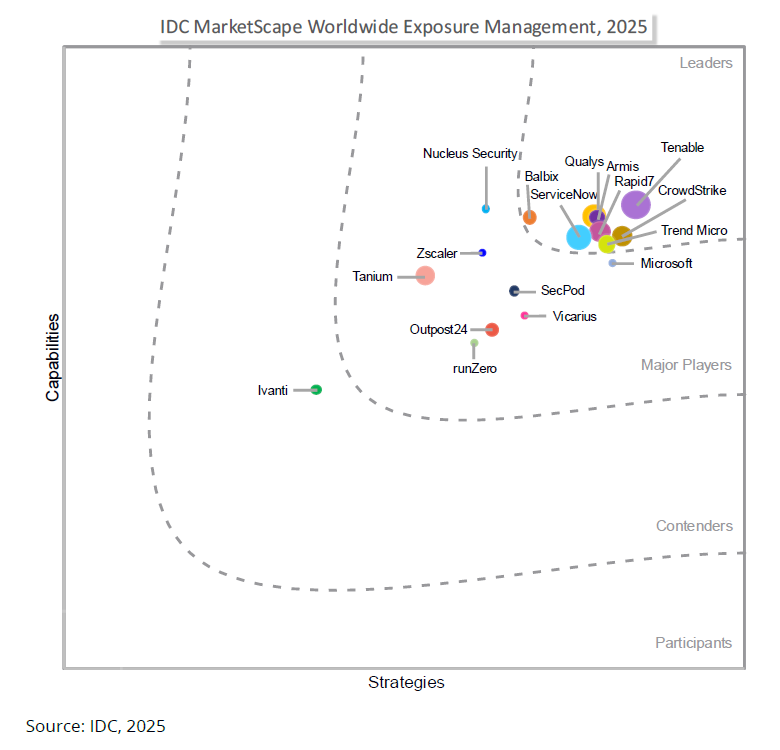
Read the reportTenable has been named a leader in the IDC MarketScape Worldwide Exposure Management 2025 Vendor Assessment
"Organizations should consider Tenable One when seeking a unified exposure management platform that delivers broad asset coverage across IT, cloud, OT/IoT, identity, and application environments."
Read the reportSee Tenable in action
Want to see how Tenable can help your team expose and close the priority cyber weaknesses that put your business at risk?
Complete this form to get a custom quote or demo.