Solorigate: SolarWinds Orion Platform Contained a Backdoor Since March 2020 (SUNBURST)

Nation-state threat actors breached the supply chain of a popular IT management software provider in order to infiltrate government agencies and private companies.
Update December 30: The Analysis, Solution and Identifying Affected Systems sections have been updated to reflect the discovery of and availability of patches for a separate threat affecting SolarWinds known as SUPERNOVA, which includes the exploitation of a newly disclosed vulnerability.
Background
On December 13, several news outlets, including Reuters, The Washington Post and The Wall Street Journal, reported that multiple U.S. government agencies were the victims of a significant breach reportedly linked to hackers associated with a nation-state. Additional reporting has since confirmed a direct connection between this breach and last week’s breach of cybersecurity firm FireEye.
According to a tweet from Dustin Volz, reporter for The Wall Street Journal, the source of the breach was “a flaw in IT firm SolarWinds.”
Russia has hacked several govt agencies including Treasury and Commerce as part of a widespread attack that also hit FireEye. They got in through a flaw in IT firm SolarWinds, which has 100s of thousands of customers, including military and Fortune 500.https://t.co/l6pC9vwvs6
— Dustin Volz (@dnvolz) December 13, 2020
Following the publication of these news articles, additional information about the breach has since been made public.
Kim Zetter, a cybersecurity and national security journalist, tweeted details from a Threat Analyst Report (TAR) published by Microsoft. Microsoft is one of the firms tapped to assist in the FireEye breach investigation. Microsoft nicknamed the attack “Solorigate.”
I have report from Microsoft about SolarWinds hack, including IoCs. Excerpts in this thread: "Microsoft security researchers recently discovered a sophisticated attack where an adversary inserted malicious code into a supply chain development process.... 1/
— Kim Zetter (@KimZetter) December 14, 2020
Additionally, FireEye has published a blog post providing a more detailed account regarding how the breach occurred, which includes a set of countermeasures that contains indicators of compromise (IOCs) such as a list of hashes, as well as Snort and YARA rules. FireEye refers to the backdoor as “SUNBURST.”
New Blog from us at FireEye: Writeup of UNC2452, a highly sophisticated attacker who distributed malware via a software supply chain attack. Blog contains descriptions of how it happened, what they do post compromise and suggested mitigations.https://t.co/0J7kzPt1ti
— Ben Read (@bread08) December 14, 2020
On December 14, SolarWinds filed a Form 8-K with the U.S. Securities and Exchange Commission that sheds light on the potential impact from this incident. In the 8-K, SolarWinds says it believes the number of customers with an active installation of Orion products containing this backdoor is “fewer than 18,000.”
Analysis
According to the Microsoft TAR and the FireEye blog post, a “highly sophisticated” adversary managed to breach the supply chain of SolarWinds, a company that develops IT infrastructure management software, resulting in the placement of malicious code inside of the company’s Orion Platform software builds.
The backdoor resides in a dynamic-link library (DLL) file name SolarWinds.Orion.Core.BusinessLayer.dll. The file was digitally signed by SolarWinds with a valid certificate on March 24, meaning it would be trusted by the underlying operating system and would not raise any alarms.
The backdoored DLL file was seeded as part of SolarWinds software builds between March and June 2020, which are accessible via the SolarWinds website. Once an organization installed the malicious software update, the backdoored DLL file would remain in hibernation for a period of two weeks before beginning its operation. This is one of the stealthy elements of this operation. FireEye says in its blog post that the backdoor also managed to “blend in with legitimate SolarWinds activity” in order to evade detection.
For a detailed teardown of the DLL file, including the associated IOCs and network activity, we strongly encourage you to read FireEye’s comprehensive blog post about the incident.
Reportedly, this operation has remained under the radar until last week. However, FireEye notes that the activity is “currently ongoing” and that it is “widespread, affecting public and private organizations around the world.”
While details have only just emerged, we encourage organizations using the SolarWinds Orion Platform to assume their networks have been compromised and activate existing incident response plans, work with your in-house information security teams or partner with an organization that conducts incident response to identify the impact to your organization.
SUPERNOVA: Second malware component discovered through SolarWinds breach
On December 18, Microsoft published a blog post analyzing the Solorigate malware. In their post, Microsoft mentioned the discovery of “an additional malware” that is “unrelated to” the original compromise via Solorigate. This additional malware is a “a small persistence backdoor in the form of a DLL file.” The DLL file, named App_Web_logoimagehandler.ashx.b6031896.dll, was reportedly created to “allow remote code execution through SolarWinds web application server.”
One day prior to Microsoft’s blog post, Palo Alto Networks’ Unit 42 team published a blog post about this additional malware component, which researchers are calling SUPERNOVA.
CVE-2020-10148: Authentication Bypass Flaw in SolarWinds Orion API
On December 26, the CERT Coordination Center (CERT/CC) published a vulnerability note for CVE-2020-10148, an authentication bypass vulnerability in the SolarWinds Orion API. According to CERT/CC, a remote attacker could exploit the vulnerability in order to execute API commands on the vulnerable Orion API instance. It is believed that this vulnerability was used to deploy the SUPERNOVA malware.
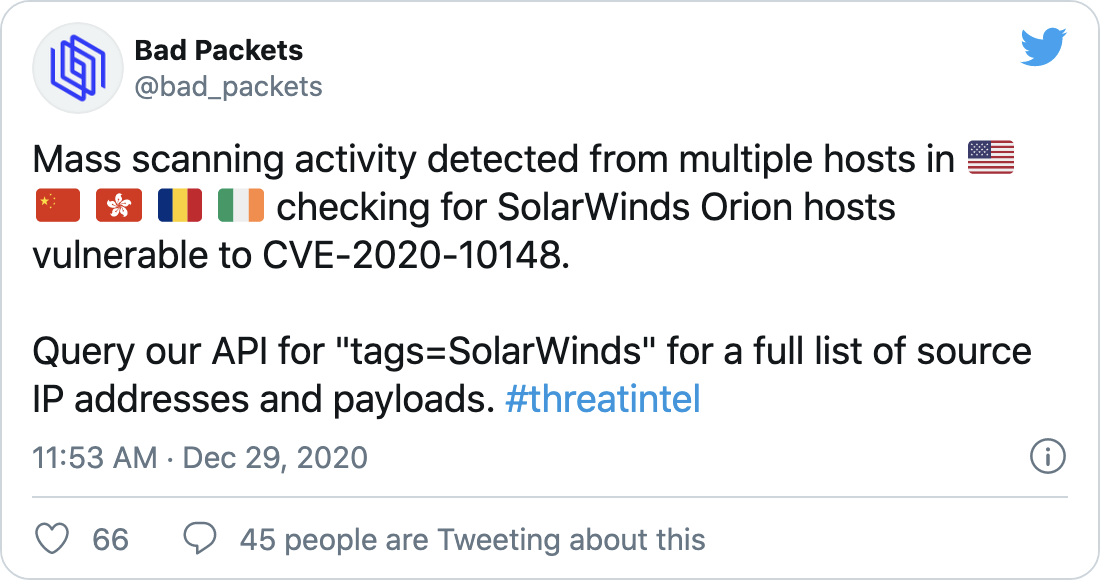
Reports of mass scanning for CVE-2020-10148 detected
On December 29, Troy Mursch, chief research officer at Bad Packets, tweeted that sensors have reportedly detected “mass scanning activity” for CVE-2020-10148 from hosts in the United States, China, Hong Kong, Romania and Ireland.
Solution
SolarWinds has published a security advisory regarding this incident. According to the company, the following build versions of its Orion Platform software are affected.
| Affected Versions | Release Date |
|---|---|
| 2019.4 HF 5 through 2020.2 with no hotfix | March 2020 through June 2020 |
| 2020.2 HF 1 | June 2020 through July 2020* |
* SolarWinds did not specify which versions of 2020.2 Hotfix 1 were affected, so we have provided the entire release date window for all versions of 2020.2 Hotfix 1.
SolarWinds specifically calls out the following products in its Orion Platform that are known to be affected:
- Application Centric Monitor (ACM)
- Database Performance Analyzer Integration Module (DPAIM)
- Enterprise Operations Console (EOC)
- High Availability (HA)
- IP Address Manager (IPAM)
- Log Analyzer (LA)
- Network Automation Manager (NAM)
- Network Configuration Manager (NCM)
- Network Operations Manager (NOM)
- Network Performance Monitor (NPM)
- Network Traffic Analyzer (NTA)
- Server & Application Monitor (SAM)
- Server Configuration Monitor (SCM)
- Storage Resource Monitor (SRM)
- User Device Tracker (UDT)
- Virtualization Manager (VMAN)
- VoIP & Network Quality Manager (VNQM)
- Web Performance Monitor (WPM)
Hotfix releases for the Orion Platform are now available and they reportedly address both Solorigate/SUNBURST and SUPERNOVA.
| Fixed Versions | Release Date |
|---|---|
| 2019.4.HF 6 | December 14, 2020 |
| 2020.2.1 HF 2 | December 15, 2020 |
Hotfix 2 (HF 2) replaced the compromised DLL component with the genuine DLL component as well as includes “several additional security enhancements.”
In addition to these hotfix releases, SolarWinds has also published patches explicitly for SUPERNOVA:
| SUPERNOVA Patch | Release Date |
|---|---|
| 2019.2 SUPERNOVA Patch | December 23, 2020 |
| 2018.4 SUPERNOVA Patch | December 23, 2020 |
| 2018.2 SUPERNOVA Patch | December 23, 2020 |
These fixes can be obtained from the SolarWinds customer portal.
For SUNBURST, if upgrading to the latest hotfix version is not feasible for your organization at this time, SolarWinds has provided a link to a document about securing the configuration for the Orion Platform.
FOR SUPERNOVA, if upgrading to the latest hotfix or applying the SUPERNOVA patches is not feasible for your organization at this time, SolarWinds has released a mitigation script that can “temporarily protect” your environment.
Additionally, the Cybersecurity and Infrastructure Security Agency (CISA) issued Emergency Directive 21-01 on December 13, which provides guidance to Federal Civilian Executive Branch agencies regarding this incident. On December 30, CISA updated the Emergency Directive with a second supplemental guidance ordering these agencies to update to the fixed versions of the Orion Platform by December 31.
Identifying affected systems
Tenable customers can utilize our existing detection plugin to identify all of the SolarWinds Orion assets in your environment.
Additionally, a version check plugin was released to help identify impacted versions of SolarWinds in your environment. We have also released a local, agent compatible detection plugin.
Finally, an additional version check plugin has been released for customers to identify systems vulnerable to the CVE-2020-10148 that was reportedly used to deploy the SUPERNOVA malware.
Get more information
- SolarWinds Security Advisory for Orion Platform Backdoor
- FireEye Blog Post about SUNBURST Backdoor in SolarWinds Orion Platform
- CISA Emergency Directive 21-01 for SolarWinds Orion Platform Backdoor
- Reuters Story about U.S. Treasury Department and NTIA Breach
- New York Times article about FireEye Breach
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Government
- Threat Intelligence
- Threat Management
- Vulnerability Management
- Vulnerability Scanning




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success