Nessus Leverages Threat Intelligence from ThreatGRID
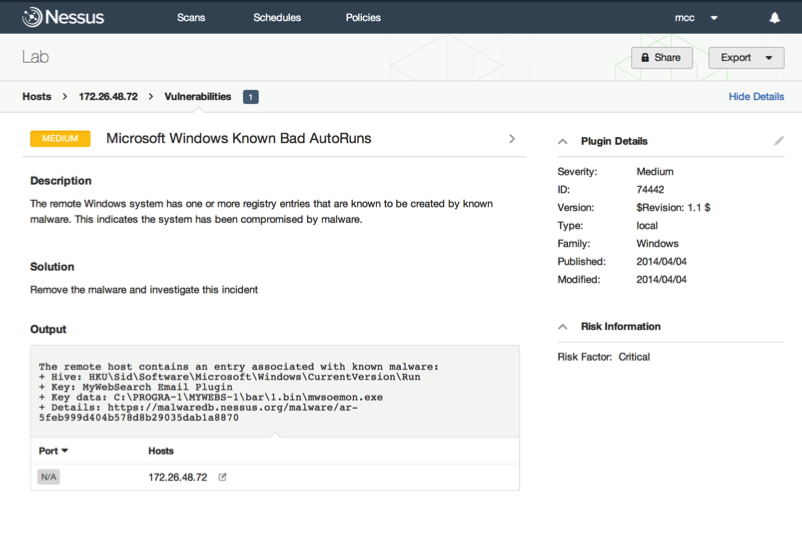
Tenable released a new Nessus® plugin – Microsoft Windows Known Bad AutoRuns (Plugin id 74442), which detects the presence of advanced malware on endpoints based on threat intelligence from ThreatGRID. The threat intelligence includes Scheduled Tasks, AutoRuns, and other Windows Registry entries that Nessus® collects while scanning endpoints and cross-references with data from the ThreatGRID feed.
Global Threat Intelligence
ThreatGRID combines advanced malware analysis with deep threat analytics and content to empower security teams to proactively defend against attacks and malware outbreaks. ThreatGRID analyzes millions of malware samples a month, harvested globally and generating terabytes of rich, actionable content every day, to provide customers unmatched scale and coverage from global threats.
Advanced Malware Detection Using Tenable Nessus® and ThreatGRID
This joint solution provides the following customer benefits.
Ability to Detect Persistent Malware
This solution allows customers to find systems that have been infected by malware, even when the malware is dormant (not running) during the time of audit.
Improved Quality of Malware Detection
Customers gain continuous real-time threat intelligence enriched by global and historical context. Nessus leverages this threat feed to improve the quality of detection of new forms of malware, beyond file signature hashes.
Conclusion
The addition of global threat intelligence from ThreatGRID gives the Tenable Network Security Products detections of malicious software that has not been classified or identified by traditional anti-malware solutions. The fact that this feed is updated frequently allows us to improve zero-day malware detection across all endpoints in a customer’s enterprise without updating any software on every endpoint. By including this additional data we are confident in providing network security staff increased security and comfort knowing that if anything slips past their dedicated anti-malware solution, they have a quality service providing a double check.
Learn more
- Malware
- Nessus
- Plugins
- Threat Intelligence



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success