Cybersecurity Snapshot: 6 Things That Matter Right Now

Topics that are top of mind for the week ending Sept. 2 | Shift-left efforts falling short. What CISOs earn and what stresses them out. The quantum computing risk for critical infrastructure. Securing machine learning systems. And much more!
1 – Shift left: Still a work in progress
Shifting security left – meaning, starting security checks earlier in the software development process – has been widely hailed. But, as a new study shows, adoption of “shift left” practices is falling short.
In the study “Software Security During Modern Code Review: The Developer’s Perspective,” University of Zurich researchers interviewed 10 developers and polled another 182 online, and found:
- Developers acknowledge the importance of security code reviews, and view it as their responsibility, but it’s not top of mind for them.
- Most companies expect developers to do security code reviews, but many don’t provide them with security training.
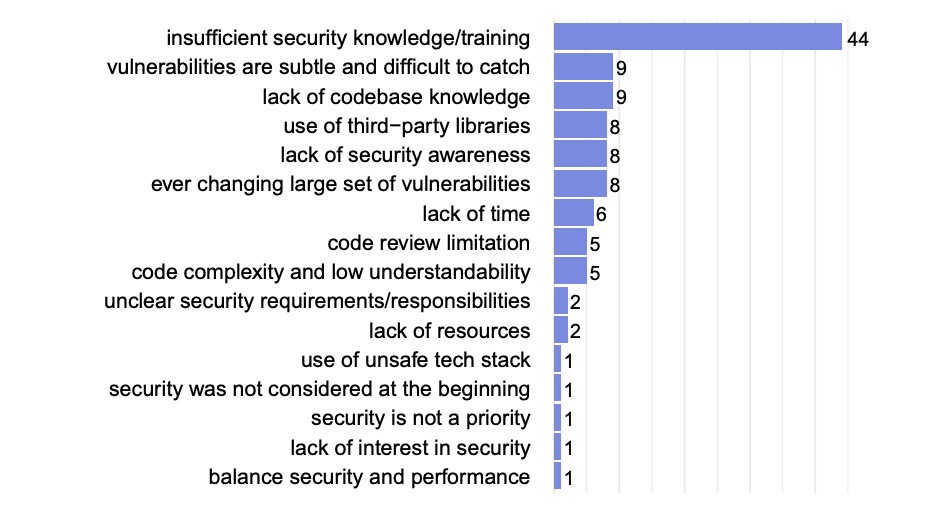
- Developers rank a lack of security training and knowledge as their main security-related challenge.
- Developers are often unclear on who’s responsible for what regarding application security, and thus they may neglect doing their part.
- They report struggling with assessing the security of third-party software libraries and the security of the interaction between app code components.
Challenges developers face concerning security during code reviews
The researchers recommend that companies do a better job of educating developers about security and of motivating them to review code by providing incentives and recognition.
More information:
- “A Practical Approach for Shifting Left” (Tenable)
- “What is shift left testing?” (TechTarget)
- “Shift Left: Where Cloud Native Computing Security Is Going” (The New Stack)
- “Shifting security left requires a GitOps approach” (TechTarget)
- “OpenSSF director warns over secure development” (The Stack)
2 – All you ever wanted to know about CISOs in 2022
How much do CISOs earn? Which career paths do they take to become a CISO? How long do they stay at their jobs? What keeps them up at night?
You can find answers to those – and many more – questions in the “2022 Global Chief Information Security Officer (CISO) Survey” from executive search firm Heidrick & Struggles.
Key findings from the survey, which polled 327 CISOs from the U.S., Europe and Asia-Pacific:
- Regarding the most significant threats facing their organizations, most respondents included ransomware (67%), followed by insider threats (32%), nation/state attacks (31%) and malware attacks (21%.)
- CISOs’ team size grew compared with last year, reflecting the increasing investment in cybersecurity by organizations.
- CISOs have broad visibility with their board of directors, with 88% saying they present to either the full board or to a board committee.
- Median cash compensation for CISOs in the U.S. rose to $584,000 from $509,000 in 2021. Total compensation, including equity grants and other incentives, increased to $971,000 from $936,000.
- Regarding tenure length, 77% of respondents have been at their current job for at least three years, up from 56% of respondents in 2021’s survey.
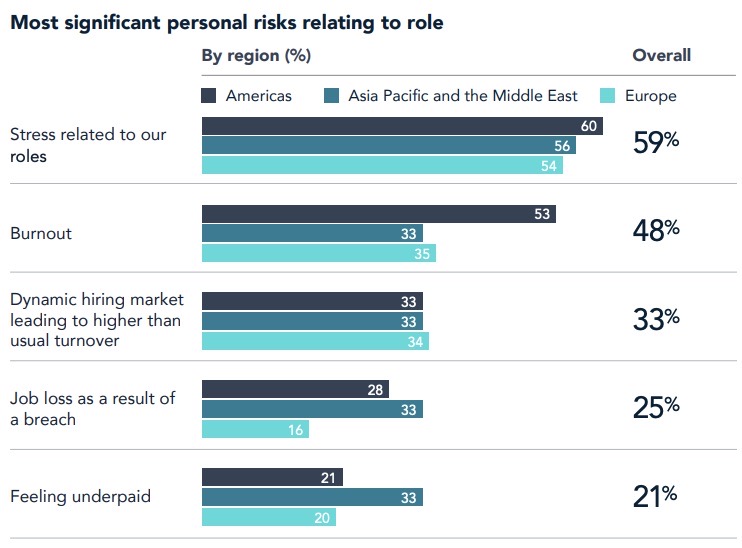
- When asked about “personal risks,” CISOs ranked stress at the top (59%), followed by burnout and by higher-than-usual staff turnover
More information:
- “Cybersecurity on the board: How the CISO role is evolving for a new era” (TechMonitor)
- “7 best reasons to be a CISO” (CSO)
- “Effective Board Communication for CISOs” (CISO Street)
- “7 mistakes CISOs make when presenting to the board” (CSO)
3 – Guidance for securing ML and AI systems
Machine learning (ML) and artificial intelligence (AI) have become ubiquitous across all types of applications, which makes them an attractive target for cybercriminals – and creates a need for security teams to protect these systems.
The latest guidance for combatting “adversarial machine learning” attacks comes from the U.K.’s National Cyber Security Centre (NCSC), which has just published a set of security principles for systems that have ML technology.
As an NCSC data science researcher explains in a blog post, to test software for vulnerabilities and weaknesses, one must understand how it works, but this is often difficult with ML, for a variety of reasons.
In its guidance, the NCSC addresses critical ML weaknesses and challenges; the differences between ML security and standard cybersecurity; and its development of specific security principles.
More information:
- “What is Adversarial Machine Learning?” (Towards Data Science)
- “Adversarial machine learning explained” (CSO)
- “5G networks vulnerable to adversarial ML attacks” (TechTarget)
- “Data-tampering attacks are hard to detect” (Protocol)
- “How to protect your ML models against adversarial attacks” (The Next Web)
4 – Struggling to fill IT, cybersecurity jobs? Look for non-tech candidates
The shortage of IT workers remains a global problem, and is particularly pronounced in cybersecurity, so what’s a hiring manager to do? A popular suggestion is to consider candidates without tech experience. A new article from McKinsey & Co. backs it up as a good idea.
Titled “Overcoming the fear factor in hiring tech talent,” it’s based on an analysis of anonymized online work histories of about 280,000 tech pros. Here’s a stat that jumps out: 44% transitioned to IT from non-IT occupations. And almost three in five U.S. IT managers started in non-IT roles.
Other interesting findings about these IT pros:
- 70% started in professional services, healthcare or other science, technology, engineering and mathematics (STEM) fields.
- Common first IT roles included app developer, IT support and document manager.
- They show a stronger ability to acquire new IT skills than their IT “lifer” counterparts.
- They tend to move quickly up the ladder to more specialized, sophisticated roles in areas like cybersecurity.
Recommendations for finding good candidates include:
- Look for motivated candidates within your own organization.
- Make bold hiring decisions and consider “soft skills” like:
- Analytical mind
- Attention to detail
- Problem solving ability
- Adaptability
- Communication skills
- Don’t rule out mid-career workers who are eager for a change.
- Once they’re in IT, provide them with plenty of training and education.
More information:
- “Companies are desperate for cybersecurity workers” (Fortune)
- “Cybersecurity skills gap: Why it exists and how to address it” (TechTarget)
- “Cybersecurity teams need to fill jobs. They’ll need entry-level roles.” (Protocol)
- “What Can Be Done to Overcome Cybersecurity Staff Shortage?” (Bank Infosecurity)
- “Hiring entry-level and junior candidates can alleviate the cybersecurity skills shortage” (TechRepublic)
5 – CISA: Critical infrastructure must prep for quantum computing threat
Here’s a heads up for critical infrastructure organizations: Quantum computing is coming and you should start preparing for its cybersecurity risk now.
What’s the problem? When they become available, possibly around 2030, powerful quantum computers will break existing public-key cryptographic algorithms, which would create a global data-privacy and security disaster.
Consequently, the U.S. government is trying to get the country ready. For example, “quantum resistant” cryptographic algorithms are being developed, an effort slated for completion in 2024 with the release of a new standard.
The government is also providing guidance to cybersecurity teams, as we’ve explained in this blog. However, critical infrastructure faces particularly complex challenges, so the Cybersecurity and Infrastructure Security Agency (CISA) recently issued a guide for this sector.

Here are some key takeaways:
- Among the 55 national critical infrastructure functions provided by government and businesses, these four will offer foundational support via products, patches and software:
- Providers of online content and communication services
- Providers of identity management services
- IT providers
- Protectors of sensitive information
- Because their hardware is geographically dispersed and has a long replacement lifecycle, organizations with industrial control systems (ICS) should factor quantum-computing risks into new hardware purchases.
- NCF providers that store confidential data long-term must prevent “catch and exploit” attacks, in which hackers try to steal this data and decrypt it once quantum computers are available.
CISA also reiterated the importance of taking steps now, like inventorying the systems and applications that use public-key cryptography, as well as the most critical data to be secured long-term.
More information:
- “Quantum apocalypse: Experts warn of ‘store now, decrypt later’ hacks” (Silicon Republic)
- “CISA Warns Critical Infrastructure to Prepare for Mass Post-Quantum Systems Migration” (NextGov)
- “A Peek Into CISA's Post-Quantum Cryptography Roadmap” (Dark Reading)
- “CISA Releases Guidelines to Aid Companies Transition to Post-quantum Cryptography” (Infosecurity Magazine)
6 – Quick takes
Here’s a roundup of vulnerabilities, trends, news and incidents to put on your radar screen.
- Microsoft is warning about a malware called MagicWeb, “a malicious DLL that allows manipulation of the claims passed in tokens generated by an Active Directory Federated Services (AD FS) server.” MagicWeb is being used by the Nobelium APT – of SolarWinds fame – to maintain persistent access to compromised environments. More information and analysis from Redmond Magazine, ZDNet and Dark Reading.
- Ransomware attacks surged 47% in July compared with June, with the new Lockbit 3.0 variant accounting for most of the attacks (52), according to NCC Group.
- LastPass, provider of a popular password manager app, disclosed that an intruder accessed parts of its dev environment and stole portions of source code, but said no customer data was compromised.
- Google has disclosed multiple vulnerabilities in Chrome, and the most severe could lead to arbitrary code execution.
- Wordpress is recommending users update to the latest version because it patches three security issues, including a SQL injection bug.
- Google has launched a bug bounty program specifically for vulnerabilities found in any of its open source projects.
- Atlassian warned about a critical severity vulnerability in BitBucket Server and Data Center 7.0.
Learn more
- Cybersecurity Snapshot
- Government
- OT Security




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success