Cyber Risk Management in Transition: Key Findings from ESG’s Cyber Risk Management Survey

A recent ESG report shows the traditional approach to cyber risk management isn’t working anymore, if in fact it ever did. Here, we share four highlights from the report and offer two steps to help improve your organization’s strategy.
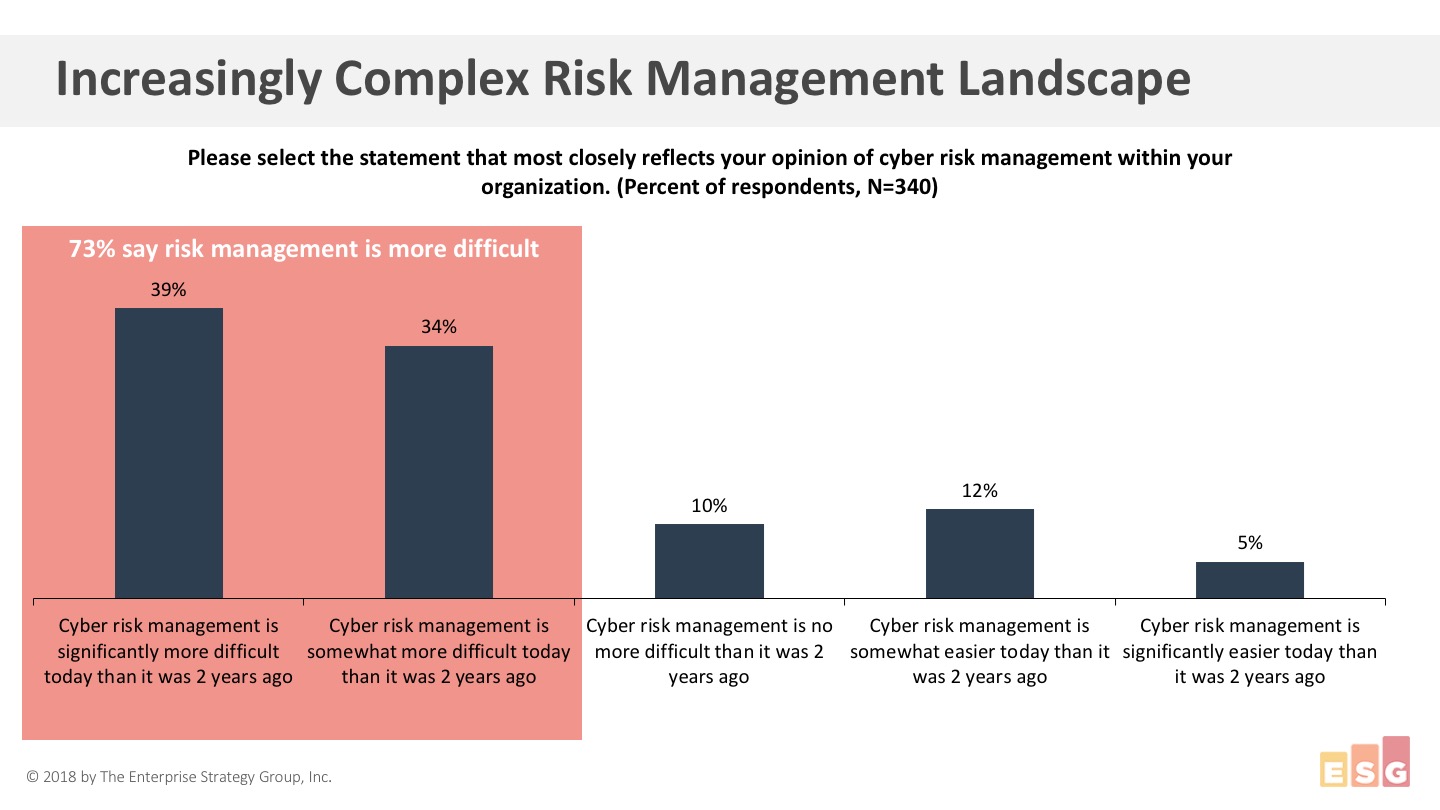
To gain insight into how cyber risk management is changing to support organizational missions and initiatives, the Enterprise Strategy Group (ESG) surveyed 340 information security professionals in organizations with over 1,000 employees.
The results show the traditional approach to cyber risk management isn’t working anymore, if in fact it ever did. The vast majority of respondents (72%) state that cyber risk management is more difficult than it was two years ago. Only 5% say it’s significantly easier than it used to be. It’s clear a new way to deal with the flood of vulnerabilities is required. (Watch the video below for a quick synopsis of the findings from ESG's senior principal analyst, Jon Oltsik.)
Top 4 findings from ESG’s Cyber Risk Management Survey
Here are four highlights from the survey results:
- This was never easy and it keeps getting worse. Cyber risk management is becoming increasingly important – as it tracks to a growing attack surface and an overwhelming number of vulnerabilities.
- What we have here is a failure to communicate. Organizations are finding it difficult to align cyber risk management with business goals. What the C-suite needs and what security can provide are not in sync. There’s a real language barrier. Security must translate technical jargon into terms everyone can understand and utilize for their own decision processes.
- It’s time for a change. All too often, vulnerability management is dependent upon antiquated processes and practices. Spreadsheets and intuition aren’t cutting it.
- What you can’t see CAN hurt you. Clear visibility and knowledge across the entire attack surface is essential. But business pressures are causing organizations to have an ever-expanding attack surface as cloud technologies gain ground and operational technology (OT) devices are integrated with the IT infrastructure.
Why cyber risk management is getting harder – and what you can do about it
As for what’s making things more difficult, the challenges are coming from all sides. There’s a daunting combination of more vulnerabilities, greater business pressure and, last but not least, more advanced adversaries.
Here’s what ESG survey respondents say they are facing in their environments:
- 43%: More workloads to public cloud infrastructure services
- 42%: More software vulnerabilities
- 42%: More advanced adversaries
- 41%: More sensitive data
- 30%: More exec-level analysis and reporting requirements
So, what can a beleaguered infosec professional do?
Step 1: Continuous visibility
Only 38% of ESG survey respondents continuously scan their environments. This results in blind spots and gives attackers a leg up on discovering your vulnerabilities. Instituting continuous visibility is your first line of defense.
Step 2: Prioritization of vulnerabilities
The volume of vulnerabilities is overwhelming for 70% of respondents. But only a small fraction of vulnerabilities are ever exploited. The key is finding the dangerous needles in your ever-growing haystack of vulnerabilities. And to do that you need insight into threat intelligence and a model that can help predict which of your vulnerabilities are most likely to be attacked. Prioritizing vulnerabilities based on a predictive model will improve your team’s ability to respond quickly and efficiently to the most critical threats to your business.
Learn more
- View the webinar with ESG analyst Jon Oltsik now
- Download the executive summary: What’s the Answer to the Vulnerability Overload Problem? Key Findings from ESG’s Cyber Risk Management Survey
- Read the eBook: How to Prioritize Cybersecurity Risks: A Primer for CISOs
- Vulnerability Management


