CVE-2023-41064, CVE-2023-4863, CVE-2023-5129: Frequently Asked Questions for ImageIO and WebP/libwebp Zero-Day Vulnerabilities
Frequently asked questions relating to vulnerabilities in Apple, Google and the open source libwebp library.
Background
The Tenable Security Response Team has put together this blog to answer frequently asked questions (FAQ) to help provide clarity around recently disclosed vulnerabilities including CVE-2023-41064, CVE-2023-4863 and CVE-2023-5129 in an open source library called libwebp.
FAQ
What do these vulnerabilities have to do with Apple products?
On September 7, researchers at Citizen Lab published a blog post detailing their discovery of an iPhone zero-click, zero-day exploit chain in Apple iOS used to deploy a spyware known as Pegasus.
NEW: Last week, we @citizenlab captured a "zero-click" exploit used to install Pegasus on the latest version of iOS, 16.6. The exploit installed Pegasus without any interaction from the victim, and was virtually invisible https://t.co/MxPrAThwa1
— Bill Marczak (@billmarczak) September 7, 2023
What are the vulnerabilities that Apple patched?
Apple patched two vulnerabilities across several of its operating systems, including iOS and iPadOS [1, 2], watchOS and several versions of macOS [1, 2, 3]:
| CVE | Description |
|---|---|
| CVE-2023-41064 | ImageIO Buffer Overflow vulnerability |
| CVE-2023-41061 | Wallet Validation Issue |
What is this exploit chain called and how severe is it?
The Citizen Lab dubbed this exploit chain BLASTPASS and it is considered a critical flaw because exploitation requires no interaction from a potential victim, making it a zero-click vulnerability.
In-the-wild exploitation involved attachments using Apple PassKit that contained malicious images delivered to the victim via iMessage.
What does this have to do with Google Chrome and other web browsers?
As part of the disclosure of these vulnerabilities, both Apple’s Security Engineering and Architecture (SEAR) team and The Citizen Lab notified Google about their findings on September 6 due to the potential for exploitation outside of Apple’s ecosystem.
Did Google also patch this vulnerability?
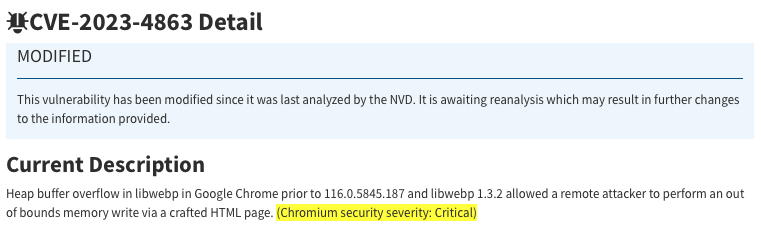
Yes, on September 11, Google published a patch for Google Chrome. However, they assigned a separate CVE for this vulnerability:
| CVE | Description |
|---|---|
| CVE-2023-4863 | Heap Buffer Overflow Vulnerability in WebP |
What is ImageIO or Image I/O?
ImageIO or Image I/O is a framework that allows programs to read and write image file formats, including WebP. It is a part of Apple operating systems from iOS and iPadOS to macOS, and watchOS.
What is WebP or libwebp?
WebP is an open-source image file format developed by Google, while libwebp is a library that was developed to allow programs to support the WebP file format. It is part of Google’s Chromium project, the open source web browser that Google Chrome and other browsers are based on.
How are CVE-2023-4863 and CVE-2023-41064 connected?
Based on the timeline of when CVE-2023-41064 was disclosed (September 7) and both Apple and The Citizen Lab’s proactive disclosure to Google on September 6, coupled with the fact that both issues are buffer overflow vulnerabilities in image processing frameworks/libraries (ImageIO, WebP), it would appear that both vulnerabilities are related. This is also corroborated by other independent research from Matt Suiche and Ben Hawkes.
We suspect that this is the same bug that Citizen Lab reported to Apple after detecting an NSO Group exploit chain called "BLASTPASS" that was used to attack on a Washington DC-based civil society organization.
— Ben Hawkes (@benhawkes) September 21, 2023
If this affects the libwebp library, does that mean other programs are also vulnerable?
Yes, applications or programs and operating systems that use libwebp as a dependency are also considered vulnerable to these flaws.
What does CVE-2023-5129 have to do with this?
On September 25, Google assigned a new CVE, CVE-2023-5129, to expand the impact of CVE-2023-4863, to cover libwebp more broadly versus specifically impacting Google Chrome.
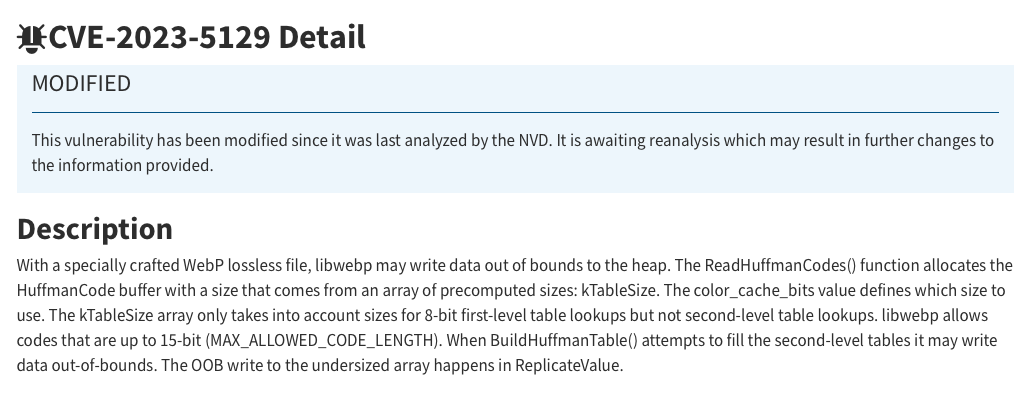
Google also assigned a maximum CVSSv3 score of 10.0 for this CVE.
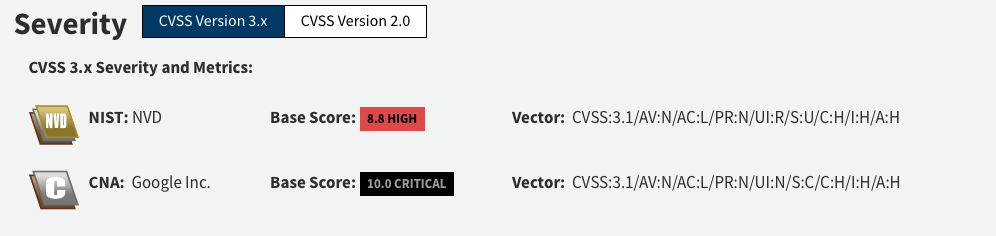
Did Google reject CVE-2023-5129 after assigning it?
Yes, on September 27, Google rejected CVE-2023-5129, citing it as a duplicate of CVE-2023-4863 and updated the description for CVE-2023-4863 to include the impact to libwebp itself while clarifying the critical impact to Chromium.
Google did not increase the CVSSv3 score for CVE-2023-4863, opting instead to add a note about it being of “Critical” per Chromium security’s severity scale.
Why was CVE-2023-5129 rejected?
Google has not confirmed why it rejected the vulnerability. However, based on the fact that several vendors have already adopted CVE-2023-4863 as the CVE identifier when patching libwebp, it likely did not make sense to assign a new CVE for this versus expanding the impact of the original CVE.
How many applications or programs are affected by CVE-2023-4863?
Because libwebp is a library that is included in applications and programs or packages as a dependency, we do not know the full depth and breadth of how widespread it is. We know that several browsers, including Firefox and Thunderbirdas well as browsers based on Chromium including Microsoft Edge, Opera and Brave are affected by this vulnerability. Additionally, the library is included in the Electron open source framework that is used by a large number of applications including 1Password, Slack and more.
A list of affected Electron applications is being tracked by Michael Taggart here.
Timeline
The following is a timeline related to all three vulnerabilities highlighted in this FAQ. It was last updated on September 27.
| Date | Details |
|---|---|
| September 6, 2023 | Apple Security Engineering and Architecture (SEAR) and The Citizen Lab notifies Google about a critical vulnerability in the WebP library (libwebp) |
| September 7, 2023 | The Citizen Lab publishes blog post detailing discovery of zero-click, zero-day exploit chain against iPhones dubbed BLASTPASS |
| Apple publishes patches for several operating systems including iOS and iPadOS, watchOS and macOS to address the flaws disclosed by The Citizen Lab | |
| Apple assigns CVE-2023-41064 (ImageIO), CVE-2023-41061 (Wallet) for the exploit chain | |
| September 11, 2023 | Google publishes a Stable Channel Update for Desktop versions of Chrome on Mac, Linux and Windows to address the vulnerability disclosed on September 6. |
| Google assigns CVE-2023-4863 to address the impact of this vulnerability in WebP in Chromium | |
| Apple publishes a patch for previous versions of iOS and iPadOS as well as macOS Big Sur and Monterey | |
| September 25, 2023 | Google assigns CVE-2023-5129 to expand impact of this vulnerability to libwebp |
| September 27, 2023 | Google rejects CVE-2023-5129, marking it as a duplicate of CVE-2023-4863 |
| Google modifies the entry for CVE-2023-4863 to highlight impact to both Google Chrome and libwebp |
Identifying affected systems
A list of Tenable plugins to identify affected systems can be located on the individual CVE page for each of the CVEs mentioned here:
| CVE Plugins Page | Description |
|---|---|
| CVE-2023-4863 | Heap Buffer Overflow in WebP |
| CVE-2023-41064 | Buffer Overflow in Image I/O |
| CVE-2023-41061 | Validation Issue in Wallet |
These links will display all available plugins for these vulnerabilities, including upcoming plugins in our Plugins Pipeline.
Get more information
- BLASTPASS: NSO Group iPhone Zero-Click, Zero-Day Exploit Captured in the Wild
- About the security content of iOS 16.6.1 and iPadOS 16.6.1
- Google Chrome: Stable Channel Update for Desktop
- Google quietly corrects previously submitted disclosure for critical webp 0-day
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Exposure Management
- Vulnerability Management


