CVE-2020-5135: Critical SonicWall VPN Portal Stack-based Buffer Overflow Vulnerability
Researchers disclose a critical pre-authentication vulnerability in the SonicWall VPN Portal that is easily exploitable.
Background
On October 12, SonicWall published a security advisory (SNWLID-2020-0010) to address a critical vulnerability in SonicOS that could lead to remote code execution (RCE). The vulnerability was discovered by security researchers at Tripwire’s Vulnerability and Exposure Research Team (VERT).
Analysis
CVE-2020-5135 is a stack-based buffer overflow vulnerability in the VPN Portal of SonicWall’s Network Security Appliance. A remote, unauthenticated attacker could exploit the vulnerability by sending a specially crafted HTTP request with a custom protocol handler to a vulnerable device. At a minimum, successful exploitation would result in a denial of service condition against the exploited device, exhausting its resources.
Remote code execution “likely feasible” but not without additional footwork
The researchers added that they were able to “divert execution flow through stack corruption” which means achieving RCE is “likely feasible.” In an interview with Threatpost, Craig Young of VERT noted that to gain RCE, an attacker would also need “an information leak and a bit of analysis.”
Hundreds of thousands of devices may be impacted
According to VERT, nearly 800,000 hosts may be affected. This is based on a Shodan search for the HTTP server banner, which was not provided.
Our own Shodan search for vulnerable SonicWall devices led us to two specific search queries:
The combined results from Shodan using these search queries led to a total of 795,674 hosts. In the VERT advisory, they specified that 795,357 hosts were vulnerable.
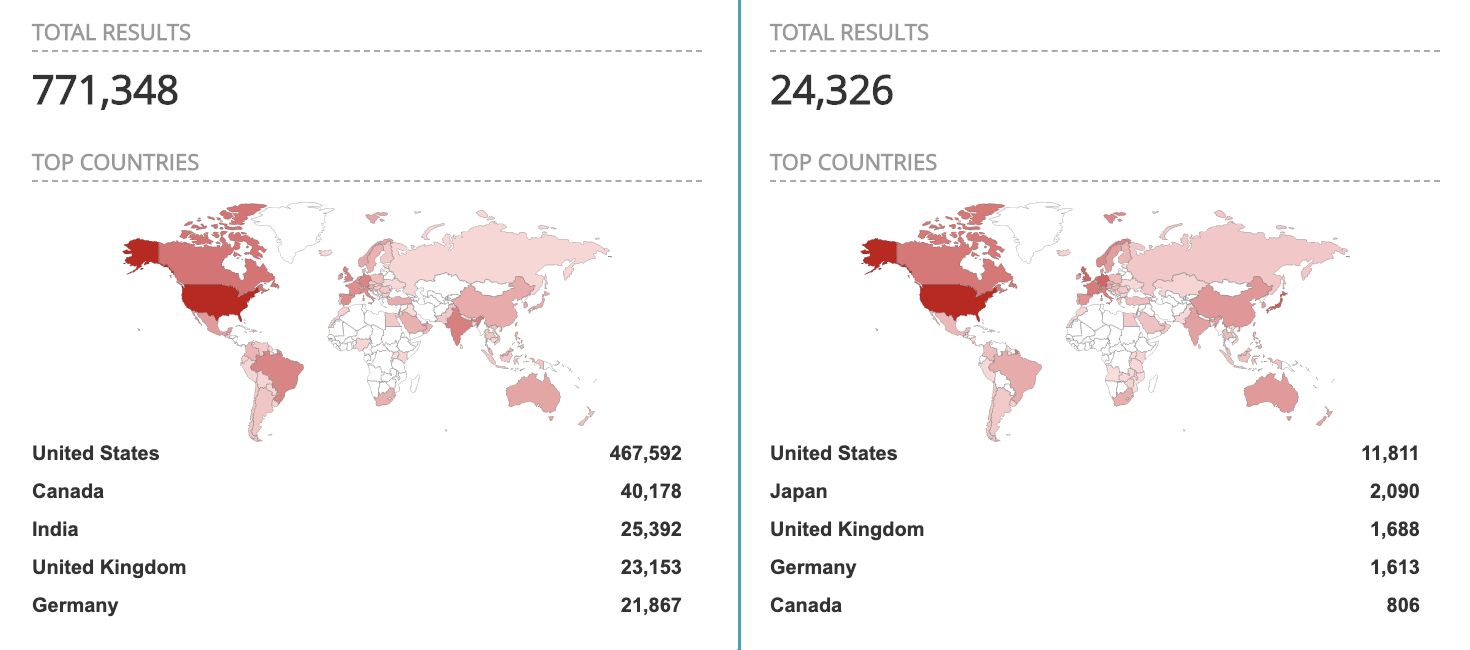
The Tenable Security Response Team was not able to independently confirm the hosts found on Shodan were indeed affected by this particular vulnerability. The hosts discovered with our Shodan queries are indicative that they are internet facing SonicWall servers, their respective versions could not be determined and thus it is unclear if they are vulnerable.
SSL VPN vulnerabilities: the gift that keeps on giving
Over the last year, cybercriminals and threat actors have been steadily leveraging vulnerabilities in a variety of SSL VPN solutions. As VPNs are found at the edge of a network and in most cases, publicly accessible, they are an enticing target for attackers. Exploitation of these devices can allow an attacker to pivot to an internal network and begin targeting additional hosts. Some notable vulnerabilities in VPN devices over the past year include:
| CVE | Vendor/Product | CVSSv3 | Tenable VPR* |
|---|---|---|---|
| CVE-2018-13379 | Fortinet FortiOS SSL VPN | 9.8 | 9.8 |
| CVE-2019-11510 | Pulse Connect Secure SSL VPN | 10.0 | 10.0 |
| CVE-2019-19781 | Citrix NetScaler ADC | 9.8 | 9.9 |
| CVE-2019-1579 | Palo Alto Networks Global Protect SSL VPN | 9.8 | 9.7 |
*Please note Tenable VPR scores are calculated nightly. This blog post was published on October 15 and reflects VPR at that time.
In the Cybersecurity Infrastructure Security Agency (CISA) alert (AA20-133A) entitled “Top 10 Routinely Exploited Vulnerabilities,” both CVE-2019-11510 and CVE-2019-1978 are featured as two of the most routinely exploited vulnerabilities in 2020.
In subsequent alerts from CISA, they’ve observed foreign threat actors utilizing several SSL VPN vulnerabilities as part of their attacks. On October 9, CISA issued a joint cybersecurity advisory with the Federal Bureau of Investigation regarding advanced persistent threat (APT) group activity, which highlighted the usage of CVE-2018-13379, CVE-2019-11510, CVE-2019-19781 as part of APT toolkits to gain initial access into their targeted environments.
With CVE-2020-5135, attackers potentially have another SSL VPN vulnerability in their respective toolboxes to target vulnerable systems.
SonicWall patched 10 additional vulnerabilities
In total, SonicWall patched 11 vulnerabilities on October 12. The following table lists the remaining 10 vulnerabilities that were patched:
| CVE | Advisory ID | Type | CVSSv3 |
|---|---|---|---|
| CVE-2020-5133 | SNWLID-2020-0008 | Unauthenticated Buffer Overflow | 8.2 |
| CVE-2020-5134 | SNWLID-2020-0009 | Out-of-Bound Invalid File Reference | 6.5 |
| CVE-2020-5136 | SNWLID-2020-0011 | Authenticated Buffer Overflow | 6.5 |
| CVE-2020-5137 | SNWLID-2020-0012 | Unauthenticated Buffer Overflow | 7.5 |
| CVE-2020-5138 | SNWLID-2020-0013 | Unauthenticated Heap Overflow | 7.5 |
| CVE-2020-5139 | SNWLID-2020-0014 | Unauthenticated Release of Invalid Pointer | 7.5 |
| CVE-2020-5140 | SNWLID-2020-0015 | Unauthenticated Malicious HTTP Request | 7.5 |
| CVE-2020-5141 | SNWLID-2020-0016 | Unauthenticated Brute Force | 6.5 |
| CVE-2020-5142 | SNWLID-2020-0017 | Stored Cross-Site Scripting (XSS) | 6.5 |
| CVE-2020-5143 | SNWLID-2020-0018 | Administrator Username Enumeration | 5.3 |
All of these vulnerabilities were discovered by security researcher Nikita Abramov of Positive Technologies Offensive Team. Abramov is credited with discovering CVE-2020-5135 along with Craig Young of VERT.
Proof of concept
At the time this blog post was published, no PoC code was available for any of the vulnerabilities, including CVE-2020-5135.
Solution
SonicWall published patches for all 11 vulnerabilities. The following table lists the affected versions along with their associated fixed version. Organizations are strongly encouraged to upgrade to a fixed version as soon as possible.
| Affected Versions | Fixed Versions |
|---|---|
| SonicOS 6.5.4.7-79n and below | SonicOS 6.5.4.7-83n |
| SonicOS 6.5.1.11 and below | SonicOS 6.5.1.12-1n |
| SonicOS 6.0.5.3-93o and below | SonicOS 6.0.5.3-94o |
| SonicOSv 6.5.4.4-44v-21-794 and below | SonicOS 6.5.4.v-21s-987 |
| SonicOS 7.0.0.0-1 | SonicOS 7.0.0.0-2 and above |
If upgrading is not feasible at this time, a temporary workaround, while inconvenient, would be to ensure the SonicWall SSL VPN portal has been disabled.
Identifying affected systems
A list of Tenable plugins to identify CVE-2020-5135 will appear here as they’re released.
Get more information
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
Learn more
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success