CVE-2019-11510: Critical Pulse Connect Secure Vulnerability Used in Sodinokibi Ransomware Attacks
Recent rash of ransomware attacks are leveraging an eight-month-old flaw in a popular SSL VPN solution used by large organizations and governments around the world.
Background
On January 4, security researcher Kevin Beaumont (@GossiTheDog) observed two "notable incidents" in which a vulnerability in a Secure Socket Layer (SSL) Virtual Private Network (VPN) solution was used to breach two organizations and install targeted ransomware.
New by me: Pulse Secure VPN flaw being used to deliver targeted ransomware to large organisations https://t.co/h4rrzbPOWG
— Kevin Beaumont (@GossiTheDog) January 4, 2020
In his blog, Beaumont says this vulnerability was used to gain access to the vulnerable networks, followed by a similar pattern: obtaining domain administrator access, installing Virtual Network Computing (VNC) using PsExec for lateral movement, disabling endpoint security tools and installing the Sodinokibi ransomware, also known as Sodin or REvil.
Scott Gordon, Chief Marketing Officer for Pulse Secure, issued the following statement regarding Beaumont’s blog:
“Threat actors will take advantage of the vulnerability that was reported on Pulse Secure, Fortinet and Palo Alto VPN products -- and in this case, exploit unpatched VPN servers to propagate malware, REvil (Sodinokibi), by distributing and activating the Ransomware through interactive prompts of the VPN interface to the users attempting to access resources through unpatched, vulnerable Pulse VPN servers.”
Analysis
Pulse Secure Vulnerability
CVE-2019-11510 is a critical arbitrary file disclosure vulnerability in Pulse Connect Secure, the SSL VPN solution from Pulse Secure. Exploitation of the vulnerability is simple, which is why it received a 10.0 rating using the Common Vulnerability Scoring System (CVSS). The flaw could allow a remote, unauthenticated attacker to obtain usernames and plaintext passwords from vulnerable endpoints.
While Pulse Secure issued an out-of-cycle patch for the vulnerability in April 2019, it garnered more attention after a proof of concept (PoC) for the flaw was made public in August 2019. Shortly after the PoC was released, reports began to surface that attackers were probing for vulnerable endpoints and attempting to exploit the flaw.
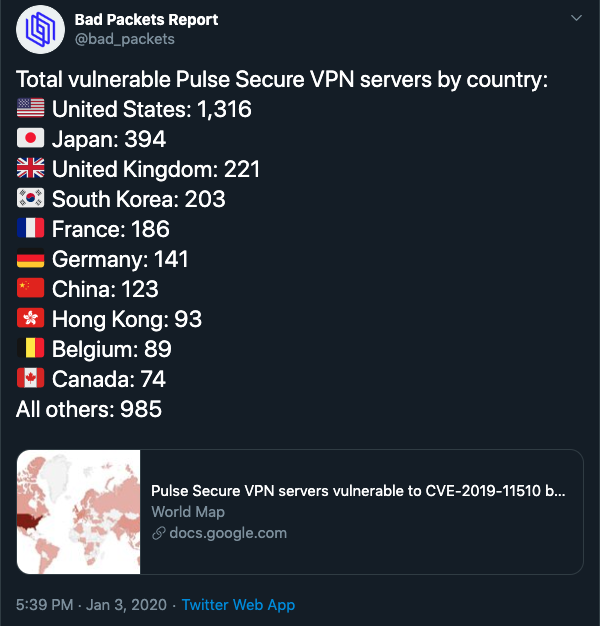
At the time, Troy Mursch, Chief Research Officer at Bad Packets, identified over 14,500 Pulse Secure VPN endpoints that were vulnerable to this flaw. Mursch has been working to notify affected organizations to patch the flaw while also publishing weekly reports on Twitter of scan results for vulnerable endpoints. According to the most recent scan result from January 3, 2020, Mursch detected 3,825 endpoints that remain vulnerable, with over 1,300 of those endpoints residing in the United States.
Sodinokibi (REvil) Ransomware
Sodinokibi (or REvil) first appeared in April 2019 as part of attacks utilizing a zero-day exploit for an unauthenticated remote code execution vulnerability in Oracle WebLogic identified as CVE-2019-2725. Additional research in July 2019 found that Sodinokibi also exploits CVE-2018-8453, an elevation of privilege flaw in Win32k, which the researchers called “rare among ransomware.”
Sodinokibi has been linked to the creators of the GandCrab ransomware, which shuttered its operations in May 2019 after earning a reported $2 billion in ransom payments.
Big Game Hunting Ransomware
The use of the term “Big Game Hunting” references a Crowdstrike blog from 2018 regarding the electronic crime group dubbed INDRIK SPIDER pivoting from banking trojans to targeted ransomware attacks using the BitPaymer ransomware. The “big game” component refers to threat actors shifting to “targeted, low-volume, high return” activity.
In the case of Sodinokibi, it appears this tactic has been fruitful. Security researcher Rik Van Duijn identified at least seven cases of Sodinokibi ransomware infections in the first six days of 2020 demanding over $10 million based on analyzed malware samples, underscoring just how much potential value there is in these big game hunting ransomware attacks.
REvil is starting the year strong, asking for some serious cash. We are working on a blog describing just how bad it is, hoping to launch end of the month.
— rik van duijn (@rikvduijn) January 6, 2020
cc @GossiTheDog pic.twitter.com/0Katzxd7aW
While Sodinokibi has been linked to various vulnerabilities mentioned above, it is important to note that ransomware in general spreads through a variety of methods, including unpatched software vulnerabilities, malicious emails and exposed remote desktop systems.
Proof of concept
The first PoC published for CVE-2019-11510 was released on August 20 to Exploit Database by security researchers Alyssa Herrera and Justin Wagner. There are also multiple PoCs to identify and/or exploit CVE-2019-11510 published to GitHub repositories.
Solution
As previously noted, Pulse Secure released patches for CVE-2019-11510 back in April 2019. If your organization utilizes Pulse Connect Secure in your environment, it is paramount that you patch as soon as possible. Additionally, because Sodinokibi uses CVE-2018-8453, it is also extremely important to ensure the appropriate security updates from Microsoft’s October 2018 Patch Tuesday have been applied.
Identifying affected systems
A list of Tenable plugins to identify this vulnerability can be found here, which includes a direct exploit check, identified as Plugin ID 127897.
Get more information
- Kevin Beaumont's Blog on Big Game Ransomware Exploiting CVE-2019-11510
- Out-of-Cycle Advisory for Multiple Vulnerabilities in Pulse Connect Secure
- Troy Mursch's Blog on 14,500 Vulnerable Pulse Secure VPN Endpoints
- Cisco Talos' Blog on Sodinokibi Ransomware Exploiting CVE-2019-2725
- Kaspersky's Blog on Sodinokibi Ransomware Using CVE-2018-8453
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management


