Synopsis
The Plex Media Server has a weak cross-origin resource sharing (CORS) policy. By default, an Access-Control-Allow-Origin header is returned by a media server with a value of '*', meaning any origin is allowed to send requests to the media server. A remote, unauthenticated attacker is able to exploit this to steal an X-Plex-Token and/or force a victim user to send requests to their own server without their knowledge. This would allow the attacker to, for example, access private media, change server settings, reboot media server services, etc.
This vulnerability would be exploited via a phishing attack, where a victim admin user would be tricked into logging into the attacker's Plex Media Server. The client-side code in the victim's browser, hosted by the attacker's media server, would then be able to access media server(s) that the victim administers. This scenario is shown in the PoC below.
Proof of Concept
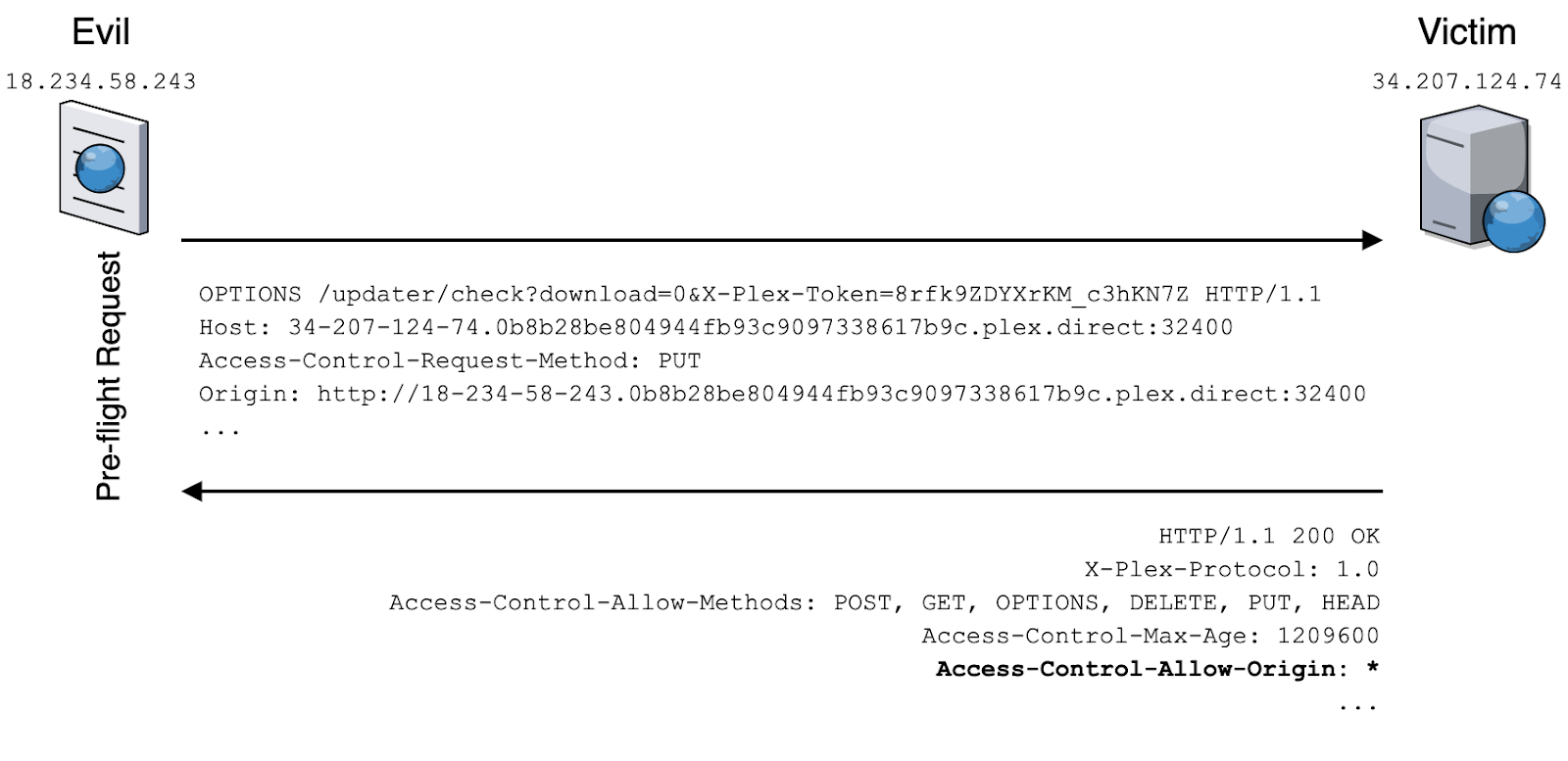
In the image below, a victim user hosts a Plex Media Server at 34.207.124.74, and an attacker hosts a media server at 18.234.58.243. The victim user just logged into the attacker's server, and the following preflight request/response was observed.
Note, the IP addresses in the video differ from the previous example.
Solution
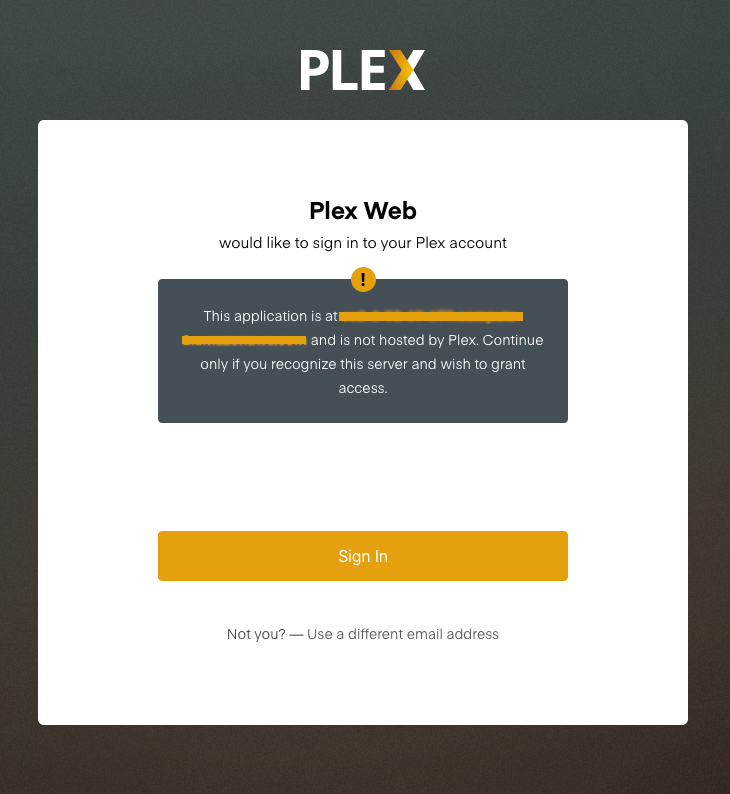
As of June 15, 2020, Plex has deployed a mitigation on authentication pages server side to notify users if they are logging into an application not hosted by Plex.
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success