by Josef Weiss
March 19, 2015
During a resource attack, a resource is depleted to the point that its functionality is affected. Virtually any resource can be targeted using this type of attack. The result of a successful resource attack is usually the degrading or denial of one or more services. To prevent resource depletion, you should monitor normal network activity and devices. General resources that present easy targets are CPU cycles, RAM, network throughput and I/O operations.
By utilizing LCE and deployed LCE Clients, these resources can be easily monitored through SecurityCenter Continuous View (SecurityCenter CV). Each LCE Client sends a heartbeat message containing a snapshot of the system's existing CPU, memory and disk usage. The System Monitor TASL script includes some default levels for global alerting, and these can be overridden by adding advanced TASL parameters to the TASL parameters configuration box as part of the advanced configuration options for TASL and Plugins, found in the LCE configuration options. By default, this script will generate a new alert any time a CPU rating of more than 90%, a memory usage of more than 90%, a disk usage of more than 90% has been encountered, or a load level larger than 3. To modify these settings, consult the Log Correlation Engine documentation.
This report displays results to assist the analyst in analyzing resource depletion. The report includes trending and table data on event spikes and high utilization events found within the environment. Trending is available for the most common resource targets, such as: CPU cycles, RAM utilization, network throughput and I/O operations. The remaining chapters display results to the analyst via tables that report expanded details on the specific event notifications, such as time, event type, and detailed event description/message.The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 4.8.2
- LCE 4.4.1
- PVS 4.0.3
Tenable's SecurityCenter Continuous View (SecurityCenter CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with Tenable’s Passive Vulnerability Scanner (PVS), as well as log correlation with Tenable’s Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network. LCE provides deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities.
The report contains the following chapters:
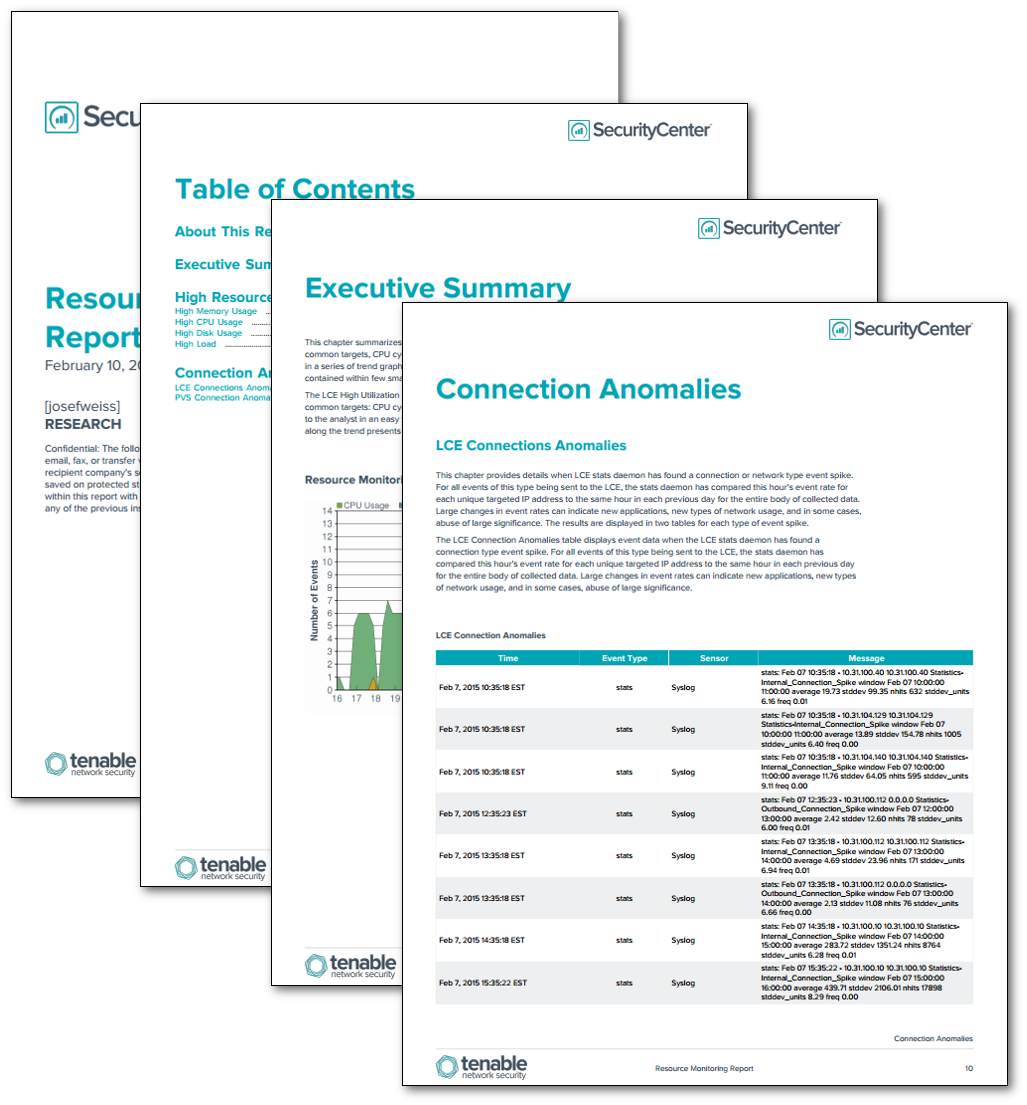
- Executive Summary - This chapter summarizes event spikes and high utilization events found within the environment for the most common targets, CPU cycles, RAM utilization, network throughput and I/O operations. Results are displayed in a series of trend graphs, which allow the reader to become rapidly acquainted with a large body of material contained within few small graphs.
- High Resource Usage Event Details - This chapter summarizes Log Correlation Engine events utilizing the system_monitor TASL script. The script can be configured with a variable threshold to alert for high usage events and reports details such as high usage events, and high memory, CPU, disk or load threshold events. These events are generated when various UNIX and Windows LCE clients send in their systems’ current statistics data to the LCE.
- Connection Anomalies - This chapter provides details when LCE stats daemon has found a connection or network type event spike. For all events of this type being sent to the LCE, the stats daemon has compared this hour's event rate for each unique targeted IP address to the same hour in each previous day for the entire body of collected data. Large changes in event rates can indicate new applications, new types of network usage, and in some cases, abuse of large significance. The results are displayed in two tables for each type of event spike.