by Cesar Navas
September 3, 2020
The National Banking and Securities Commission (CNBV) Annex 72 is a collection of 30 Key Risk Indicators (KRI) that establish compliance standards for financial institutions operating in Mexico. The KRIs cover several topics such as secure management, vulnerability management, user and access management, anti-malware and obsolete or outdated software. Tenable.sc provides passive and active detection methods to correlate vulnerability data to align with said KRIs. All financial institutions in Mexico should be prepared to divulge all KRIs to CNBV auditors when requested. This report pulls together several of the key grouping based on assets type and risk levels to help the operations team understand the current state of the Vulnerability Management program and to effectively plan mitigation efforts.
Financial institutions are at a higher risk of being targeted and attacked. In an effort to successfully manage risk mitigation practices, operations teams should understand and document the security configuration of cyber assets. Knowing the status of compliance scans across the organization assists these teams to assess and mitigate identified risks. Tenable.sc provides a full suite of risk detection methods starting with active and passive vulnerability detection, along with configuration audit & compliance assessment.
This report provides a detailed view of the KRIs identified in the organization. The report is broken up into four chapters which describe the topics mentioned in each KRI. With each chapter, an operations team is shown different topics that span the KRIs; They are, Secure Management, Risk Management, and Unsupported Product Summary. By tracking active, passive, and compliance vulnerability data the operations team is able to successfully report and mitigate on the CNBV’s requirements for the related KRIs.
CNBV Annex 72 requires knowledge of assets on the network and the appropriate identification, categorization, and protection of these assets. Knowing the types of assets on the network also aids in efficiently identifying, managing, and mitigating known vulnerabilities in administrative, accounting, and business communications systems. Vulnerability assessments are required to be performed frequently. Similarly, CNBV requires software to be maintained at a level supported by the vendor.
This report is available in the Tenable.sc feed, which is a comprehensive collection of dashboards, reports, assurance report cards, and assets. The report can be easily located in the Tenable.sc feed under the compliance category. The report requirements are as follows:
- Tenable.sc 5.12.0
- Nessus 8.7.1
- Compliance Data
This report provides the organization with a clear and simplified method to identify problem areas where compliance is not being met according to Annex 72 by CNBV. Tenable.sc enables the operations team to Analyze data and identify the non-compliant KRI’s. Through this process the operations team is able to complete the Fix and Measuring steps of the Cyber Exposure Lifecycle. Tenable.sc is the On-prem solution for understanding the whole picture of the network, while keeping the data under the organization’s control. Built on leading Nessus technology, Tenable.sc discovers unknown assets and vulnerabilities, and monitors unexpected network changes before they turn into breaches.
This report contains:
Executive Summary: This chapter gives the operations team an overview of the organization’s compliance standing as related to CNBV’s Annex 72. The chapter has a section for 3 topics that span a large portion of the KRI topics; the topics include vulnerability management, user and access management and anti-virus management. This chapter allows operations teams to quickly assess compliance and understand the more critical areas of concern.
Risk Management: This chapter gives the operations team a look into mitigation techniques, and provides guidance as to where their efforts should be focused. By showing SLA tracked mitigated and unmitigated vulnerabilities, the operations team is able to better understand the risk to an environment when a vulnerability is detected. For example, a vulnerability with a medium severity could be actively exploited, and therefore be more urgent to mitigate, via patches or configuration.
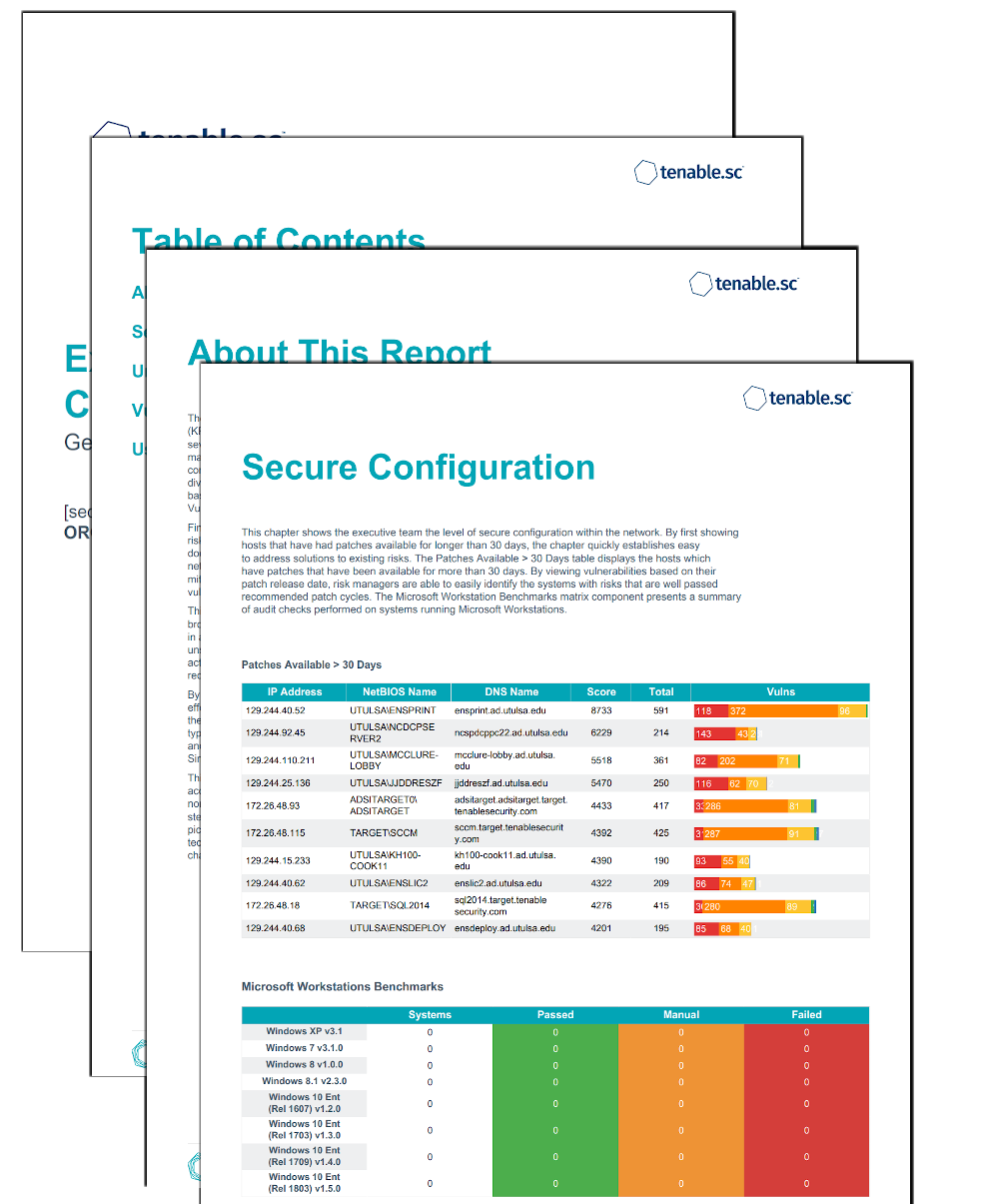
Secure Configuration: This chapter shows the operations team the level of secure configuration within the network. By first showing hosts that have had patches available for longer than 30 days. The chapter quickly establishes easy to address solutions to existing risks. Microsoft workstation and Linux compliance results are also introduced to further establish a level of secure configuration that is needed based on CNBV’s Annex 72.
Unsupported Product Detail: This chapter shows the operations team the overall presence of unsupported products in the network. The organization has a responsibility to maintain software, operating systems, and databases at a level supported by the vendor. The chapter identifies unsupported applications, Operation Systems and databases per the requirements of the CNBV.