by Cody Dumont
November 6, 2015
The National Institute of Standards and Technology (NIST) develops many standards that are available to all industries. A common set of standards is the NIST 800-53. This report summarizes all the families outlined in the NIST Special Publication 800-53 Revision 4. The publication consists of 18 families, and each family contains security controls related to the general security topic. Each security control was designed to help organizations, both private and government, to select the controls best suited to protect mission critical services. Implementing these controls properly can aid in the defense against a diverse set of threats including hostile cyber attacks, natural disasters, structural failures, and human errors.
The NIST families and controls is not a checklist-type compliance standard like HIPAA, PCI, or CSF; rather, it is a catalog of controls that are used in achieving compliance with the aforementioned standards. Using this report can assist the organization in understanding how they currently meet various standards. The first chapter is a series of indicator matrices showing management the controls that have been audited. Following the Executive Summary is a chapter for each family that contains bar charts with network summaries and tables providing lists of identified hosts.
This report covers all the NIST families currently supported by Tenable audit files, which provide the results of an audit check as one of three severity levels. The informational severity level is considered a pass. The pass is achieved when the configuration setting matches the expected result of the audit check. The match can be a defined value or a range of values. The “Nessus Compliance Checks” document, available in the Support Portal, contains details on how to edit the audit files. When an audit check fails, the severity is set to high, indicating that the collected result and the expected result do not match. A mismatch may not mean a failure. Each failure should be reviewed and verified to ensure the expected result is correct. If the expected result is not correct, then the audit file should be modified and the scan should be run again. Results assigned a medium severity must be evaluated by an analyst to determine whether the results are accurate or not.
The elements in this report use audit files (released after 1 July 2013), which incorporate the reference tag that maps many audit checks to a respective standard. In the case of this report, the audit files must contain a string similar to '800-53|IA-5' on the reference line of the applicable audit check.
For example 'reference: CCE|CCE-8912-8,800-53|IA-5,PCI|8.5.12,800-53|CM-6'
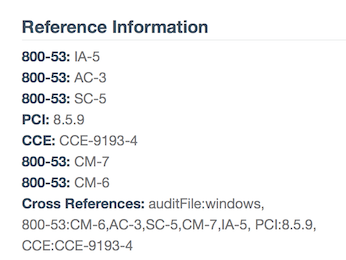
Please note that if you are creating you own filters and reports, the '800-53: IA-5' shown in the example is actually '800-53|IA-5' in the data query.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 4.8.2 or Tenable.sc 5.1
- Nessus 8.5.1
- Audit Files containing NIST references
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Tenable.sc Continuous View (CV) measures compliance in real-time without human intervention. Allowing the organization to identify gaps and lapses are detected and prioritized immediately. With more supported technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure, Tenable.sc CV provides the best solution for managing compliance with regulations. Tenable provides peace of mind to customers, because Tenable.sc CV detects security and compliance issues before our competitors.
NIST Controls
Access Control: The Access Control family is a series of controls that determine the setting used for limiting access to systems and information stored on the systems. Some of the controls provide guidance on account management and privilege assignments. The guidance provided helps to address the assignment of roles, and define business functions. Other settings covered include login time, screen saver requirements, and similar activity based controls. The guidance for users, which require access to system level resources or administrative rights, is discussed in the controls. Developers and program manages can use these controls to understand session timeout settings and recommendations and least privilege.
Audit and Accountability: The Audit and Accountability family provides the mechanism to record policy violations and related activities. The control provides guidance on log retention policies and configurations. The family also provides information on what data should be retained in each log. Time synchronization is import when performing incident response. Data collected using audit and accountability methods should use a common NTP sever, other guidelines related to time stamps is covered in this family.
Awareness and Training: The Awareness and Training control assists with measuring the control and effectiveness of security controls. The metrics provide visibility into how well security controls protect systems, and how well users understand the controls in use. As of 2015, there are only few audit checks that measure this control; therefore this content may often be blank.
Configuration Management: This family focuses on baseline establishment and identifying the minimal software installations. Many of the important details concerning change control and configuration management is described in this family.
Contingency Planning: This family contains many of the auditable setting for backup and recovery of systems. The settings include detecting the back of sensitive data, scheduling backup and other related settings.
Identification and Authentication: The audit checks in this family primarily focus on the configuration setting concerned with authentication systems. While authentication for users who are employed by the organization, this family also tracks authentication for guests, contractors, shared accounts, and service account. Some setting will also validate the configuration of RAIDUS, TACACS, and Two-Factor based authentication.
Incident Response: This family identifies auditable setting to support incident response efforts.
Maintenance: The controls in this family provide guidance on how to perform, documents, and audit records of maintenance and repairs on information systems. The organization should track the maintenance activities of support personal regardless of the location of equipment and personnel. Guidance tracking impacted security controls is also discussed in this family.
Media Protection: This family provides information on how to maintain security for digital media. By offering guidance on how to configured media controls, classification markings, storage policies, and usage this family can assist an organization in using different media more securely.
Personnel Security: This family provides guidance on handing personnel related issues such as, termination, promotion, transfer, and other related tasks. The audit checks look for common settings that can assist with these tasks.
Physical and Environmental Protection: This family provides guidance on the physical security requirements. Using logs from digital locks and other events create enable physical controls and digital controls can be correlated. Information leakage is also addressed in this family, providing guidance on how to address signal leakage and other electronic communication controls.
Planning: This family provides guidance on information security architecture and describes the overall philosophy, requirements, and approach organizations take with regard to protecting the confidentiality, integrity, and availability information. Provides guidance for integrating security into other enterprise architectures.
Program Management: This family provides guidance on facilitating compliance with applicable federal laws, Executive Orders, directives, policies, regulations, and standards. Additionally the audits in this family provide a vehicle for the organization to document in a central repository the all the security controls.
Risk Assessment: This family provides guidance on the requirements to perform risk assessments. Risk assessments take into account threats, vulnerabilities, likelihood, and impact to organizational operations and assets, individuals, other organizations, and the Nation based on the operation and use of information systems.
Security Assessment and Authorization: This family provides guidance for the effective implementation of security controls and enhancements. Guidance for corrective actions and related milestones are reported in this family. Other information with respect to penetration testing and other internal systems audits are described in this this family.
System and Communication Protection: This family provides guidance on the how implement protected communications with a system. One aspect is the separation of duties, for example making sure the administrative interface is not part of the regular user interface. Other controls are limiting direct hardware access, memory address space controls, intrusion detection, and other methods on monitoring system resources.
System and Information Integrity: This family provides guidance on monitoring information systems affected by announced software vulnerabilities, email vulnerabilities (SPAM), error handling, memory protection, output filtering and many other areas of security. Many of these audit checks will need to be customized and should reviewed by the organization.
System and Services Acquisition: This family provides guidance on using service-based software such as Telnet, HTTP, and other services. Some of which may be authorized under some conditions and not under other conditions. These settings should be reviewed and customized to meet the local polices for the organization.