by Josef Weiss
May 6, 2014
With a search engine as prevalent as Internet Explorer (IE) is in every modern organization, focusing on this common browser should be standard practice in all risk mitigation efforts. Since IE cannot be removed from Microsoft Windows, every windows host in the world is potentially susceptible to IE vulnerabilities and attacks. This report helps analysts and management better understand the organization’s attack surface and overall risk.
In this report, the tables listing installed versions of IE can be used to assist analysts in discovering which hosts may have outdated or unsupported versions. These outdated versions should be upgraded immediately. After discovering all of the installed IE versions in the environment, analysts can use the IE-related vulnerability information to identify the current risk and assess the actions that need to be taken to reduce that risk.
For analysts seeking to address the most critical threats related to IE, the chapter on IE vulnerabilities that allow for remote code execution is a perfect start. The vulnerabilities presented there are an immense risk, as they can allow an attacker to execute code remotely, bypassing most other environmental security measures.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Discovery & Detection.
The report requirements are:
- Tenable.sc 5.5.2
- Nessus 8.6.0
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Tenable's family of products includes Tenable.sc Continuous View (CV), Nessus, Nessus Network Monitor (NNM), and Log Correlation Engine (LCE). Tenable.sc CV provides the most comprehensive and integrated view of network health, and is the global standard in detecting and assessing network data.
This report contains the following chapters:
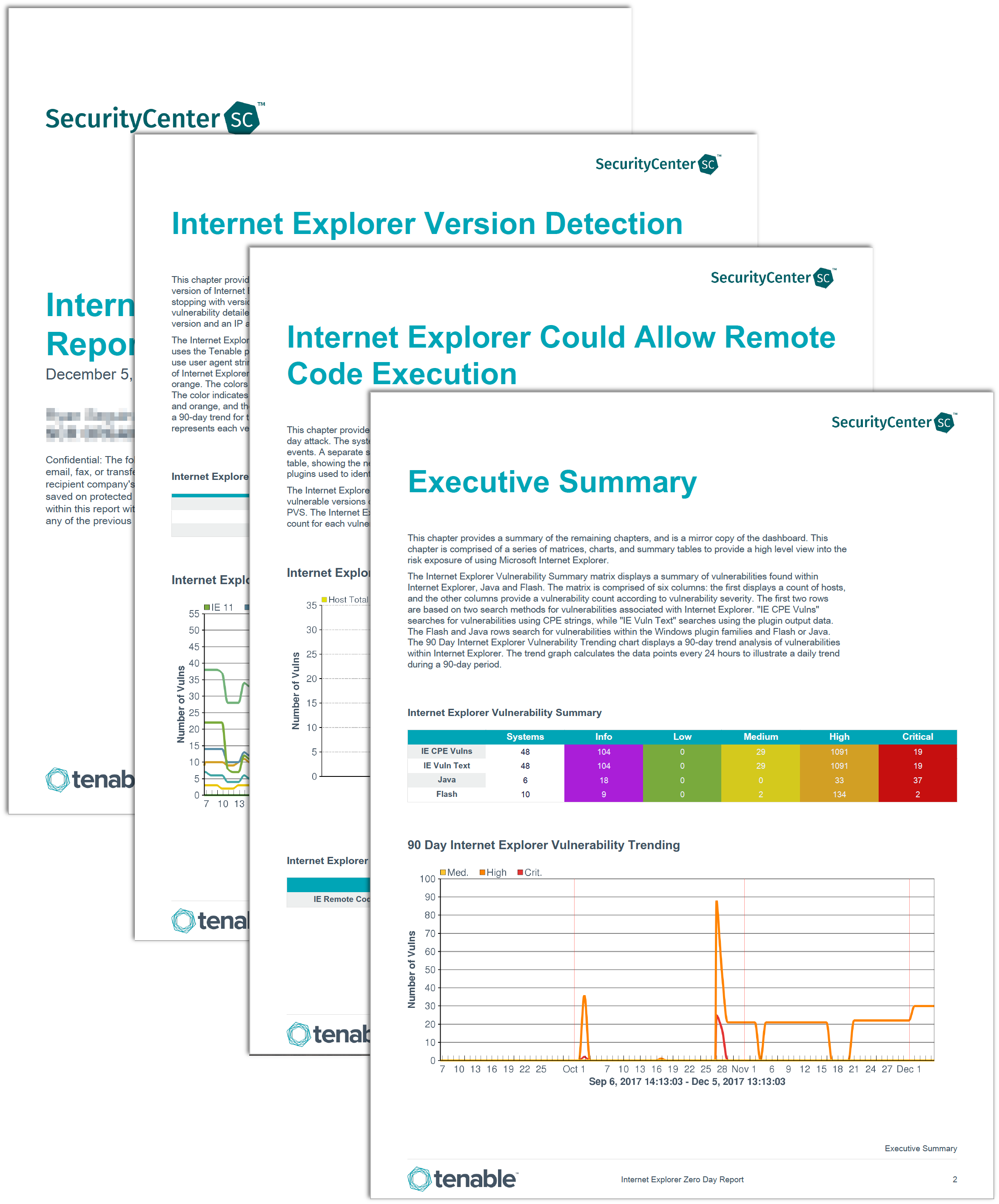
Executive Summary - This chapter provides a high-level view into the current risks associated with Microsoft Internet Explorer. Analysts can use this high level view to better understand the current attack surface and risk level in the environment. The data in presented here can help analysts assess risk and create remediation strategies related to Internet Explorer.
Internet Explorer Version Detection - The Internet Explorer Version Detection chapter provides a detailed summary of all networks and hosts running Internet Explorer. For each version of Internet Explorer there is a separate section, beginning with most current version 11, and stopping with version 3. Each section contains a bar chart and table, showing the network summary and a vulnerability detailed report. The vulnerability detail shows the plugins used to identify the Internet Explorer version and an IP address list of each host with vulnerability.
Internet Explorer Could Allow Remote Code Execution - The Internet Explorer Could Allow Remote Code Execution Chapter provides the detection methods used to identify systems with are vulnerable to zero day attack. The systems identification methods include active and passive scanning, and log correlation events. A separate section is available for each detection method. Each section contains a bar chart and table, showing the network summary and a vulnerability detailed report. The vulnerability detail shows the plugins used to identify the Internet Explorer vulnerabilities and an IP address list of each affected host.
Enhanced Mitigation Experience Toolkit (EMET) - The Enhanced Mitigation Experience Toolkit (EMET) chapter provides a list of all systems that are configured with EMET. The EMET Tool is a Microsoft tool that works to prevent attacks through Microsoft products. The EMET toolkit will reach end of life in July of 2018.
Internet Explorer Related Vulnerabilities - The Internet Explorer Related Vulnerabilities chapter provides a detailed summary of vulnerabilities that are impacted by Internet Explorer. The details of vulnerabilities in Toolbars, ActiveX, Java, and Flash are reported. Additional information on Internet Explorer Autoruns is covered in a section.