by Megan Daudelin
March 4, 2016
File integrity monitoring is a key component of any information security program. Changes to configurations, files, and file attributes across the network are common, but the few that impact file or configuration integrity can be hidden within a large volume of daily changes. The changes can also reduce security posture and in some cases may be indicative of a breach in progress. Values monitored for unexpected changes to files or configuration items include credentials, privileges and security settings, content, core attributes and size, hash values, and configuration values. Several compliance regulations require file integrity monitoring, including PCI DSS, HIPAA, and NERC SIP.
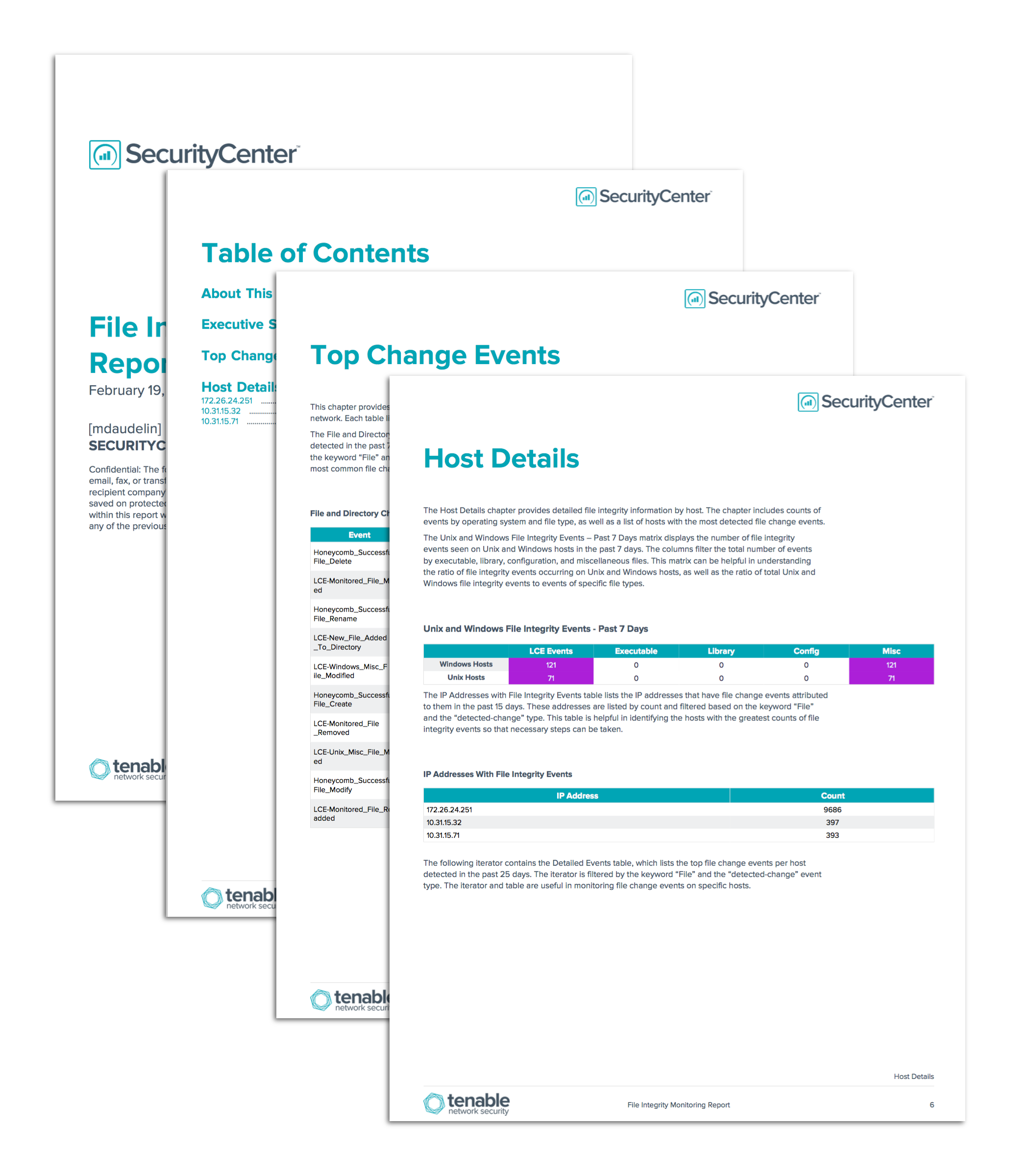
The File Integrity Monitoring report assists security teams in tracking file integrity events on the network. The report relies on normalized logs processed by the Log Correlation Engine (LCE), which provides an enhanced view of the events on the network related to file integrity. Data is filtered and displayed based on operating system, IP address, event type, and normalized event keywords.
The chapters in this report provide several views into the file integrity status of the network. The report helps security teams monitor file integrity events to ensure that necessary security measures are implemented. The detailed event information shows analysts the most common file change events and where they originate. Trend data demonstrates the rates of events over time; spikes in activity could be indicative of intentional measures such as patches or updates being applied, or they could be an indication of malicious activity on the network. Counts of events by IP address are tracked to show which hosts generate the greatest counts of file integrity events so that necessary steps can be taken. Events are also tracked by operating system and file type to help teams understand the ratio of file integrity events occurring on Windows or Unix hosts compared to the whole network, as well as the ratio of total Windows or Unix file integrity events to events of specific file types. This report provides a platform from which to monitor file integrity events on the network.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. This report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 4.8.2
- LCE 4.6.0
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. LCE Agents can be configured to monitor specific files or directories on local hosts. By integrating with LCE, SecurityCenter CV provides the most comprehensive view of file integrity.
This report contains the following chapters:
- Executive Summary: This chapter provides an overview of the file integrity status of the network over the past 25 days. The trend charts depict the rates of events over time. Spikes in activity could be indicative of intentional measures such as patches or updates being applied, or of malicious activity on the network.
- Top Change Events: This chapter provides detailed information about the most common file integrity events detected in the network. Each table lists detected normalized events and trend data by count.
- Host Details: The Host Details chapter provides detailed file integrity information by host. The chapter includes counts of events by operating system and file type, as well as a list of hosts with the most detected file change events.