by Sharon Everson
December 7, 2017
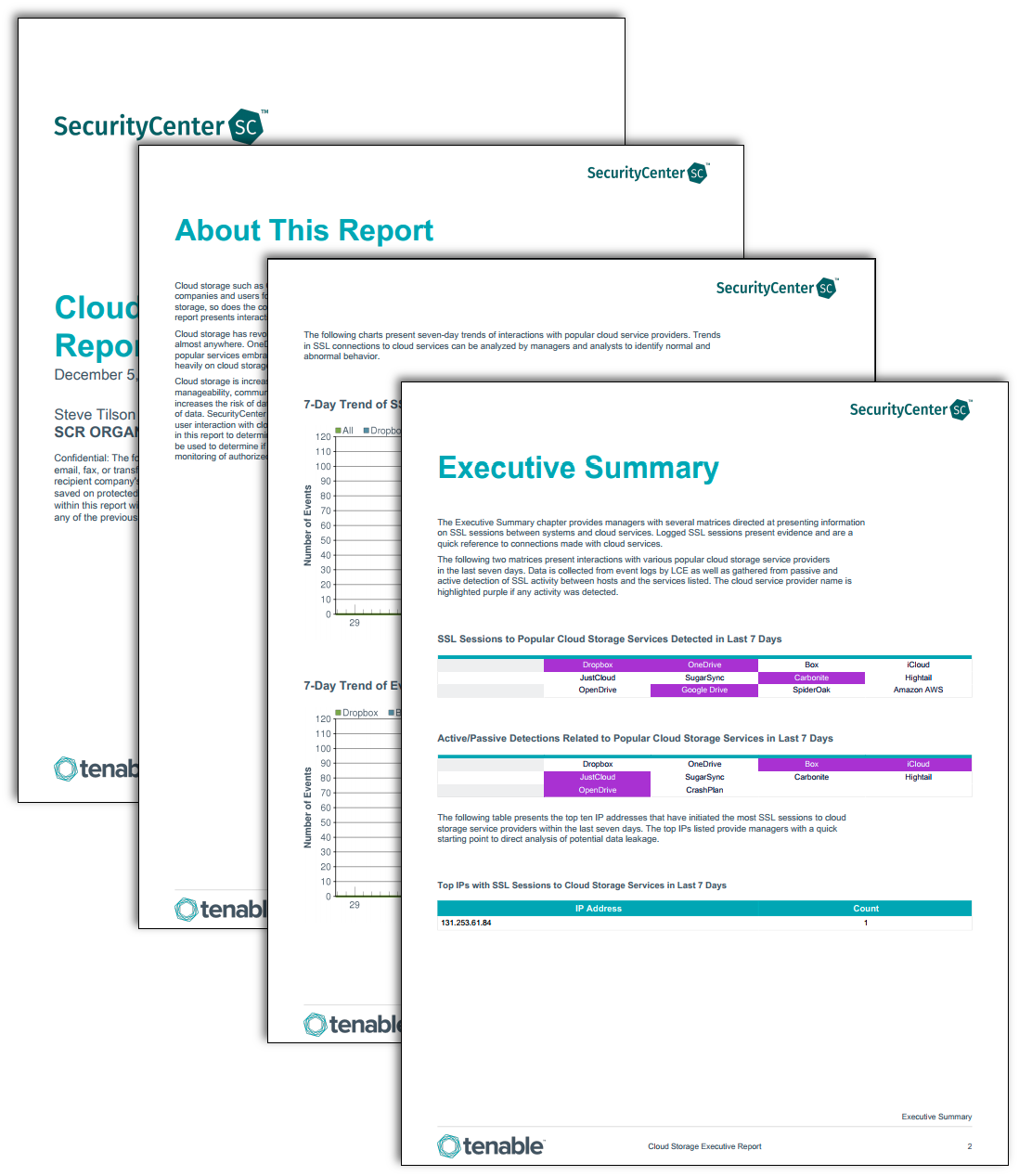
Cloud storage such as OneDrive, iCloud and Dropbox are a few of the popular services embraced by companies and users for backups and data storage. As remote storage opportunities expand for data storage, so does the concern for monitoring possible data leakage and the utilization of cloud services. This report presents interactions with cloud file storage services detected over the last seven days.
Cloud storage has revolutionized the way users can store and obtain data over a network connection from almost anywhere. OneDrive, iCloud and Dropbox are accessed over the internet and just a few of the popular services embraced by user for backups and data storage. Today many businesses and users rely heavily on cloud storage solutions, such as to backup end users' laptops and PCs.
Cloud storage is increasing in popularity for a host of reasons, including savings on storage costs, manageability, communication and tracking documentation and projects. However, storage in the cloud also increases the risk of data leakage. Unauthorized cloud services configured on systems may lead to loss of data. Tenable.sc™ Continuous View® (Tenable.sc™ CV) utilizes active and passive scanning along with event log information to track user interaction with cloud services. Business and Risk managers can use the detailed information provided in this report to determine if and when cloud services are being accessed. Information in this report can be used to determine if firewall changes may be required to prevent unauthorized use, or to enable better monitoring of authorized services being utilized.
This report is available in the Tenable.sc CV Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Executive.
The report requirements are:
- Tenable.sc 5.5.2
- Nessus 8.6.0
- NNM 5.9.0
- LCE 6.0.0
Note that this report relies on NNM detections being forwarded to the LCE. Make sure that the NNM is configured to send syslog messages to the LCE: in Configuration > NNM Settings > Syslog, include the LCE host (with port 514) in the Real-time Syslog Server List. The LCE listens for syslog messages by default.
Tenable's Tenable.sc™ Continuous View® (Tenable.sc™ CV) provides continuous network monitoring, vulnerability identification and security monitoring. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from unique sensors, delivering continuous visibility and critical context, and enabling decisive action that transforms a security program from reactive to proactive. Active scanning periodically examines the applications on the systems, the running processes and services, web applications and configuration settings. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Tenable.sc CV provides an organization with the most comprehensive view of the network and actionable information to support mitigation efforts and reduce cyber risk. Managers can better monitor and asses cloud storage access with Tenable.sc CV. Tenable enables powerful, yet non-disruptive, continuous monitoring that will provide organizations with the information needed to reduce risk within the enterprise.
The Following Chapter is included:
Executive Summary: The Executive Summary chapter provides managers with several matrices directed at presenting information on SSL sessions between systems and cloud services. Logged SSL sessions present evidence and are a quick reference to connections made with cloud services.