by David Schwalenberg
March 24, 2016
The North American Electric Reliability Corporation (NERC) is a not-for-profit international regulatory authority whose mission is to assure the reliability of the bulk power system in North America. NERC Reliability Standards define the reliability requirements for planning and operating the North American bulk power system, which serves more than 334 million people. NERC is committed to protecting the bulk power system against cyber security compromises that could lead to misoperation or instability. The NERC Critical Infrastructure Protection (CIP) Standards provide a cyber security framework for the identification and protection of Bulk Electric System (BES) Cyber Systems, to support the reliable operation of the North American bulk power system.
The purpose of CIP-010 R3 (Vulnerability Assessments) is to establish that active vulnerability assessments of BES Cyber Systems be performed. The purpose of CIP-007 R2 (Security Patch Management) is to establish a patch management process to remediate discovered vulnerabilities. Dangerous vulnerabilities can lead to critical failures, potential network compromise, and intrusion attacks, negatively impacting the reliable operation of the BES. Vulnerability assessments and patch management go hand-in-hand. Vulnerabilities must be remediated before any costly damage occurs, but remediations cannot be carried out until vulnerabilities are first discovered and the remediations are evaluated and prioritized.
For organizations that are required to be CIP compliant, Tenable.sc Continuous View (CV) can lead the way to compliance. This report can assist with detecting vulnerabilities, prioritizing remediations, and tracking patch management progress. The severities of vulnerabilities are assigned based on their Common Vulnerability Scoring System (CVSS) scores. The Security Patch Management component specifically addresses CIP-007 R2 requirements to evaluate and install patches within given time frames. This report can assist an organization in monitoring and improving its vulnerability management program, which will aid in meeting the CIP-010 R3 and CIP-007 R2 requirements and measures. If desired, more detailed information can be obtained through analysis within SecurityCenter CV.
The CIP standards recommend categorizing BES Cyber Assets into different impact categories. An asset's impact category is based on the adverse impact to BES reliability that would occur if the asset was unavailable, degraded, or misused. Once the impact categories of systems have been determined, asset groups in Tenable.sc CV can be used to group together machines in each impact category. Asset groups can then be applied to this report to narrow the focus and enable more accurate reporting on systems in specific impact categories. Using assets with reports is very similar to using assets with dashboards; for more information, see How to Add Assets in SecurityCenter and How to Use Assets with Dashboards. Alternatively, if the assets are in separate subnets, then subnet filters can be easily applied to narrow the focus of this report.
This report is available in the Tenable Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance. The report requirements are:
- SecurityCenter 5.2.0
- Nessus 8.4.0
- NNM 5.8.1
- LCE 9.0.0
Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution. For Supervisory Control and Data Acquisition (SCADA) systems, where reliability and not interfering with normal operations is a concern, Tenable.sc CV includes passive vulnerability detection with the Nessus Network Monitor (NNM), as well as log correlation with the Log Correlation Engine (LCE). Where possible, active vulnerability detection and compliance scanning with Nessus can also be done. Using Tenable.sc CV, an organization will obtain the most comprehensive and integrated view of its SCADA network.
Chapters
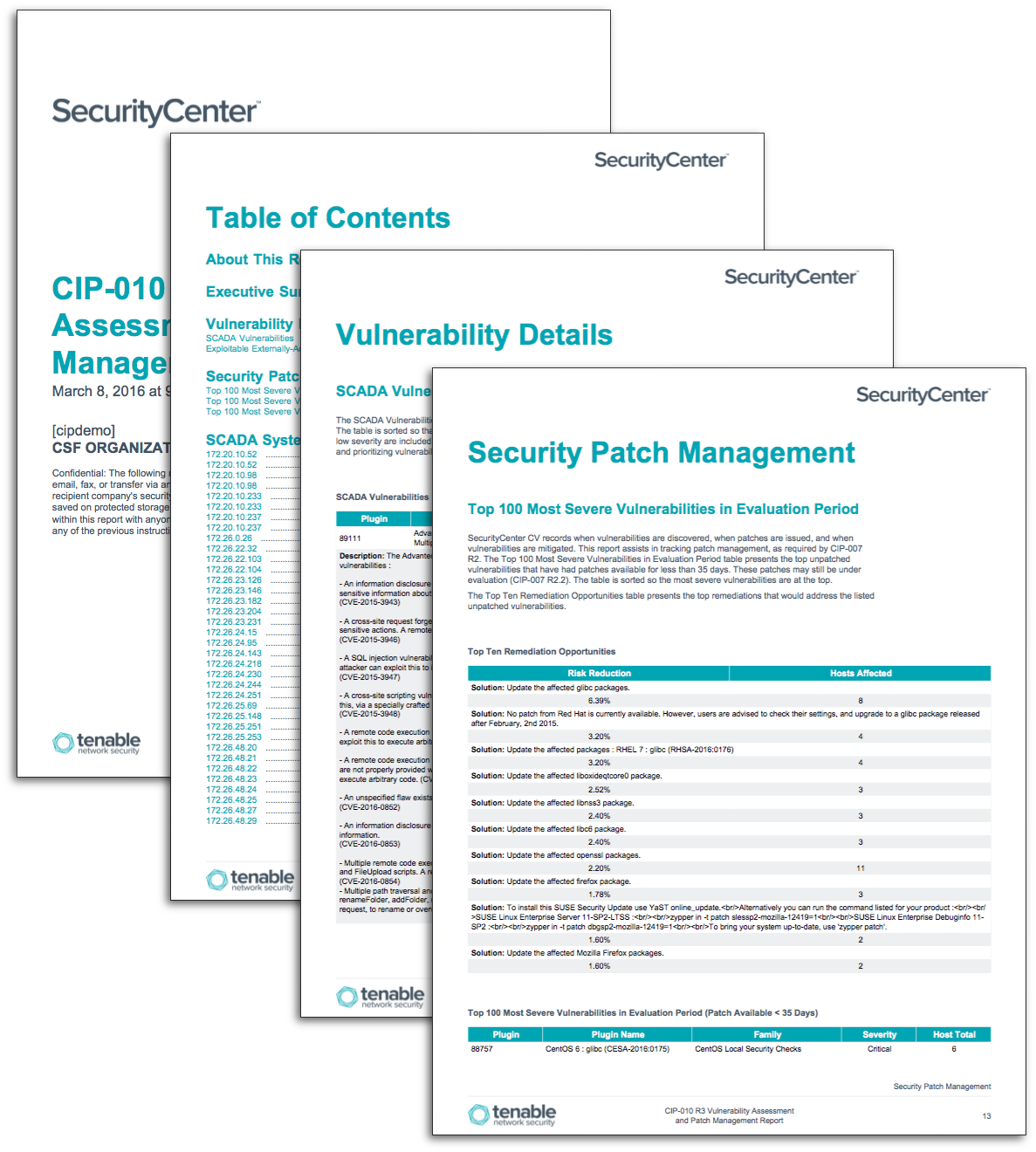
Executive Summary - This chapter presents a high-level overview of vulnerabilities on the network, focusing primarily on SCADA systems. This information can assist in detecting and prioritizing vulnerabilities and tracking remediations on critical assets, which will aid in meeting the CIP requirements and measures.
Vulnerability Details - This chapter presents detected SCADA vulnerabilities and externally-accessible vulnerabilities that are known to be exploitable. This information can assist in detecting and prioritizing vulnerabilities in critical assets, which will aid in meeting the CIP requirements and measures.
Security Patch Management - Tenable.sc CV records when vulnerabilities are discovered, when patches are issued, and when vulnerabilities are mitigated. This chapter assists in tracking patch management by presenting several lists of unpatched vulnerabilities. These lists are based on when patches for the vulnerabilities were issued, as specified by CIP-007 R2.
SCADA System Top Remediations by Host - This chapter presents remediation opportunities for each SCADA host actively or passively detected on the network. This information can assist an organization in patch management efforts, which will aid in meeting the CIP requirements and measures.