by Ryan Seguin
August 28, 2017
In February 2017, the Australian Signals Directorate (ASD) released the “Essential 8” mitigation strategies from their top 35 best practices for securing information systems. The purpose of the Essential 8 is to provide an appropriate baseline standard for organizations to mitigate their own Cyber Exposure. The ASD suggests that organizations start by ensuring that the Essential 8 mitigation strategies be implemented, then organizations can adopt other Top 35 mitigation strategies based on the risks of the organization.
The ASD Essential 8 is split into 2 sections: “To prevent malware from running,” and “To limit the extent of incidents and recover data.” Tenable.sc’s “ASD Top 4 Mitigation Strategies” dashboard covers the Top 4 of the Essential 8. Tenable.sc’s “Browser Vulnerabilities” dashboard leverages vulnerability information about web browsers to provide information on user application hardening. This report provides a comprehensive indicator of how well you comply with the ASD Essential 8.
The ASD Essential 8 report leverages data from Tenable.sc, which combines active scanning using Nessus with passive vulnerability scanning from Nessus Network Monitor. Vulnerability data is broken up into software details and browser specific vulnerabilities, organized by browser type. The final section provides remediation guidance to mitigate these vulnerabilities.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report's requirements are:
- Tenable.sc 5.4.5
- Nessus 8.5.1
Tenable's Tenable.sc is the market-defining continuous network monitoring solution, which assists organizations in securing their internal network. Tenable.sc utilizes the CVSS scoring system for vulnerabilities; providing a uniform approach to vulnerability assessment, and Tenable.sc obtains information on environmental vulnerabilities through active scanning. Nessus Agents enable scanning and detection of vulnerabilities on transient and isolated devices. Tenable.sc provides an organization with the most comprehensive view of risks within the network and the intelligence needed to support effective vulnerability remediation efforts.
This report contains the following chapters:
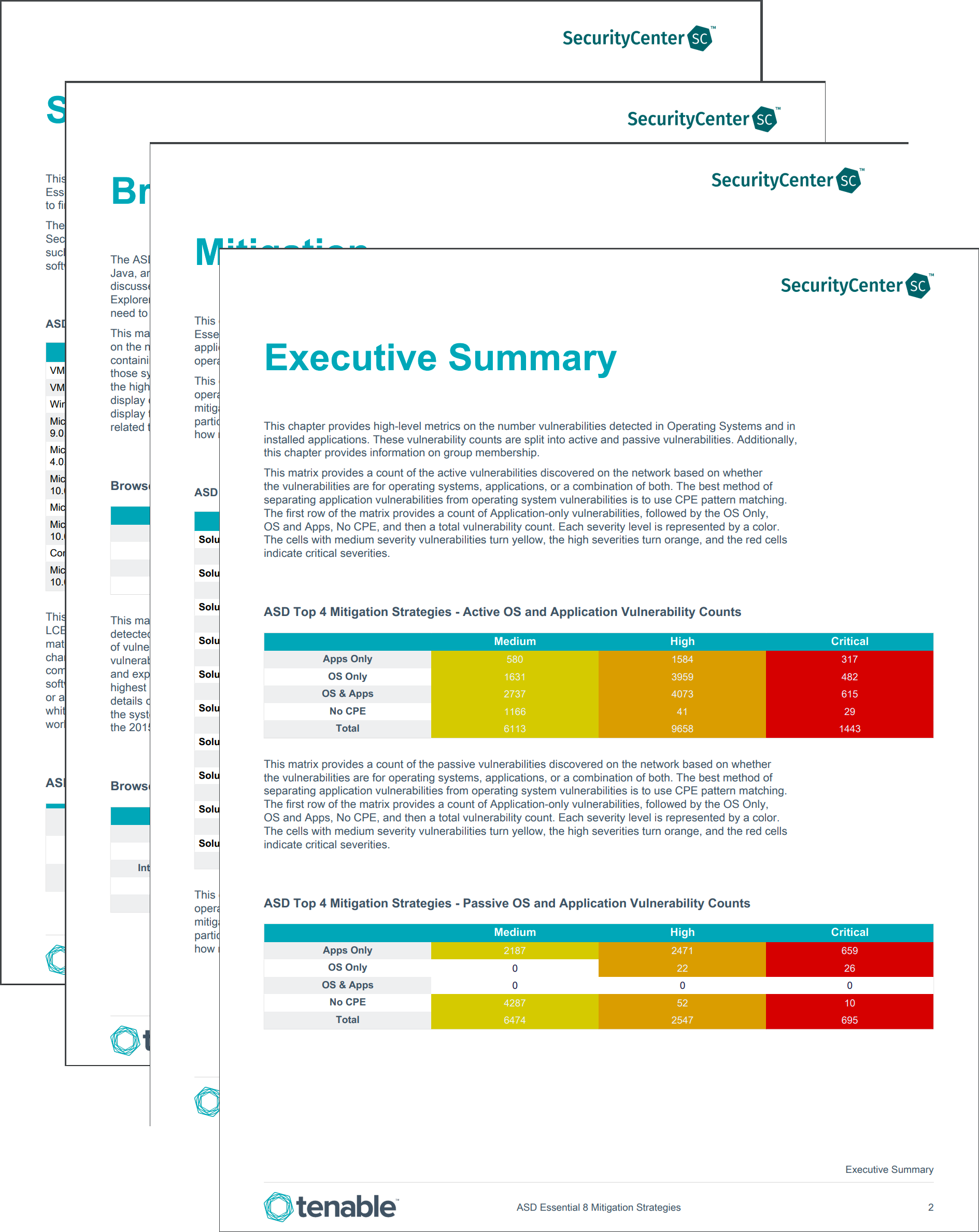
Executive Summary: The Executive Summary section provides high-level active and passive OS and application vulnerability information, and group membership/privileged access indicators.
Software Details: The Software Details chapter provides information regarding what software is installed and if there have been any modifications to the software.
Browser Vulnerabilities: The Browser Vulnerabilities chapter provides vulnerability data associated with 5 commonly used web browsers: Google Chrome, Mozilla Firefox, Safari, Opera, and Internet Explorer.
Mitigation: The Mitigation chapter provides OS and application vulnerability mitigation solutions.