by Cody Dumont
Patch management is a key process of any risk management program. Operating system patch management is often built into the operating systems, but what about the other applications used in an organization? This report helps monitor the patch management process for several different types of allocations.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- Tenable.sc 4.8.1
- Nessus 8.5.1
Tenable's Tenable.sc Continuous View (CV) has the ability to track new and mitigated vulnerabilities. When a host is scanned and a vulnerability is discovered for the first time, the Vulnerability Discovered date is set. When the host is scanned a subsequent time, and the vulnerability is no longer present, the vulnerability is considered mitigated. When a vulnerability is mitigated, the Vulnerability Mitigated date is set. Analysts can use the Days to Mitigate filter to track the amount of time taken to apply a patch.
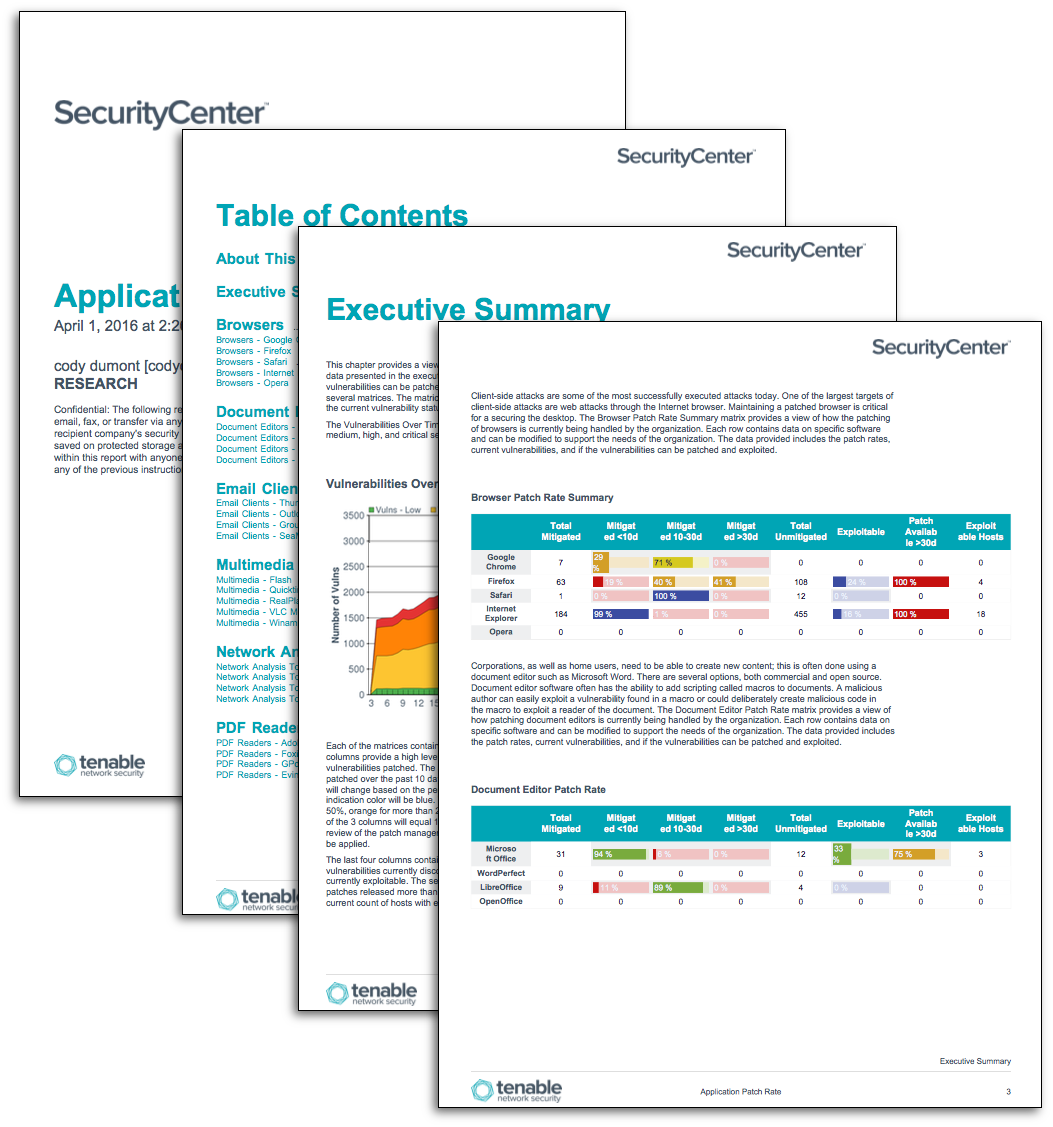
The chapters in this report provide a view of how application patching is currently being handled by the organization. The data provided includes the patch rates, current vulnerabilities, and if the vulnerabilities can be patched and exploited. The report contains seven chapters. The first chapter is an executive summary and provides a summary view of the state of application patch rates. The remaining six chapters provide a series of bar charts and tables with the details of patches applied and outstanding patches required.
Tenable.sc Continuous View's (CV) ability to scale vulnerability management allows the organization to identify the biggest risk across the entire enterprise. Providing a unique combination of detection, reporting and pattern recognition utilizing industry recognized algorithms and models. Tenable.sc CV, Log Correlation Engine (LCE), Nessus Network Monitor (NNM), and Nessus are continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits.
Chapters
Executive Summary - This chapter provides a view of how application patching is currently being handled by the organization. The data presented in the executive summary includes the patch rates, current vulnerabilities, and if the known vulnerabilities can be patched and exploited. The chapter contains a trend line for current vulnerabilities and several matrices. The matrices include eight columns: four report on the mitigation status and four report on the current vulnerability status.
Browsers - Client-side attacks are some of the most successfully executed attacks today. One of the largest targets of client-side attacks are web attacks through the Internet browser. Maintaining a patched browser is critical for a securing the desktop. This chapter provides several sections reporting on Google Chrome, Firefox, Safari, Internet Explorer, and Opera internet browsers.
Document Editor - Corporations, as well as home users, need to be able to create new content; this is often done using a document editor such as Microsoft Word. There are several options, both commercial and open source. Document editor software often has the ability to add scripting called macros to documents. A malicious author can easily exploit a vulnerability found in a macro or could deliberately create malicious code in the macro to exploit a reader of the document. This chapter provides several sections reporting on Microsoft Office, WordPerfect, LibreOffice, OpenOffice.
Email Client - Email clients are susceptible to client-side attacks via attachments or by Multi-Purpose Internet Mail Extensions (MIME) embedded attacks. Other methods of exploitation are through the supported authentication methods or protocols used to access email servers. This chapter provides several sections reporting on Thunderbird, Outlook, GroupWise, & SeaMonkey.
Multimedia Patch Rate - Multimedia applications and frameworks are common attack vectors, as they parse large amounts of data. While parsing the large data files, they are often prone to buffer overflows or other file parsing attacks. This chapter provides several sections reporting on Flash, Quicktime, RealPlayer, VLC Media Player, and Winamp.
Network Analysis Tool - There are several different type of network analysis tools found on a corporate network. Some of these tools, such as a network sniffer, must parse large data files and can be prone to buffer overflow attacks. These applications can also use unsecure protocols such as SNMP for monitoring the network or transferring files. This chapter provides several sections reporting on Wireshark, tcpdump, NET-SNMP, and SolarWinds.
PDF Reader - The Portable Document Format (PDF) is a widely used file format used to share information across platforms and environments. The PDF file format is constantly expanding and includes many embedded scripting features. A malicious author can easily exploit these scripting features, such as Javascript. Keeping corporate approved PDF readers up to date is critical for a successful security program. This chapter provides several sections reporting on Adobe Reader, Foxit, GPdf, and Evince.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success