by Cody Dumont
March 11, 2016
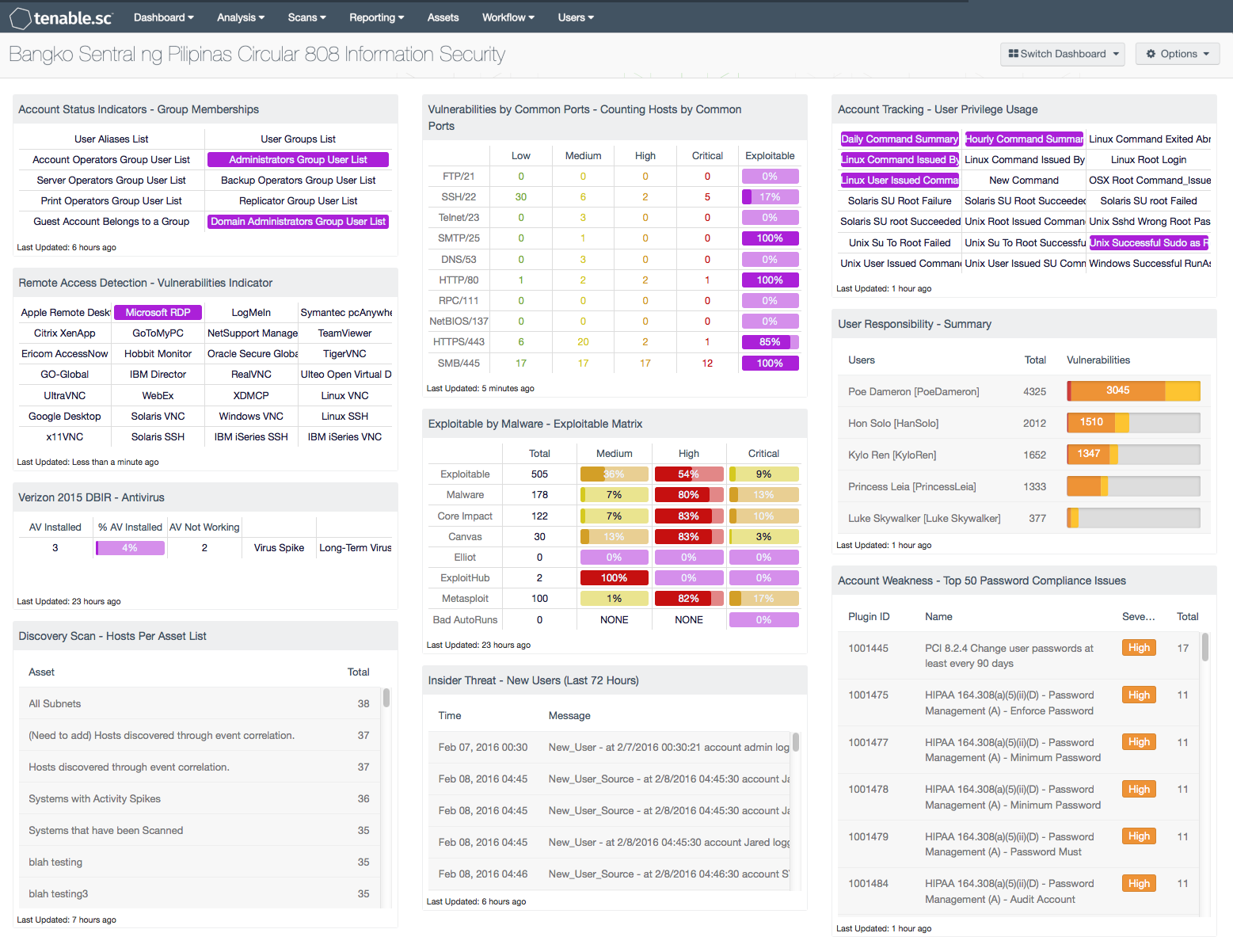
Information Technology Risk Management is crucial for any financial institution to protect their critical assets from potential cyber attacks. The Bangko Sentral ng Pilipinas (BSP) Circular 808 (August 2013) provides guidelines to assist the BSP Supervised Institutions (BSI) with the adoption of technology in the financial service industry. The dashboard focuses on Appendix 75b Information Security.
As the growing number of BSIs deploy innovative technologies to reduce risk, the need to properly monitor and audit these technologies increases. BSIs need to ensure the environment is properly audited to identify deficiencies in security controls and IT operations. The Information Security (IS) Area defines the controls needed to ensure the confidentiality, integrity, and availability is properly maintained and monitored for threats. The scope of Appendix 75b is extended to cover unauthorized access, deliberate misuse, and fraudulent modification, insertion, deletion, substitution, suppression, or disclosure. The Appendix helps the BSIs monitor their complex risk profile. Tenable.sc Continuous View (CV) can be used to analyze and report on client/server architecture, network communications, and telecommunications. The scalability of Tenable.sc CV allows the monitoring of user privilege, group memberships, network activity, responsibility monitoring, and many more aspects of information security.
As Tenable.sc CV collects logs, network flows, and vulnerability data, the BSIs can monitor many of the aspects of Appendix 75b. Logs correlated from syslog sources, LCE Agents, and other sources can provide details on user privilege escalation. Using Nessus, information on group memberships and exploitable vulnerabilities can be easily collected. This dashboard pulls information from several resources to provide a good overview of the BSI’s information security progress.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.2.0
- Nessus 8.5.1
- LCE 6.0.0
- Compliance Scan Results
Tenable.sc Continuous View (CW) provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. When implementing Tenable.sc CV with Nessus, Log Correlation Engine (LCE), and the Nessus Network Monitor (NNM), Tenable is able to provide the most comprehensive and integrated view of network health. Tenable.sc CV provides peace of mind to customers by: detecting security and compliance issues before our competitors, proactively identifying the biggest risk in the enterprise network, and enabling the BSI to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance.
Components
Account Status Indicators - Group Memberships: In paragraph 3.2.3, there is discussion on the allocation of access rights and least privilege. This component helps by providing a list of common plugins that can be utilized to monitor membership of privileged groups.
Remote Access Detection - Vulnerabilities Indicator: In paragraph 3.2.7, there is discussion about maintaining logs and monitoring remote access communications. This component provides several indicators for remote access communications.
Verizon 2015 DBIR – Antivirus: In paragraph 3.2.9, there is discussion about malicious code prevention. This component helps to monitor antivirus maintenance on the network.
Discovery Scan - Hosts Per Asset List: In paragraph 3.2.1, there is discussion about maintaining inventory of the assets in the BSI network. This component helps by providing a count of hosts per asset list.
Vulnerabilities by Common Ports - Counting Hosts by Common Ports: In paragraph 3.3.1, there is discussion about monitoring data flows. This component provides a high-level view of vulnerabilities by common ports.
Exploitable by Malware - Exploitable Matrix: In paragraph 3.2.9, there is discussion about malicious code prevention. This component helps to identify systems most at risk of being compromised by malicious code.
Insider Threat - New Users (Last 72 Hours): In paragraph 3.2.4, there is discussion on controlling access to information systems. Access to systems begins with user accounts, this component helps track when new user activities are identified.
Account Tracking - User Privilege Usage: In paragraph 3.2.4, the discussion is on limiting access and tracking the use of elevated privileges. The component provides several indicators of events related to privilege escalation commands. Drilling down into each cell can provide a list of hosts with the related event. By further examining all the events for each host, the analyst can see commands or a summary of commands used each day.
User Responsibility – Summary: In paragraph 3.2.5, there is discussion about delegating responsibility to other teams or individuals. The component uses the responsibility tool to monitor risk profile based on the person responsible for securing the systems. However, the responsible person or group will need to have accounts created in Tenable.sc for this component to work correctly.
Account Weakness - Top 50 Password Compliance Issues: In paragraph 3.2.4, there is discussion on the use of default accounts, passwords, and other settings. This component uses the results of Configuration Audit scans to report on system settings.