Confidently quantify your evolving cyber exposure
As a security leader, you face increased pressure to measure and communicate your organization's cyber risk posture. Boards, C-suites, lines of business and regulators all demand clarity.
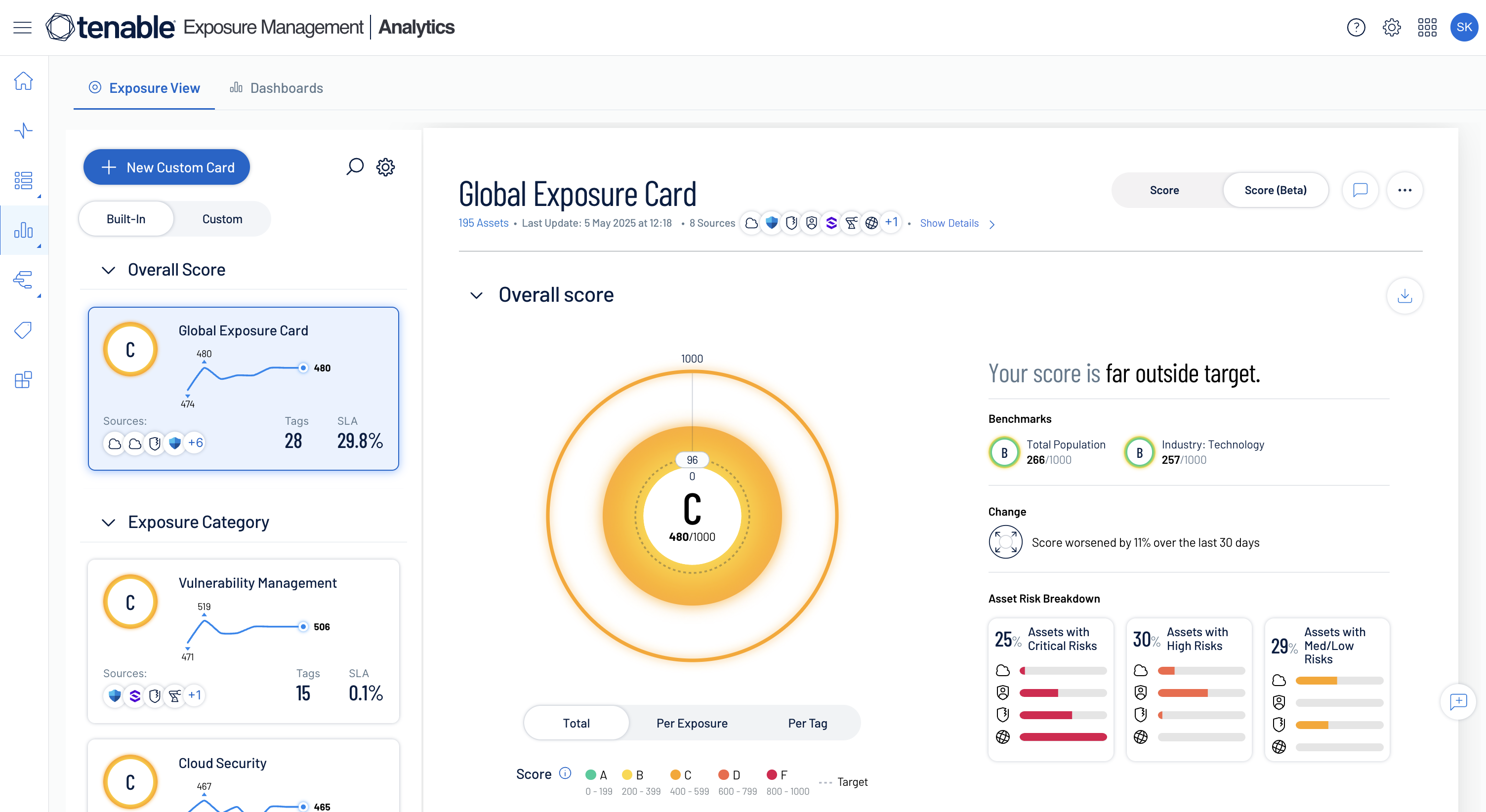
Optimize your exposure management program with exposure analytics
Gain a measurable, business-aligned view of cyber risk needed to mobilize resources and optimize security investments
Exposure data at your fingertips
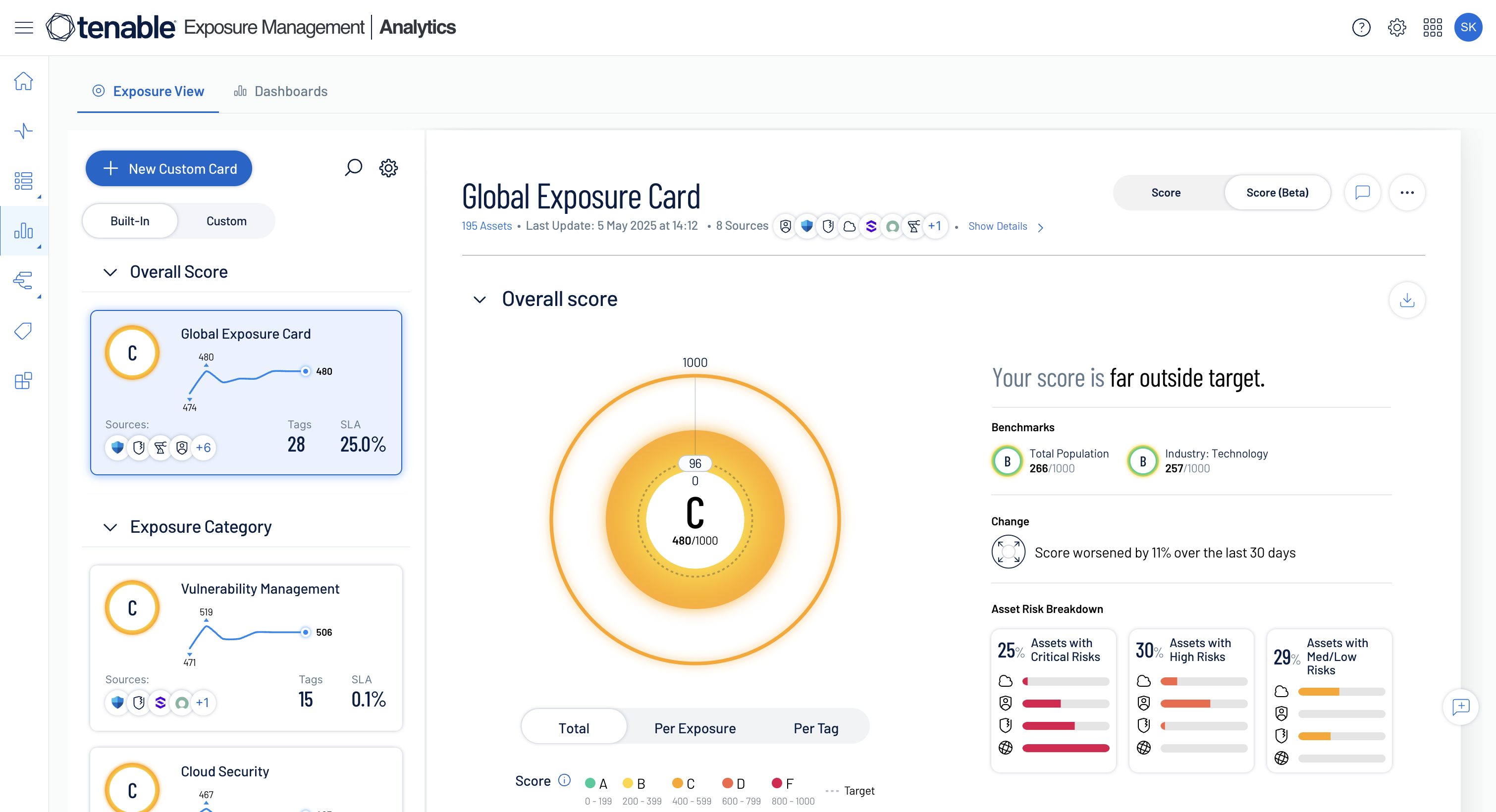
Quantify cyber posture
Track your organization's overall risk posture over time with a quantified Cyber Exposure Score and answer the question, "How secure are we?" to the board, executives and regulators.
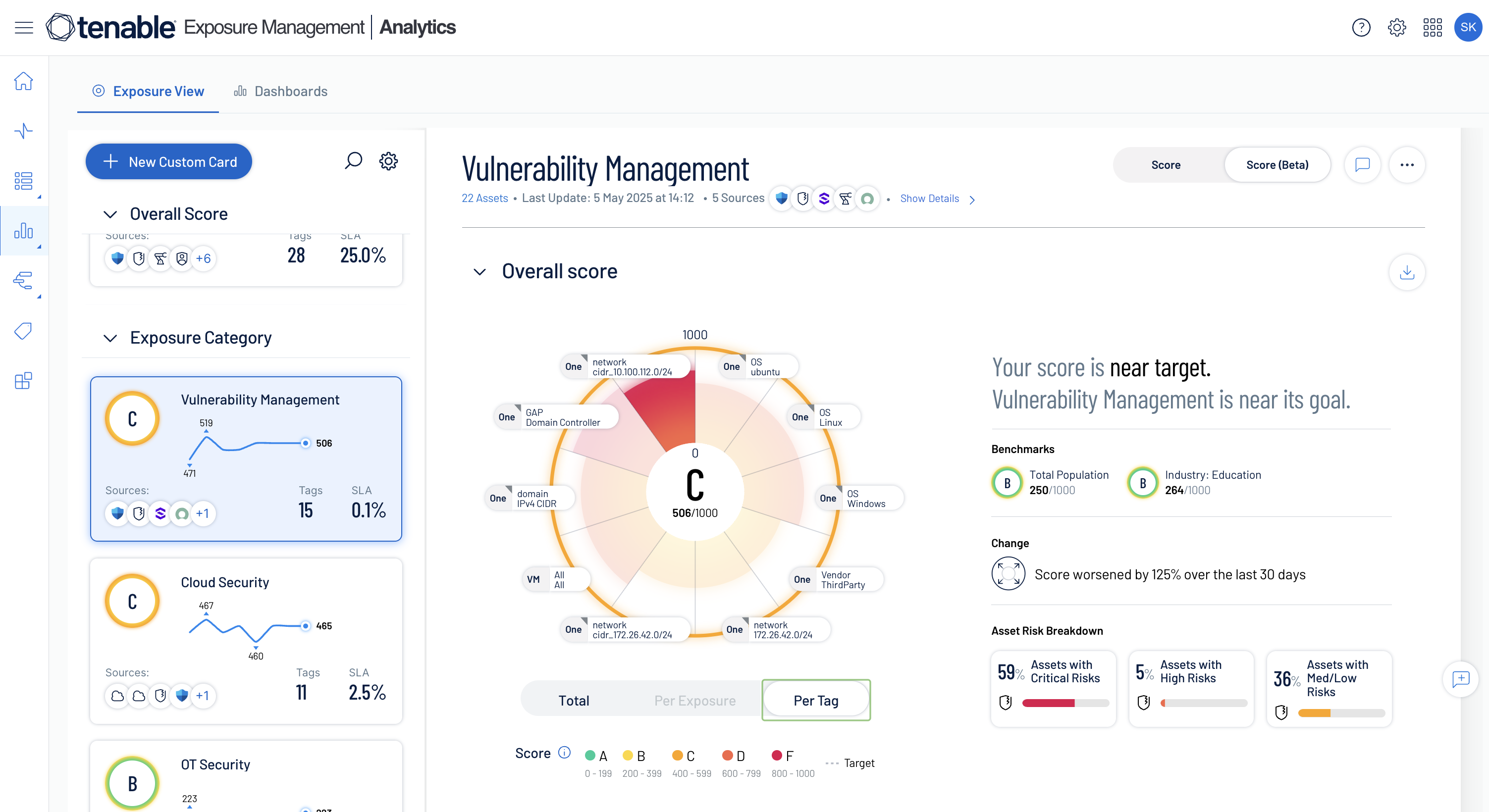
Enable risk-based decision making
Improve communication with lines of business with targeted exposure scores aligned to the things they care about most, and justify required investments in people and technology.
Track service level commitments
Easily assess your organization’s exposure management progress against remediation objectives to understand your exposure as a whole or per exposure category.
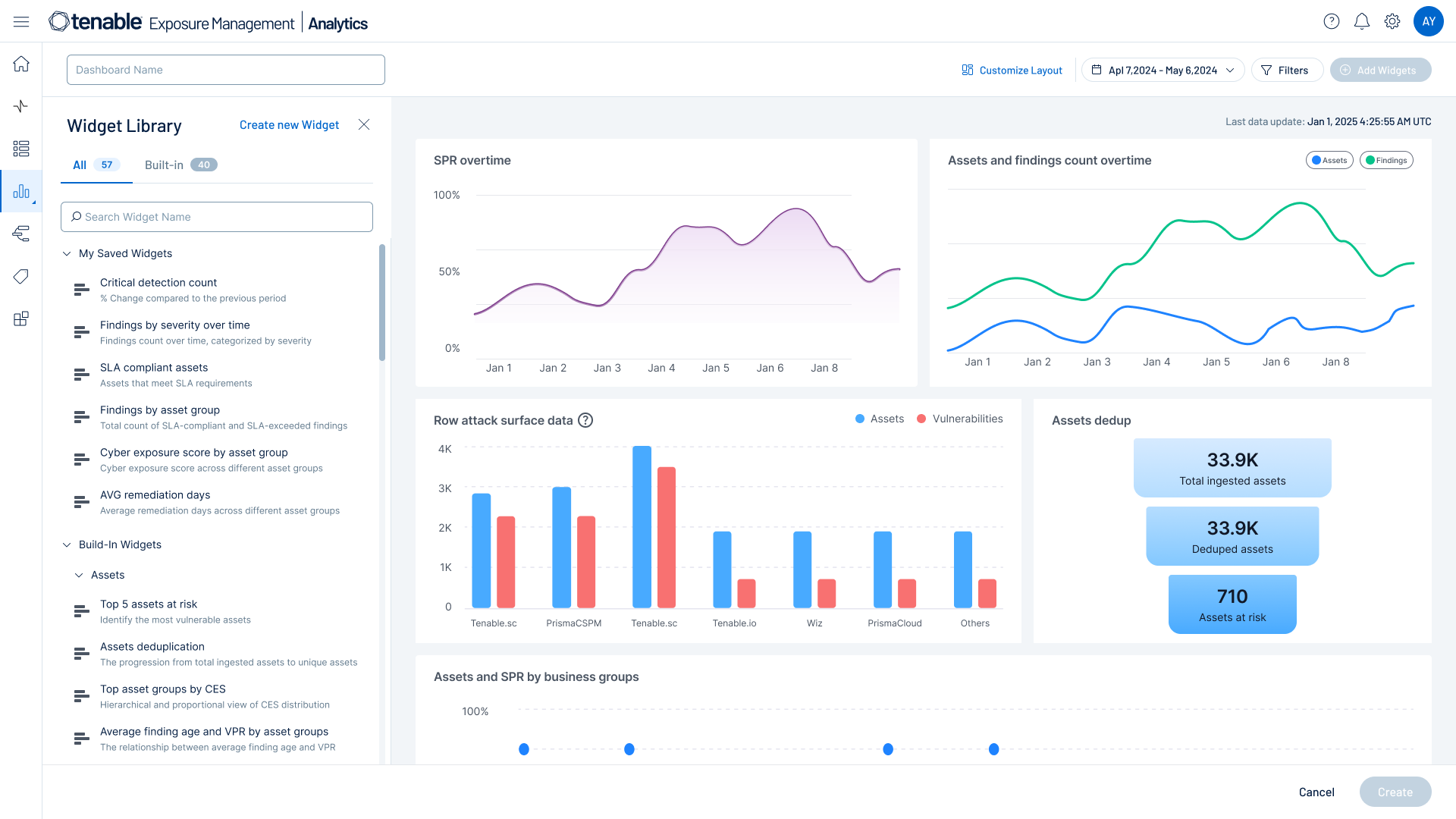
Unify risk and compliance reporting
Break down silos, with unfied reporting that brings together asset and risk data from your existing Tenable and third party tools, massively reducing administrative overhead while providing unique exposure context.
Explore how Tenable One can help you
-
Simplify risk insights
Use business-aligned exposure insights for proactive risk mitigation and strategic alignment with your organization’s priorities.
-
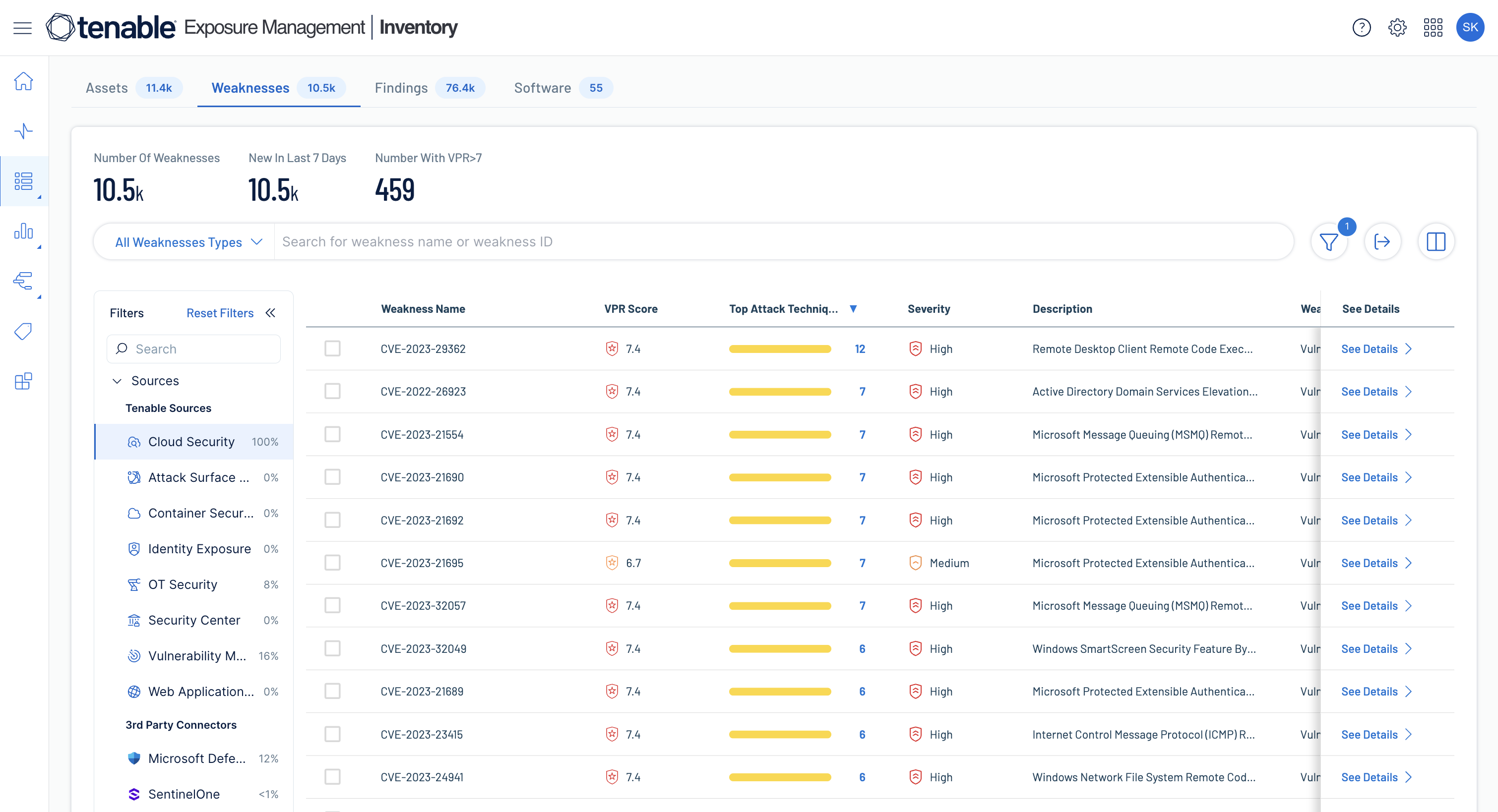
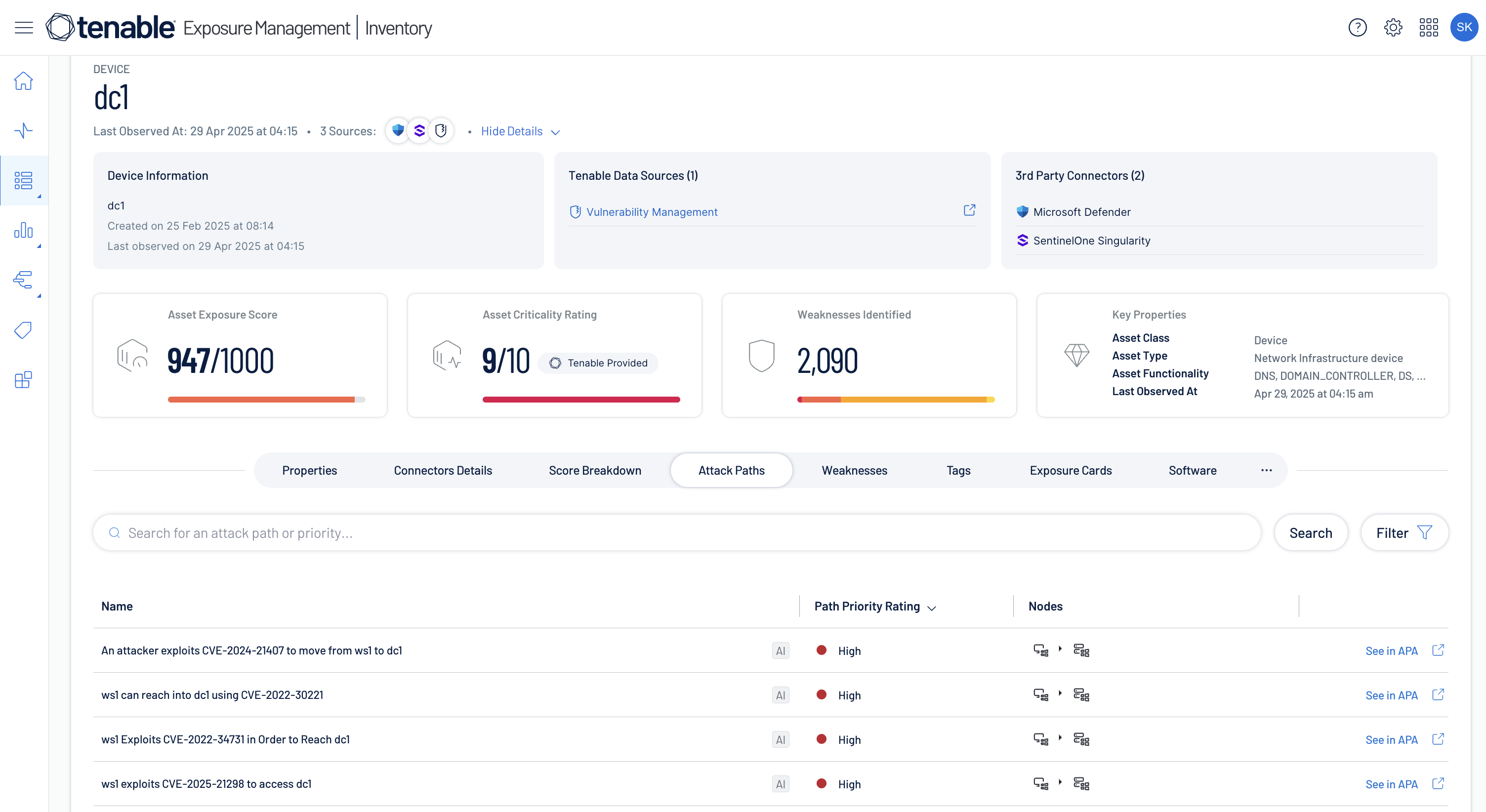
Know your attack surface
Get complete, contextualized asset visibility across your entire attack surface to unify risk assessments for faster remediation.
Learn more about asset inventory -
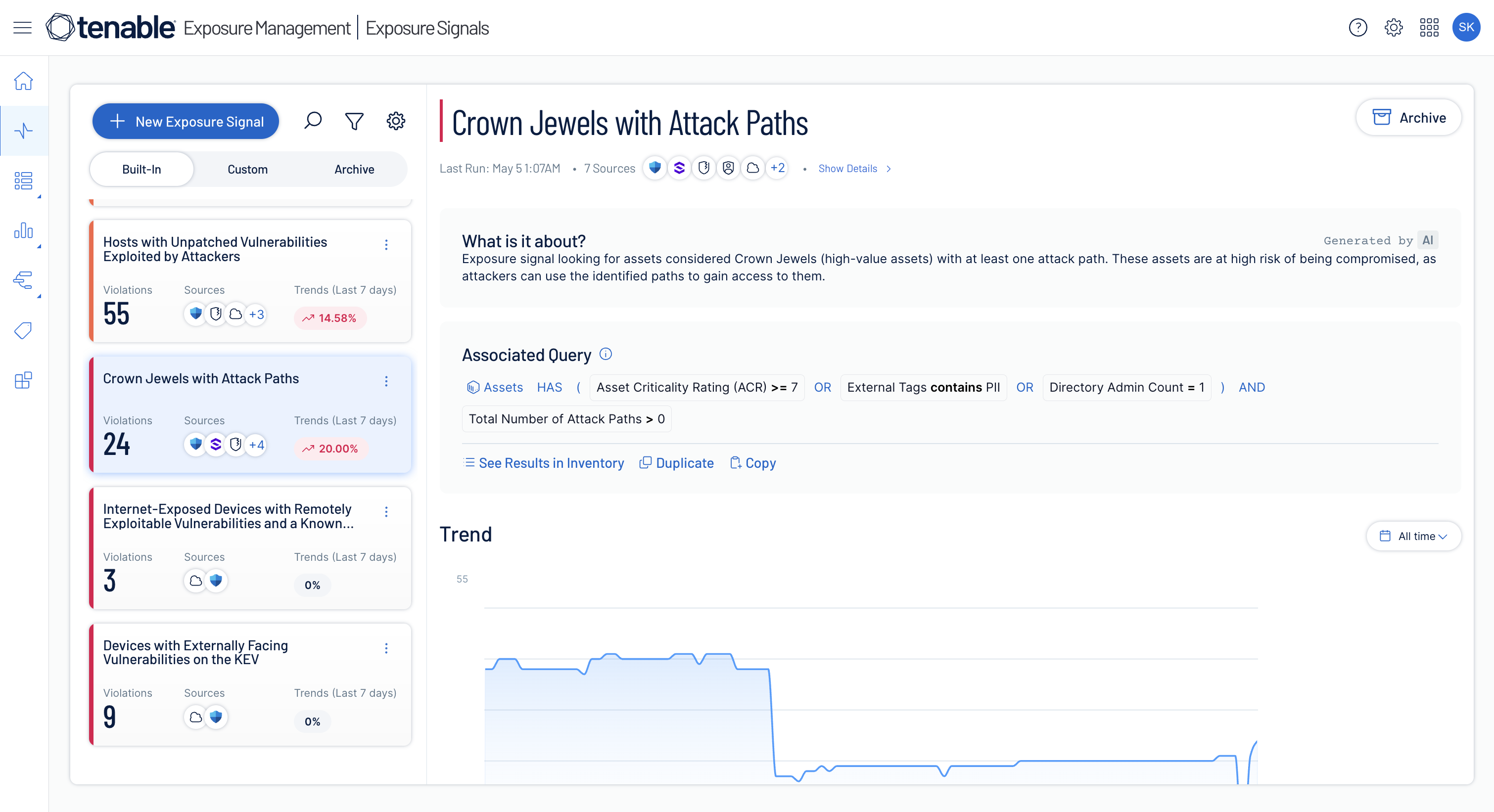
Prioritize exposures that matter
Normalize risk scoring across domains to pinpoint critical attack paths and toxic risk combinations, ensuring prioritized remediation aligned with business needs.
Learn more about exposure prioritization -
Streamline risk management
Use a dynamic policy engine to map and track risks, enabling tailored hygiene policies and rapid violation prioritization.
Learn more about cyber hygiene -
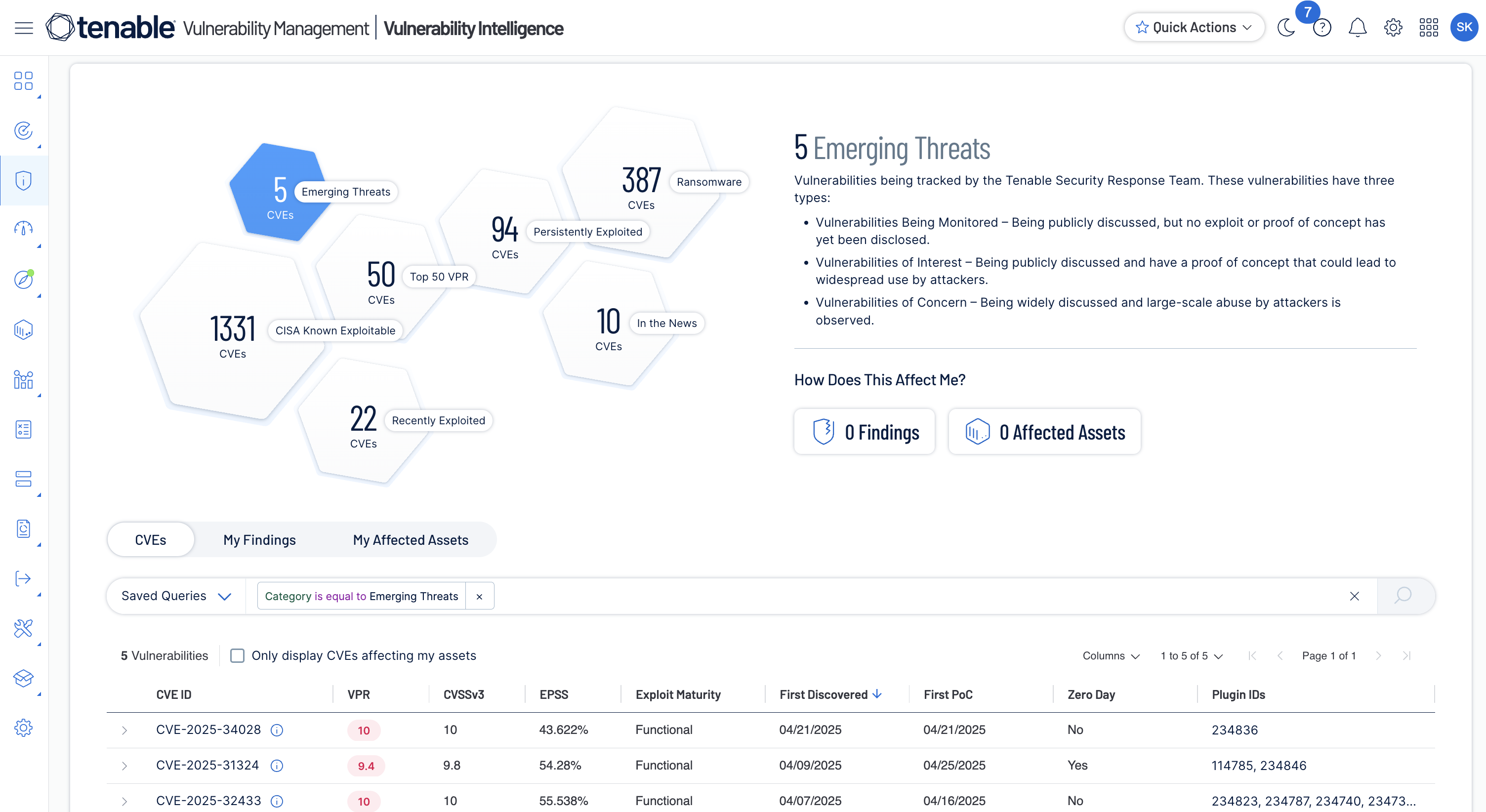
Respond to emerging threats
Track exposures in real time with historical threat context to streamline vulnerability prioritization and remediation efforts.
Learn more about emergency response -
Accelerate threat analysis
Unify asset visibility and contextual risk intelligence to accelerate investigations while reducing response time, tuned for all roles.
Learn more about threat investigation
Realize better outcomes with Tenable One
Tenable One customers see measurable improvements in security posture and business outcomes.
with technology
Related resources
Get Started with Tenable One
Tenable One has helped our engineers reduce the time spent on manual tasks by 75%, which allows them to focus on actual engineering work.
- Tenable One