Media room
Tenable news, announcements and global media coverage
Welcome to the Tenable media room. Read our latest announcements and media coverage, find global contact information and download our media kit below.
Tenable Newsletter
Subscribe to the Tenable newsletter
From innovative product releases to industry research reports to strategic partnerships, get the latest Tenable news and official announcements delivered straight to your inbox.
Form ID: 3042
Form Name: newsletter
Form Class: c-form c-form--request-demo c-form--mktoRow-column-display c-form--mkto js-mkto-no-css js-form-hanging-label c-form--compact
Form Wrapper ID: newsletter-form-wrapper
Confirmation Class: newsletter-confirmform-modal
Simulate Success
Press releases

Tenable Integrates Generative AI Capabilities Across Cybersecurity Platform With Launch of ExposureAI

Tenable Enhances OT Security To Give Organizations the Most Comprehensive Visibility and Management of IT/OT Devices in Operational Environments

Tenable Improves Shift-Left Cloud Security to Prevent Vulnerable Containers From Reaching Runtime
News
Nathan Wenzler discusses the impact of the great reshuffling on cybersecurity
Microsoft fixes two-year-old MSDT vulnerability in August update
Guy March of Tenable lays out the channel angle on Security.
Nationale Cybersicherheitsstrategie erfordert Cyberhygiene
Media kit
Download the Tenable media kit, complete with company and product logos and usage guidelines, executive headshots and the corporate fact sheet.
Contact corporate PR at [email protected]


Tenable One
Request a demo
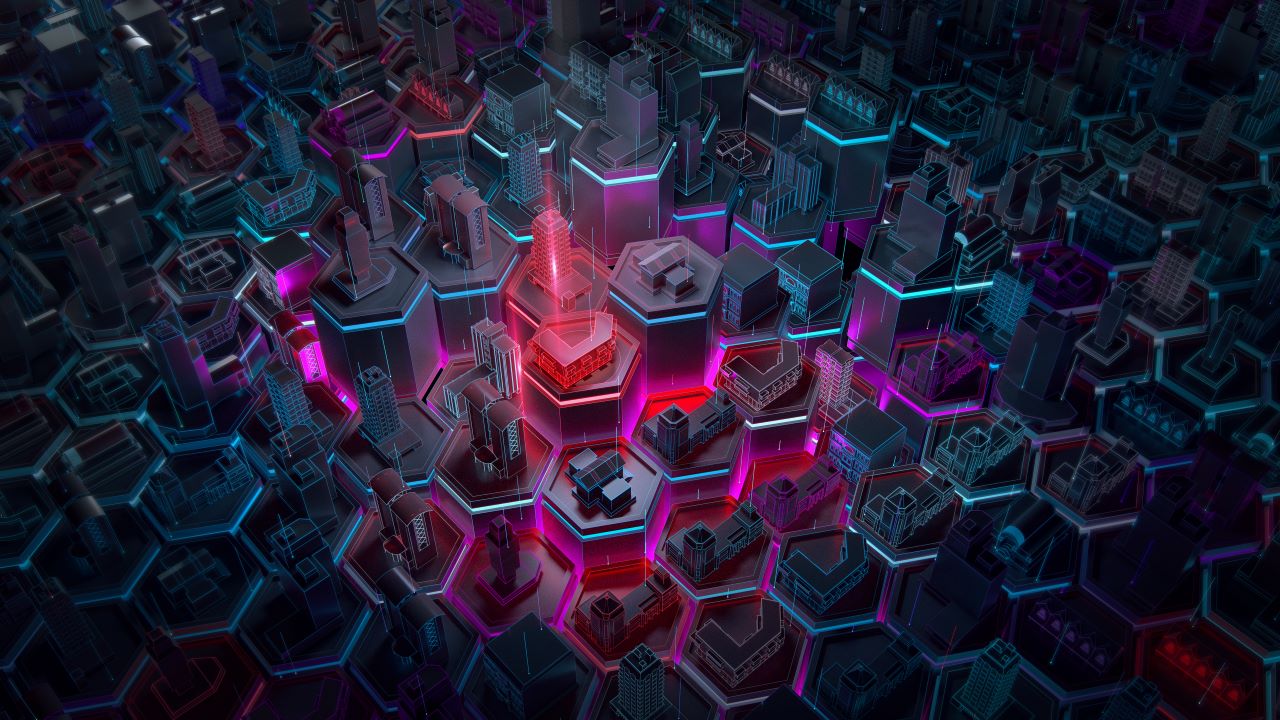
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success