Tenable
One
Take action on cyber exposure with Tenable One, the world’s leading AI-powered exposure management platform for the AI era.
Built on the industry’s most complete exposure dataset, Tenable One prioritizes, investigates, and remediates risk with precision and speed to reduce exposure at scale.
Take command of your entire attack surface
Tenable delivers a better solution that continues to evolve to meet the needs of CISOs... I love the way the Tenable One Exposure Management Platform delivers vulnerability coverage across the expanded attack surface, including cloud and Active Directory. From a single, unified view, cybersecurity teams can see all types of assets and vulnerabilities to understand their risk exposure and prioritize remediation efforts.
Tenable One Exposure Management Platform
Risk Reduction Outcomes
-
Complete Exposure Visibility
-
Attack Path Visualizations
-
Predictive Risk Prioritization
-
Automated Remediation
-
Business-Aligned Risk Metrics
-
Hexa Agentic Layer
-
Tenable Built-in, Third Party and Customer-built Agents
- Workflows
- Remediation
- Orchestration
- Verify Exploitability
-
Exposure Data Fabric
-
-
Analyze
-
Correlate
-
Enrich
-
Verify Exploitability
-
Score Risk
-
Map Relationships
-
-
Surfaces and Signals
-
300+ Data Integrations
Tenable Sensors
Threat Intelligence
AI Systems & Models

All types of assets. All exposures. All in.
The market-leading exposure protection platform spanning the entire modern attack surface, Tenable One enables organizations to expose and close cyber weaknesses anywhere to reduce business risk everywhere.
Realize better outcomes with Tenable
See what customers are saying about Tenable One Exposure Management Platform
FAQs
-
What is Tenable One?
-
Tenable One is an exposure management platform. It helps organizations gain broad attack surface visibility, prevent attacks, and accurately communicate cyber risk to support optimal business performance.
The platform combines the broadest vulnerability coverage spanning IT, OT, IoT, cloud resources, containers, web apps, and identity systems. It builds on the speed and breadth of vulnerability coverage from Tenable Research and adds comprehensive analytics to prioritize remediation actions and communicate cyber risk. Tenable One allows organizations to:
- Gain comprehensive visibility across the modern attack surface
- Anticipate threats and prioritize efforts to prevent attacks
- Communicate cyber risk to make better decisions
-
Which Tenable products are included in Tenable One?
-
Tenable One includes the following Tenable product domains.
-
Which capabilities are included in Tenable One?
-
Capabilities include:
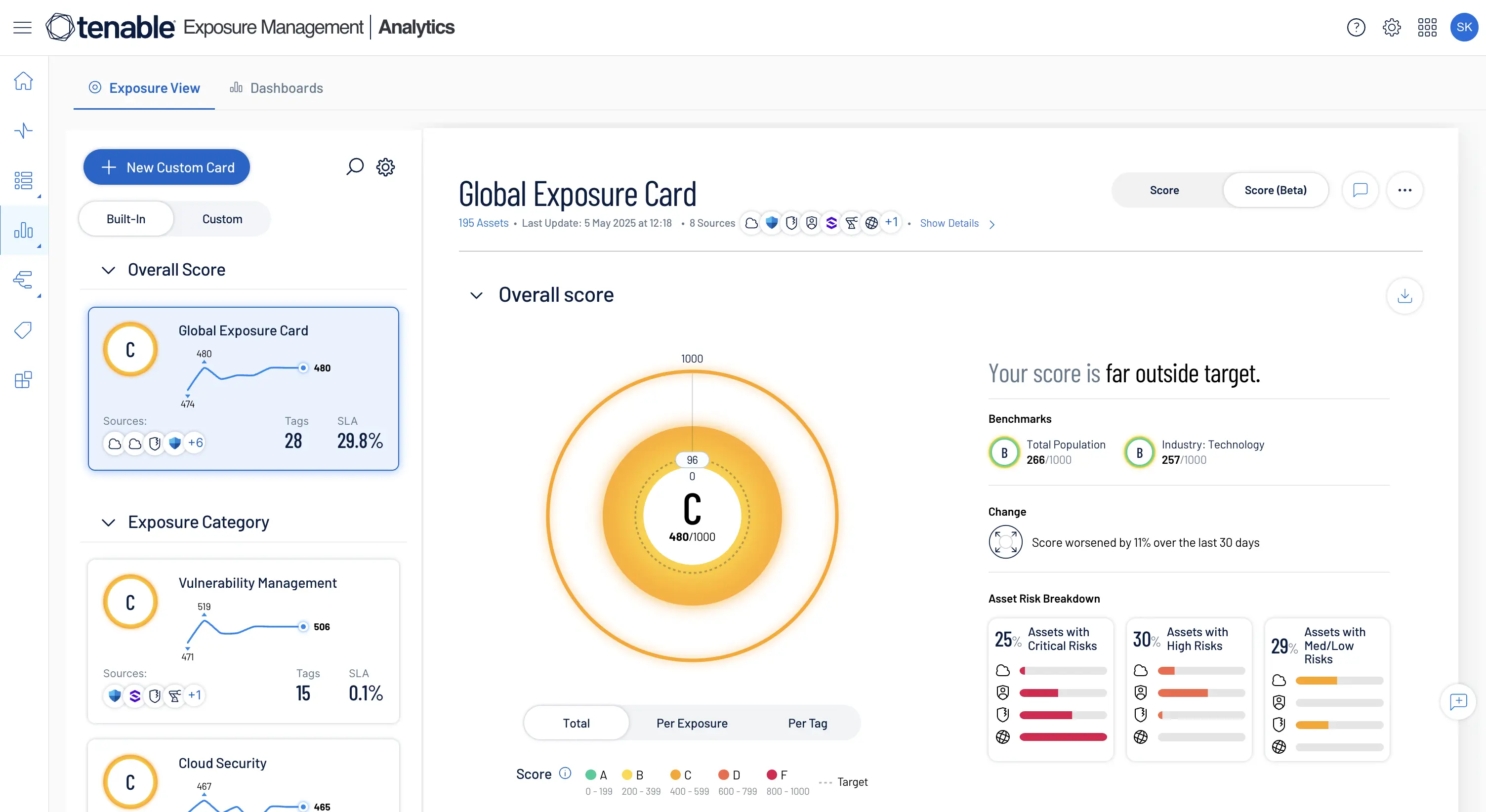
- Exposure view enables focused security efforts through clear, concise insight into your organization’s security exposure. It helps you answer critical questions like: “How secure are we?” “Where do we stand in our preventative and mitigation efforts?” “How are we doing over time?” “What are the key events?”
- Unified dashboards, powered by native and third-party data, give you deep, actionable insights into exposure across the entire attack surface. With pre-built and customizable dashboards, you can analyze risk, drill into key metrics, track progress over time, and clearly communicate insights to stakeholders to drive better decisions and stronger security outcomes.
- Tag performance addresses which tags make up an exposure card and how much that group of assets contributes to a given exposure score.
- Attack path analysis (APA) shows you how threat actors can exploit weaknesses to move across your environment. With more than 150 supported attack techniques, APA continuously monitors gaps across endpoint, identity, and cloud to proactively visualize attack paths and mitigate high-risk exposures. It performs this function by mapping critical risks to the MITRE ATT&CK framework to visualize all viable attack paths continuously — both on-prem and in the cloud.
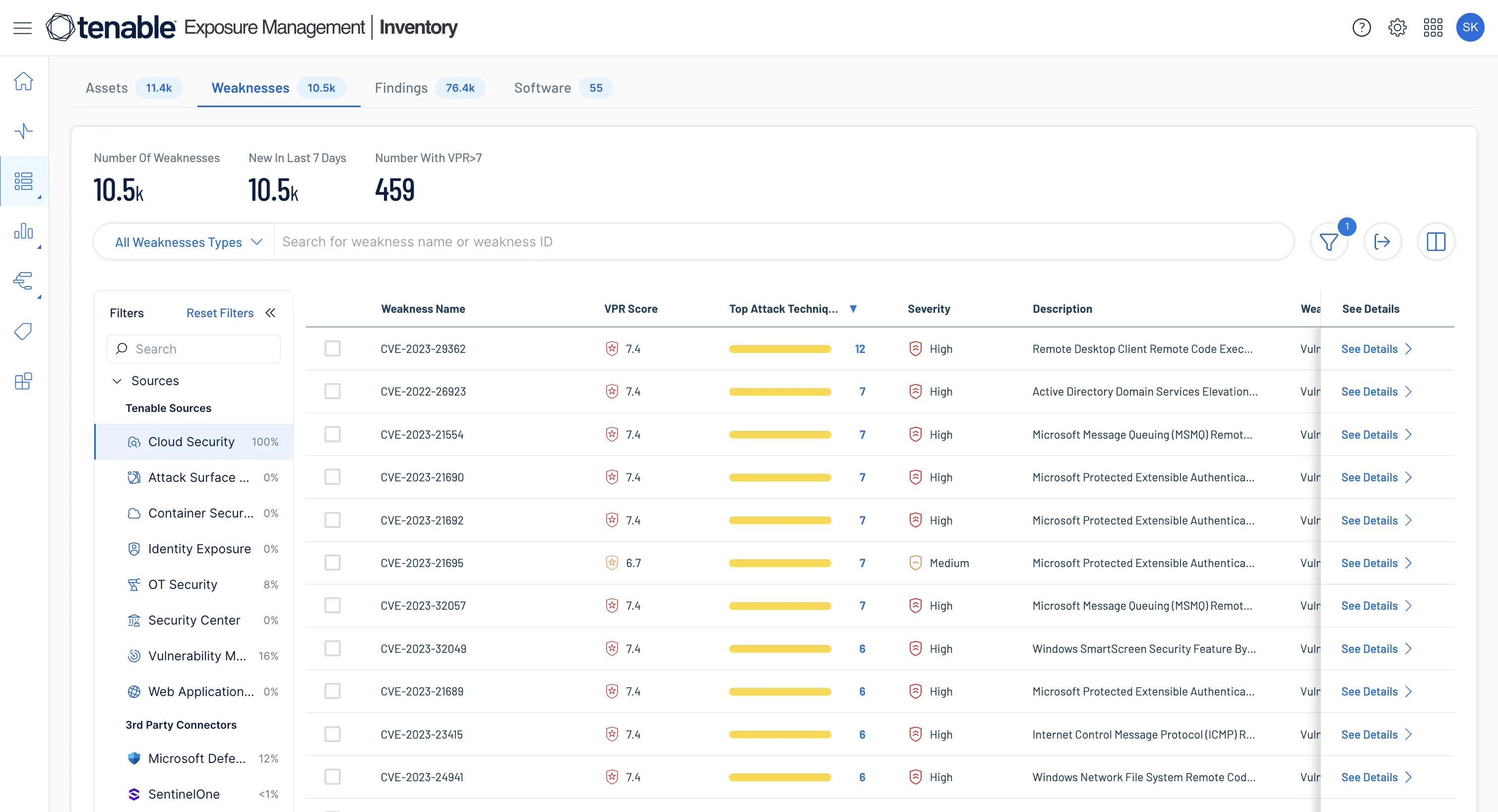
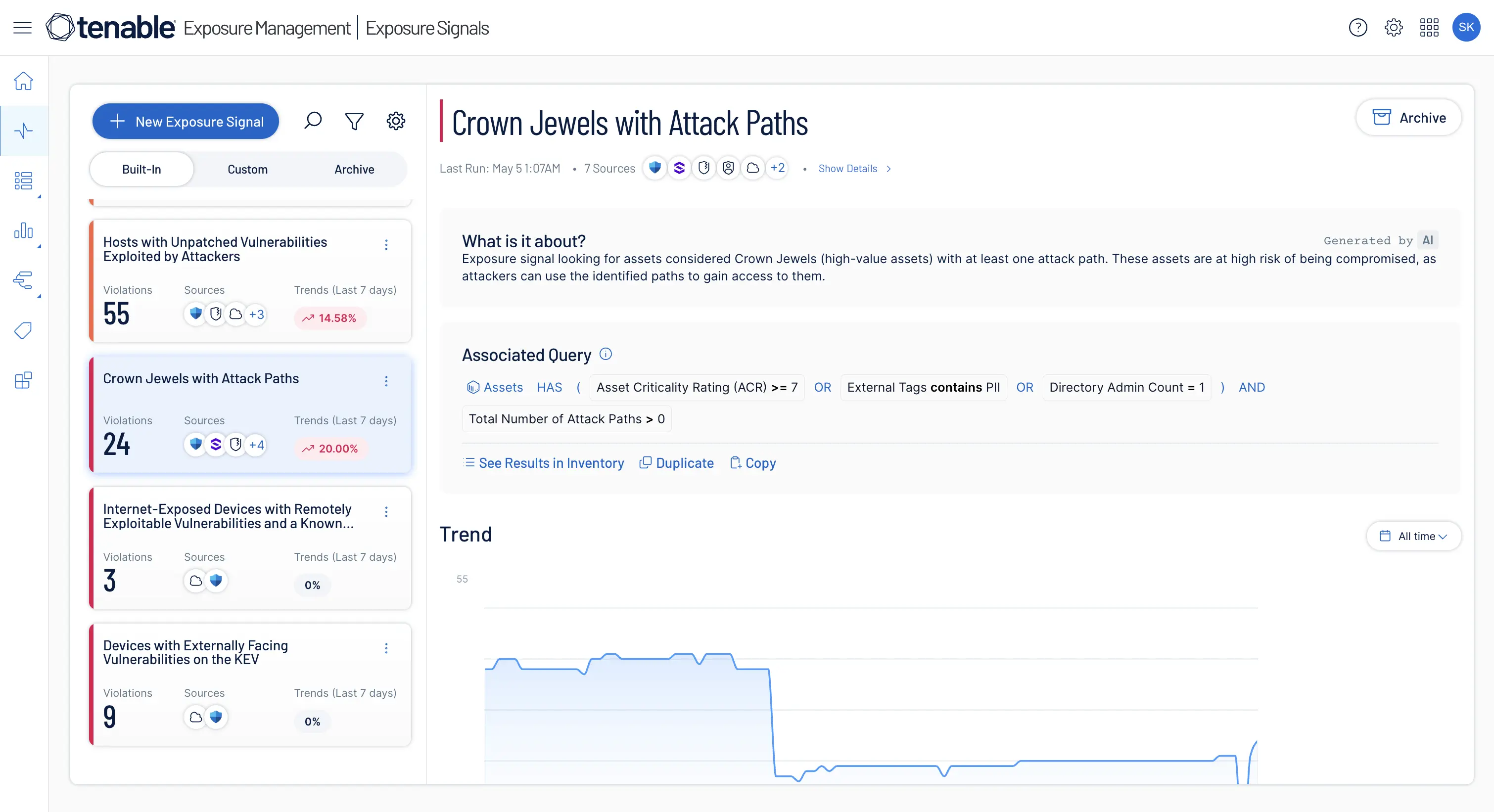
- Exposure signals are a cross-domain prioritization capability designed to identify toxic combinations of vulnerabilities, identities, threats, installed software, and assets that amplify organizational risk. By fusing Tenable sensor data with risk-scoring metrics and asset context (e.g., criticality, ownership), you can surface high-exposure scenarios that require immediate remediation.
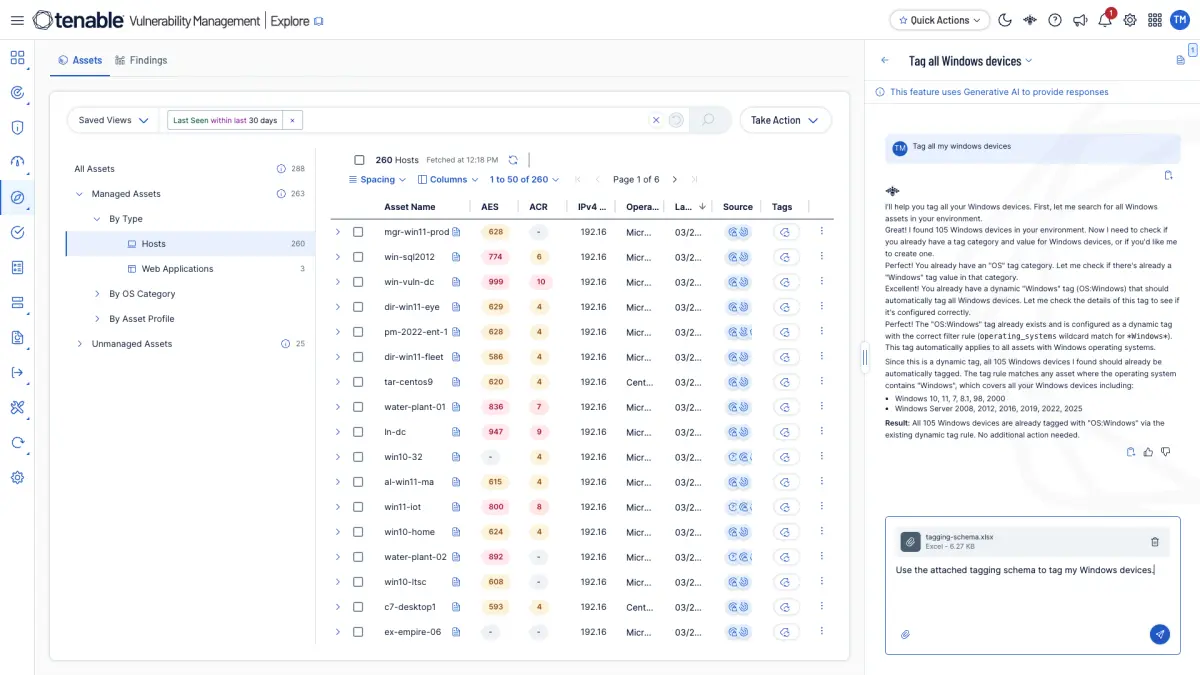
- Asset inventory provides a centralized view of all assets, weaknesses, and tags, including IT, OT, IoT, cloud, identities, and web apps, with the ability to create specific asset tags from a variety of sources.
- External attack surface management (EASM) offers insight into your external attack surface, empowering your organization to identify and reduce risks from the attacker’s perspective.
- Custom exposure cards enable concise, flexible communication of specific security insights.
- News integration with Tenable Research blogs allow for creation of custom exposure cards that reflect cybersecurity developments.
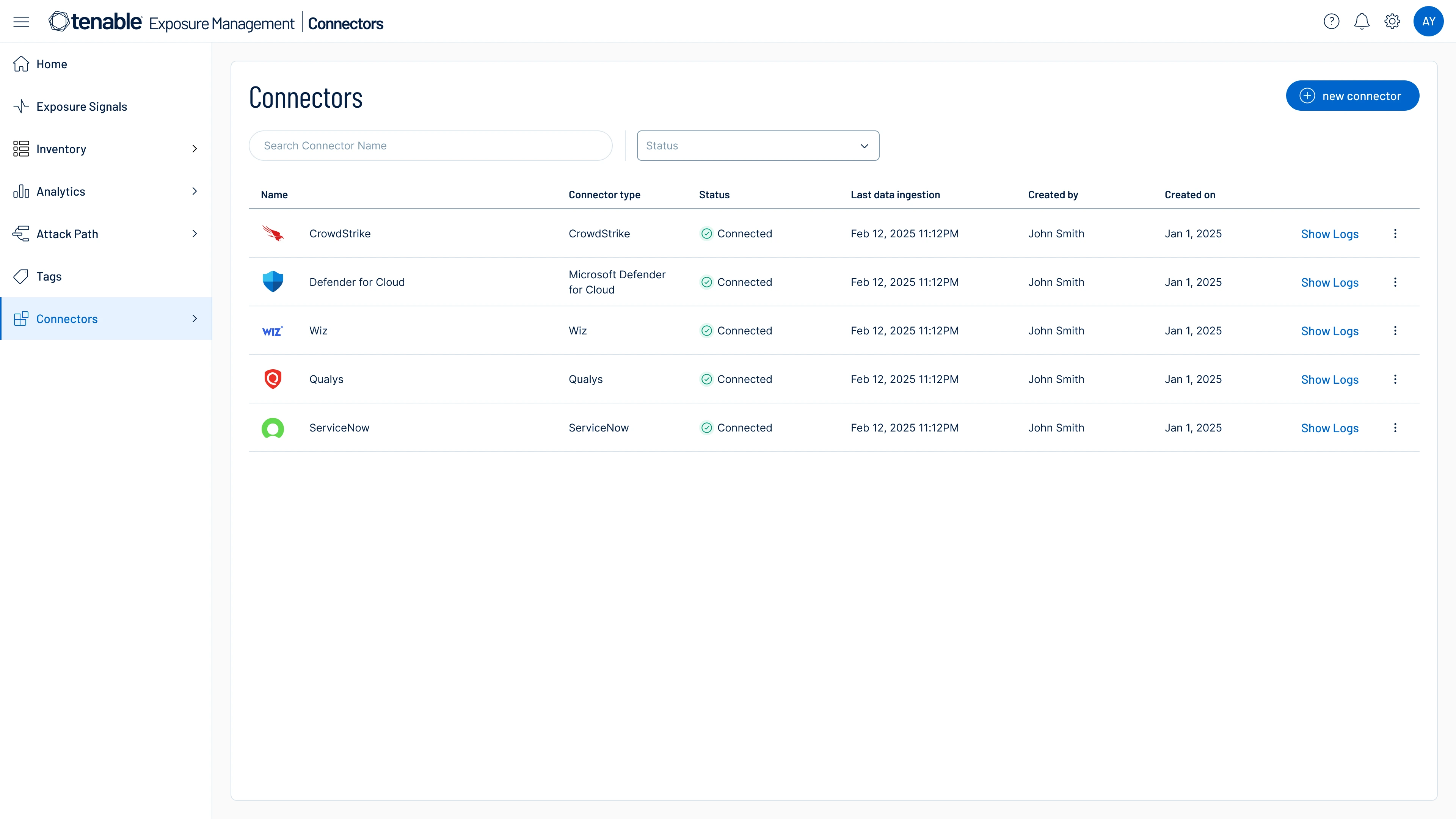
- Tenable One Connectors bring in data from other vulnerability management, application security, cloud security, endpoint security, OT security, and asset inventory and management systems to provide a fully unified, contextual view of risk across your entire attack surface.
-
How does Tenable leverage AI across its exposure management platform?
-
Tenable's use of AI for exposure management includes generative AI, deep learning, and machine learning. It empowers your security teams to make informed decisions that enhance prioritization, resilience, and democratize access to advanced threat analysis and mitigation guidance.
- Generative AI assistant: Tenable’s ExposureAI leverages generative AI and deep learning to accelerate analysis, simplify insights, and drive faster, more effective security decisions — empowering organizations to proactively manage and reduce their cyber exposure.
- Exposure prioritization: Tenable uses patented machine learning models for advanced prioritization, including vulnerability priority rating (VPR), OS prediction from network data, and predictive scoring for assets. This helps teams focus on a small percentage of vulnerabilities most likely to be exploited, improving remediation effectiveness.
- AI risk visibility and management: Tenable AI Aware is a proactive solution that gives security teams visibility into AI usage and development within their environments. It helps them detect unauthorized AI usage, surface vulnerabilities, and manage AI-related risks across the enterprise.
- Securing AI workloads in the cloud: Tenable’s AI Security Posture Management (AI-SPM) helps organizations identify and fix risks in AI workloads across cloud environments, ensuring secure configuration, governance, and visibility of AI resources.
-
What types of third-party connectors are available in Tenable One?
-
Tenable One offers a broad range of third-party connectors across vulnerability management, application security, cloud security, endpoint security, OT security, and asset inventory and management. We're continuously expanding our ecosystem by adding more connectors and supporting new security categories. Explore all connectors.
-
How does Tenable One manage third-party data?
-
All data ingested into Tenable One is fed into our exposure data lake, where it is combined with Tenable sensor data and native exposure intelligence. Our AI-driven ingestion engine then correlates, normalizes, and deduplicates the data, ensuring you are left with a clean and accurate view of risk. This creates a consistent, structured semantic layer, which reduces manual intervention and enhances data accuracy, context, and usability.
-
Is Tenable One cloud-based?
-
Yes, Tenable One is mainly a cloud-based solution. However, customers can deploy their vulnerability management assets in the cloud with Tenable Vulnerability Management and/or on premises with Tenable Security Center Plus.




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success