by David Schwalenberg
January 20, 2015
If systems and users on the network have unauthorized connections to the Internet, the network has a greater risk of being compromised. But how can this unauthorized activity be found?
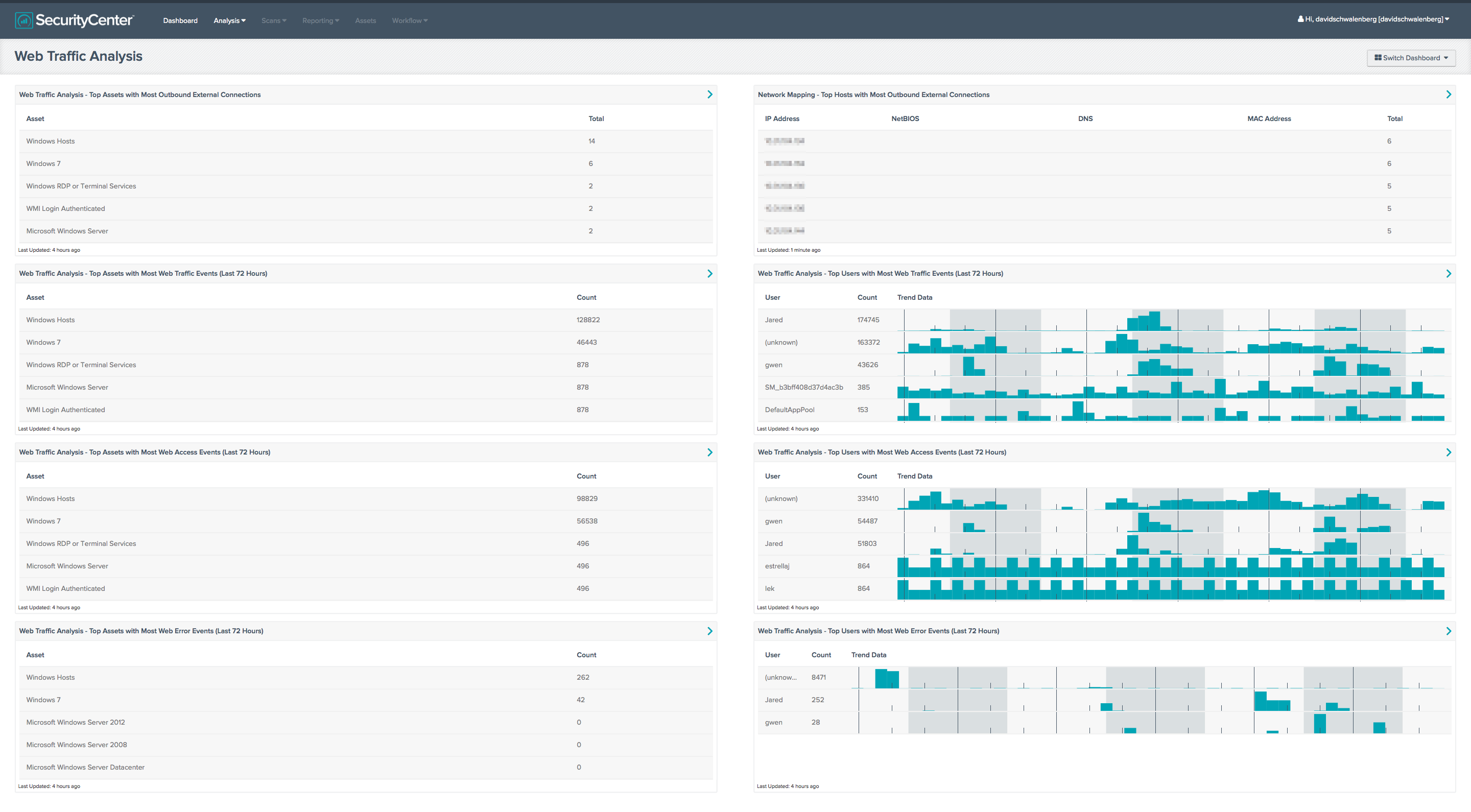
This dashboard displays the top asset groupings containing systems that have generated web traffic and the top user accounts associated with web traffic events. Assets can be created for different sections of the network and/or classes of machines, enabling an analyst to use this dashboard to discover if any systems are generating unauthorized web traffic. An analyst can also use this dashboard to discover if any user accounts are generating unauthorized web traffic. This information can assist the organization as it seeks to reduce its chances of network compromise by eliminating unauthorized web activity from critical systems, such as servers and point-of-sale systems, and from privileged user accounts, such as administrative accounts.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.1
- PVS 4.0.3
- LCE 4.4.1
- Tenable Network Monitor
- Tenable NetFlow Monitor
Tenable's SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with the Tenable Passive Vulnerability Scanner (PVS), as well as log correlation with the Tenable Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network.
Listed below are the included components:
- Web Traffic Analysis - Top Assets with Most Outbound External Connections - This table displays the asset groupings that contain systems that have outbound external connections. The list of assets is ordered so that the asset with the largest number of systems with outbound external connections is at the top. An outbound external connection means a system with an IP address in the internal network range (set in the PVS configuration) is talking to a system with an IP address outside of the internal network range. Assuming that assets have been created for different sections of the network and/or classes of machines, an analyst can use this table to discover if any systems have unauthorized connections to external IP addresses.
- Web Traffic Analysis - Top Assets with Most Web Traffic Events (Last 72 Hours) - This table displays the asset groupings that contain systems that have generated network traffic events in the last 72 hours on either port 80 or 443, as recorded by the Tenable Network Monitor and the Tenable NetFlow Monitor. The list of assets is ordered so that the asset with the largest number of traffic events is at the top. Assuming that assets have been created for different sections of the network and/or classes of machines, an analyst can use this table to discover if any systems are generating unauthorized web traffic.
- Web Traffic Analysis - Top Assets with Most Web Access Events (Last 72 Hours) - This table displays the asset groupings that contain systems that have generated network traffic events in the last 72 hours of type = web-access. The list of assets is ordered so that the asset with the largest number of traffic events is at the top. Assuming that assets have been created for different sections of the network and/or classes of machines, an analyst can use this table to discover if any systems are generating unauthorized web traffic.
- Web Traffic Analysis - Top Assets with Most Web Error Events (Last 72 Hours) - This table displays the asset groupings that contain systems that have generated network traffic events in the last 72 hours of type = web-error. The list of assets is ordered so that the asset with the largest number of traffic events is at the top. Assuming that assets have been created for different sections of the network and/or classes of machines, an analyst can use this table to discover if any systems are generating unauthorized web traffic.
- Network Mapping - Top Hosts with Most Outbound External Connections - This table presents information on those hosts with the most passively detected outbound external connections. The table is sorted so that the host with the highest count of detections is at the top. This information can assist an organization in understanding who is talking to whom, as well as detecting any unauthorized or suspicious host connections. The Total column displays the number of detections. This number of detections may be greater than the number of external hosts to which this host is connecting, as multiple connections to the same host may have been detected. Note that only passively detected outbound external host connections will be displayed, and this may not include all possible external connections.
- Web Traffic Analysis - Top Users with Most Web Traffic Events (Last 72 Hours) - This table displays the user accounts associated with network traffic events in the last 72 hours on either port 80 or 443, as recorded by the Tenable Network Monitor and the Tenable NetFlow Monitor. The list of user accounts is ordered so that the user account associated with the largest number of traffic events is at the top. An analyst can use this table to discover if any user accounts are generating unauthorized web traffic.
- Web Traffic Analysis - Top Users with Most Web Access Events (Last 72 Hours) - This table displays the user accounts associated with network traffic events in the last 72 hours of type = web-access. The list of user accounts is ordered so that the user account with the largest number of traffic events is at the top. An analyst can use this table to discover if any user accounts are generating unauthorized web traffic.
- Web Traffic Analysis - Top Users with Most Web Error Events (Last 72 Hours) - This table displays the user accounts associated with network traffic events in the last 72 hours of type = web-error. The list of user accounts is ordered so that the user account with the largest number of traffic events is at the top. An analyst can use this table to discover if any user accounts are generating unauthorized web traffic.