by Steve Tilson
May 27, 2014
According to the U.S. Treasury Department, every three seconds an identity is stolen online. With the explosive growth of web technologies, more applications, games, and other services are becoming available on the Internet. This growth has led to new categories of malware capturing credentials, photos, and other forms of sensitive data. This dashboard assists security analysts in identifying systems vulnerable to information or data stealing malware techniques.
This type of malware often poses as legitimate software or uses social engineering to trick users into executing the malware. More advanced information stealing malware does not require a user’s interaction and can cause the same if not more damage. Although early detection for any type of malware is critical, this type of malware is capable of stealing account numbers, financial data, social security numbers, and user accounts for malicious purposes. Information gathered through stealing malware can be catastrophic to businesses as well as personally. While any information gathered and stolen is unacceptable, using SecurityCenter the proper steps can be taken to locate and reduce the Cyber Exposure associated with the malware.
SecurityCenter CV detects and monitors vulnerabilities from many sources, such as event logs, active scanning and passive detection using Nessus, LCE, and Nessus Network Monitor to locate and identify potential malware. This dashboard assists analysts by monitoring and auditing windows processes, services, and suspicious logins for potential information stealing malware. As well, Malicious Process Detection plugins are used to monitor for the associated MD5 hashes identified by the FBI.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located under the category Security Industry Trends. The dashboard requirements are:
- SecurityCenter 5.5.1
- Nessus 6.11.1
- LCE 5.0.2
- Nessus Network Monitor 5.3.0
Tenable SecurityCenter Continuous View® (SecurityCenter CV™) is the market-defining continuous network monitoring solution, which assists organizations in tracking vulnerabilities within the enterprise. SecurityCenter CV™ is continuously updated with information about advanced threats, zero-day vulnerabilities, and new forms of regulatory compliance. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. SecurityCenter CV™ provides an organization with the most comprehensive view of the network and actionable information to support mitigation efforts and reduce cyber risk.
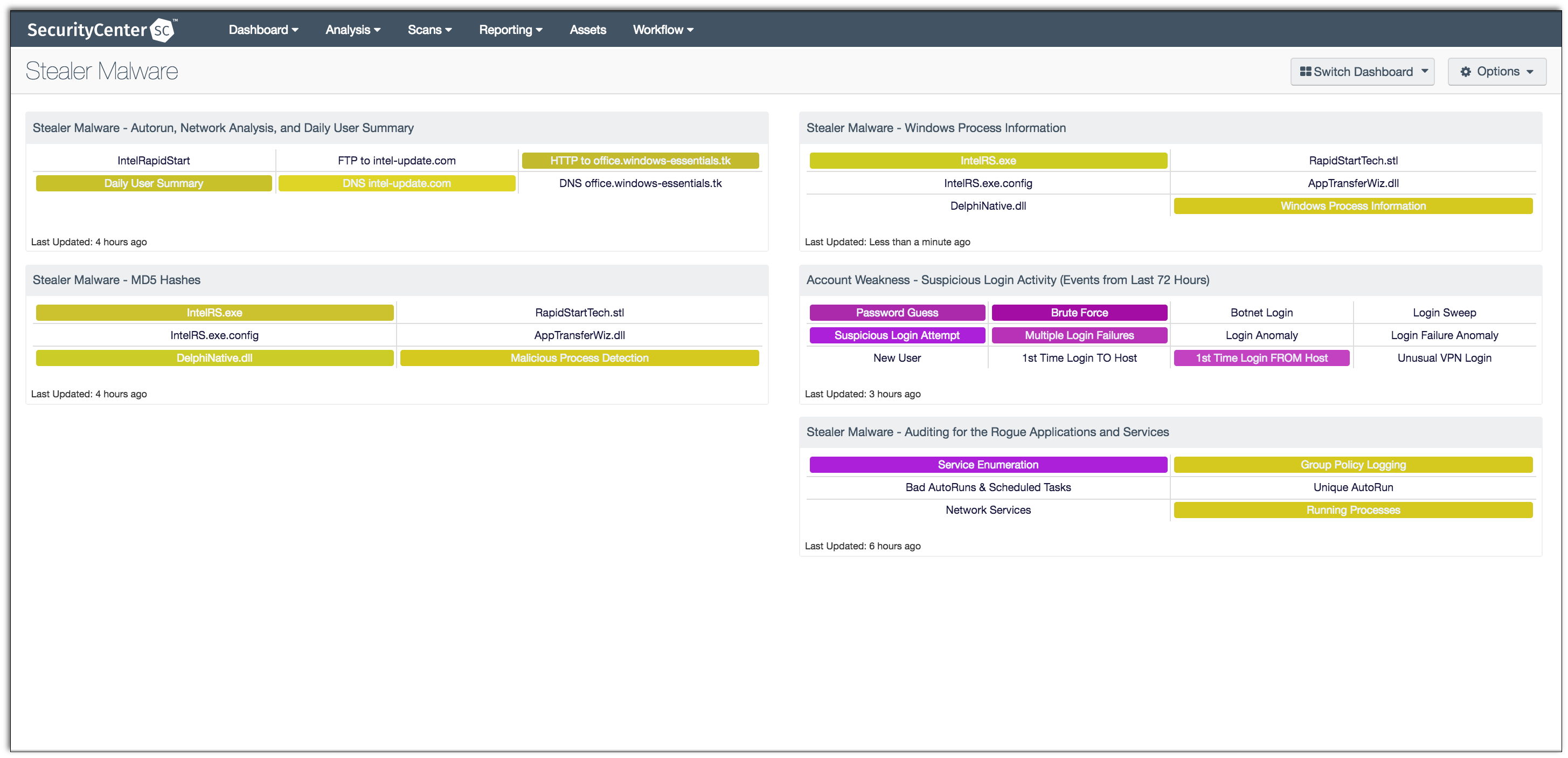
This dashboard contains the following components:
Stealer Malware - Autorun, Network Analysis, and Daily User Summary: This component encompasses several aspects of SecurityCenter CV by monitoring Windows Logon AutoRuns, vulnerabilities based on port 80, 21 containing the strings 'intel-update.com', and 'office.windows-essentials.tk'. The LCE also monitors for command usage with Daily User Summary alerts, and DNS queries for the aforementioned strings. Nessus plugin 70621, "Microsoft Windows AutoRuns Logon", includes the most common startup locations used by programs. These autorun commands are commonly associated with programs that start automatically when a computer is turned on, users log in, users log off, and remote sessions are started. Such keys can be set from a program installation, GPO, or through a malicious process to maintain persistence.
Stealer Malware - Auditing for the Rogue Applications and Services: This component covers several aspects of monitoring, starting with GPO Events captures in logs to identifying unique services on systems. The Service Enumeration indicator uses plugin 10456 to identify services using the SMB protocol; a list of active and inactive services are listed for each host. The Bad AutoRuns & Scheduled Tasks indicator uses plugin 74442 to identify systems with registry entries that are known to be associated with known malware identified by threat intelligence from ThreatGRID. The Network Services indicator uses plugin 11154 to report when banners were retrieved, but Nessus was unable to determine the service running. The Unique AutoRuns uses plugin 70628 to gather the autorun entries from similar machines and compare the output against each other to find unique entries. The Running Processes indicator uses plugin 70768 to identify when one or more running processes on the remote Windows host are not present in a database of 'known good' or 'known bad' software.
Stealer Malware - MD5 Hashes: This component uses the Malicious Process Detection plugins to monitor for the associated MD5 hashes identified by the FBI. Additionally, an indicator is used to help identify all the Malicious Process Detection plugins currently in SecurityCenter. There are several plugins to identify malicious processes, of which some focus on operating systems such as Windows, Linux, or Mac OS X. Others allow for security administrators input their own MD5 hashes and check for MD5 hashes identified by Mandiant.
Account Weakness - Suspicious Login Activity (Events from Last 72 Hours): This matrix shows potentially suspicious login activity. This activity can bring attention to accounts that are more threatened and require greater protection.
Stealer Malware - Windows Process Information: This component monitors Microsoft Windows process information. While the plugin is mostly informative, this indicator uses the plugin for forensic investigation and malware detection purposes. The filters apply the name of the process in the vulnerability text field and change color to yellow when matched.