by Michael Willison
August 13, 2014
This dashboard will monitor trending, events, and vulnerabilities for spam security risks in the network. Spam is unsolicited email sent in bulk to unsuspecting users for commercial or malicious purposes. By using spam filters, organizations can eliminate some spam emails, but spammers are always developing new ways of getting these emails out. Monitoring spam and inbound communications are critical to good security practices. The ability for LCE and PVS to monitor emails through logs and passive vulnerability detection can provide a much more in-depth view into communication exchanges.
Email servers and spam gateways should be configured to send log data to LCE and be passively monitored by PVS. The PVS scanners should also be configured to send real-time syslog data to LCE. If an anti-spam appliance is not yet supported with normalized events by LCE, the organization should contact Tenable Customer Support and provide unnormalized log types. Once the LCE team creates the normalization rules, they will be uploaded to the LCE via the scheduled updates.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.1
- Nessus 5.2.7
- PVS 4.0.2
Listed below are the included components:
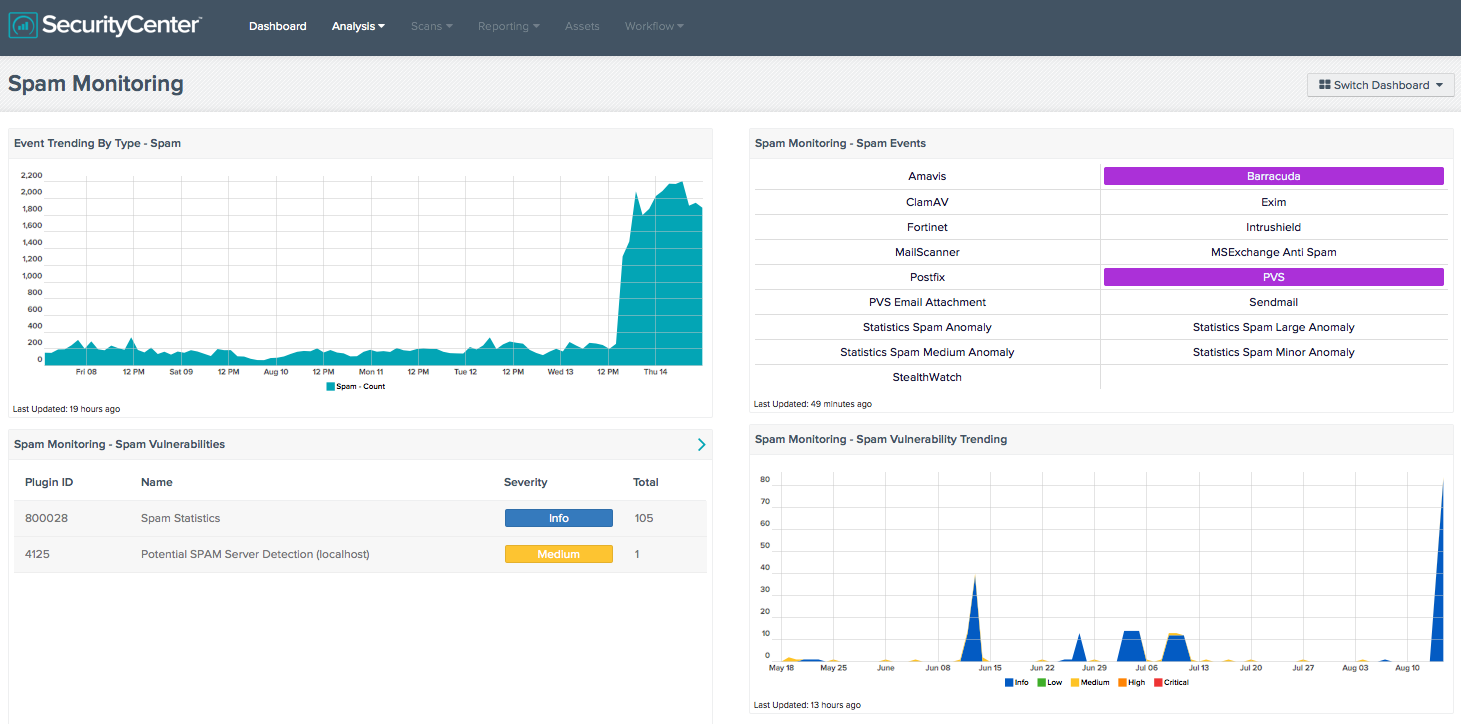
- Event Trending By Type – Spam: This component displays a 7-day trend analysis for logs from email servers, antivirus email tools, SPAM appliances, firewalls, and other sources that indicate spam activity. These are normalized to the LCE spam event type.
- Spam Monitoring - Spam Events: This component provides an indicator for spam events collected from systems with LCE Clients installed, or from systems where syslogs are collected. For each indicator, when a pattern match is found, the indicator will turn purple. Some of the event indicators in the matrix are specific for known applications such as Amavis, Sendmail, and MSExchange Anti Spam servers. Some of the other indicators will provide statistical information on spam anomalies.
- Spam Monitoring - Spam Vulnerabilities: This component provides a table of the top 100 spam vulnerabilities on the network. SecurityCenter CV provides information on vulnerabilities by using both passive and active vulnerability scans to determine what risks are on the network and how IT security teams can best use this information.
- Spam Monitoring - Spam Vulnerability Trending: Trending spam vulnerabilities by severity can be a useful tool for IT security teams. Spam is both a network resource hog and a potential security threat within companies. Whether it is an email advertising a new pharmaceutical drug or a new dating site, it takes up network bandwidth and resources on the SMTP servers on the networks. This trending chart can help an IT security team pinpoint when potential spam started coming into the company, or when one of the company’s SMTP relay server started acting as a spam server.