by Megan Daudelin
June 27, 2016
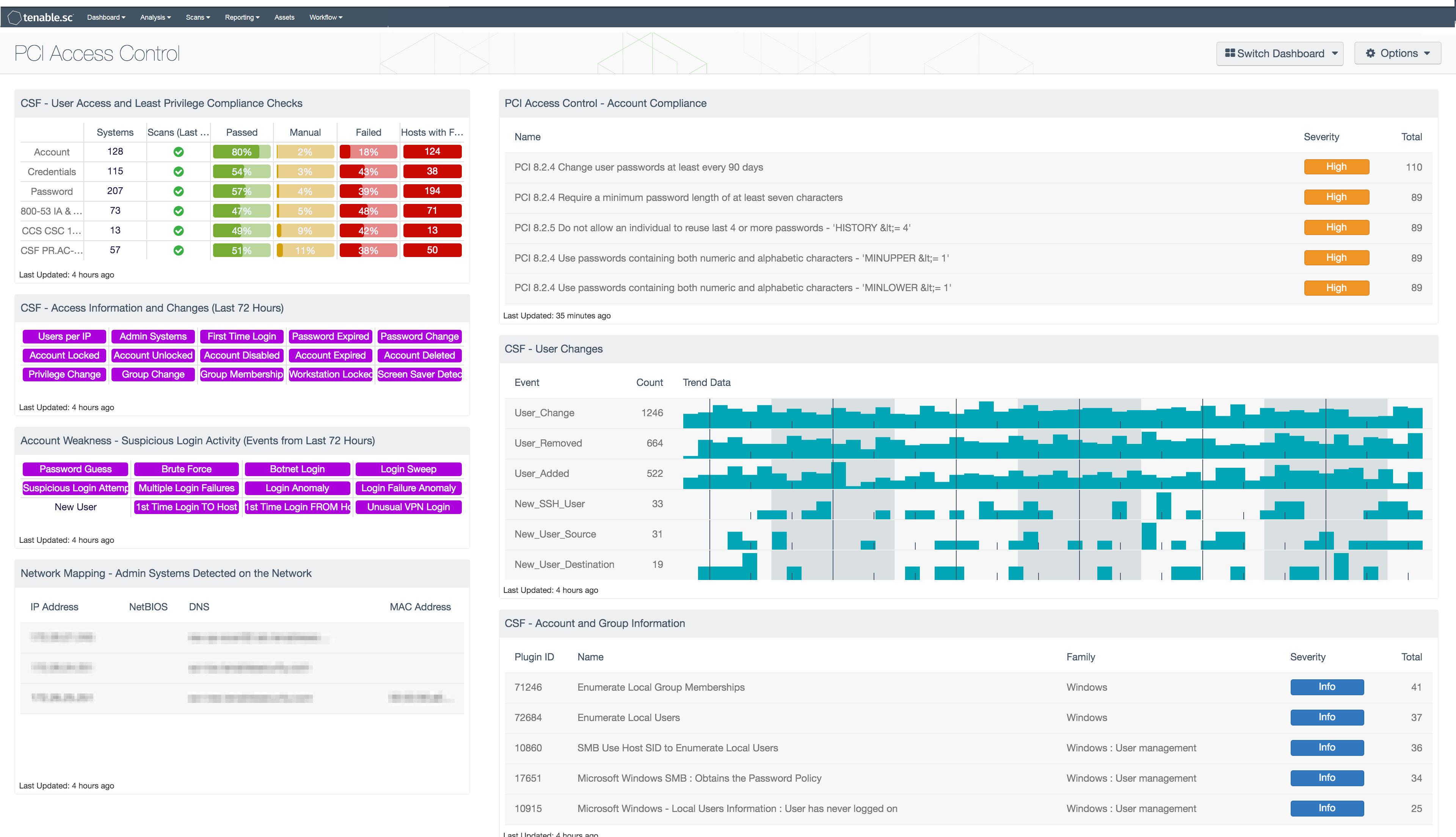
The Tenable.sc Research team created the PCI Access Control dashboard. User accounts are necessary to allow users to perform their assigned duties. Analysts need to be able to monitor and protect user accounts for not only the needs of the organization but to also adhere with PCI security requirements. This dashboard can assist security teams with monitoring access control measures and adhering to PCI requirements. The dashboard is currently available within the Feed.
The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides organizations with technical and operational requirements for organizations accepting or processing payment transactions, and for software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies, and ongoing processes that protect their payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 3.2 released in April 2016. Any organization that handles payment card information has to comply with the PCI DSS and must demonstrate compliance annually. Tenable's Tenable.sc Continuous View (CV) is able to help organizations monitor ongoing PCI DSS compliance by integrating with Tenable Nessus, Tenable Nessus Network Monitor (NNM), and Tenable Log Correlation Engine (LCE).
Users of all access control levels play an important part in all organizations. Some users ensure the security of an organization whereas others further the business goals. Regardless of the user account, if the user account is active and has permissions, there could be a possibility of compromise. Analysts need to ensure that care is taken to protect all user accounts and monitor for suspicious activity. Many organizations have a sense of belief that all user accounts are trusted within the network boundaries and are performing authorized activities. Attackers use various techniques to get credentials of any user account possible to get a foothold into the inside of the organization. Tenable has products such as Nessus, NNM, and LCE to provide organizations with a continual view into the network. Using these products within Tenable.sc CV, analysts can help detect threats to user accounts with tools such as this dashboard.
With this dashboard, organizations can assess their level of adherence with PCI security requirements focusing on access control. The components in this dashboard are focused on PCI requirements 2, “Do not use vendor-supplied defaults for system passwords and other security parameters”; 7, “Restrict access to cardholder data by business need to know”; 8, “Identify and authenticate access to system components”; and 10, “Track and monitor all access to network resources and cardholder data”. The components in this dashboard cover requirements such as 2.2.3, 2.3, 7.1, 7.2, 8.1, 8.2, 8.5, 10.3, and 10.6 that focus on specific access control data detected in the organization.
Within this dashboard, user account focused components are provided to help analysts see activities detected in the organization around user accounts. All user accounts such as regular user accounts and administrative accounts should be monitored for unusual activity. Multiple industry recommendations from standards such as PCI and NIST CyberSecurity Framework (CSF) are provided to help analysts see potential malicious indicators around user accounts. Examples of these indicators, such as privilege changes and group membership changes, alert analysts as changes may not be expected and should be validated. Analysts can use these components to help determine what typical activity should be on a network and then be more aware of when abnormal activity takes place within the organization.
Organizations can configure repositories or asset lists in order to tailor the focus of the dashboard. When the dashboard is added from the Tenable.sc Feed, the appropriate assets, IP addresses, or repositories can be specified. Assigning one of the options to the dashboard will update all filters in the components. By creating static or combination asset lists that include all systems in the Cardholder Data Environment (CDE), each component can be filtered to display results directly related to ongoing PCI security. Using an asset list filter will also allow traffic into and out of the CDE to be monitored. In order to accurately measure an organization’s PCI security posture, asset lists need to be applied as filters to provide results focused on the CDE.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
- NNM 5.9.0
- LCE 6.0.0
Tenable's Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. Tenable Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, NNM, and LCE, Tenable.sc CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
This dashboard contains the following components:
- CSF - User Access and Least Privilege Compliance Checks: This component displays user access and least privilege compliance information in areas such as password requirements, lockout policy after failed logins, and controlled use of administrative privileges.
- CSF - Access Information and Changes (Last 72 Hours): This matrix component can help an analyst quickly pull up information on systems where certain user access-related events and changes have occurred.
- Account Weakness - Suspicious Login Activity (Events from Last 72 Hours): This matrix shows potentially suspicious login activity.
- Network Mapping - Admin Systems Detected on the Network: This table presents those systems that have been observed as the source of an administrator authentication.
- PCI Monitoring - Account Compliance: The “PCI Monitoring - Account Compliance” table component lists account compliance plugin detections that match various security standards.
- CSF - New Users and User Changes: The New Users and User Changes component presents data on new and existing user events on the network over the past 72 hours.
- CSF - Account and Group Information: This table displays detections of account and group information, such as accounts that have never been logged into, disabled accounts, and group user lists.