by Josef Weiss
October 10, 2016
Incident response is a broad area that not only involves breaches and malicious software, but also involves the handling of unauthorized access from internal or external sources, misuse of systems, and data loss. Without proper incident response procedures, organizations may spend a considerable amount of time and resources recovering from these incidents. Malicious activities may continue to proliferate through critical systems, allowing attackers additional opportunities to exploit more systems and exfiltrate more data. Undetected long-term malicious activity may jeopardize an organization’s competitiveness and long-term survival.
The federal government relies heavily on external service providers and contractors to assist in carrying out a wide range of federal missions. Sensitive but unclassified federal information is routinely processed by, stored on, or transmitted through nonfederal information systems. Failing to properly protect this Controlled Unclassified Information (CUI) could impact the ability of the federal government to successfully carry out required missions and functions.
The National Institute of Standards and Technology (NIST) created Special Publication 800-171 "Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations" to provide recommended requirements for protecting the confidentiality of CUI. Federal agencies should use these requirements when establishing contracts and agreements with nonfederal entities that process, store, or transmit CUI.
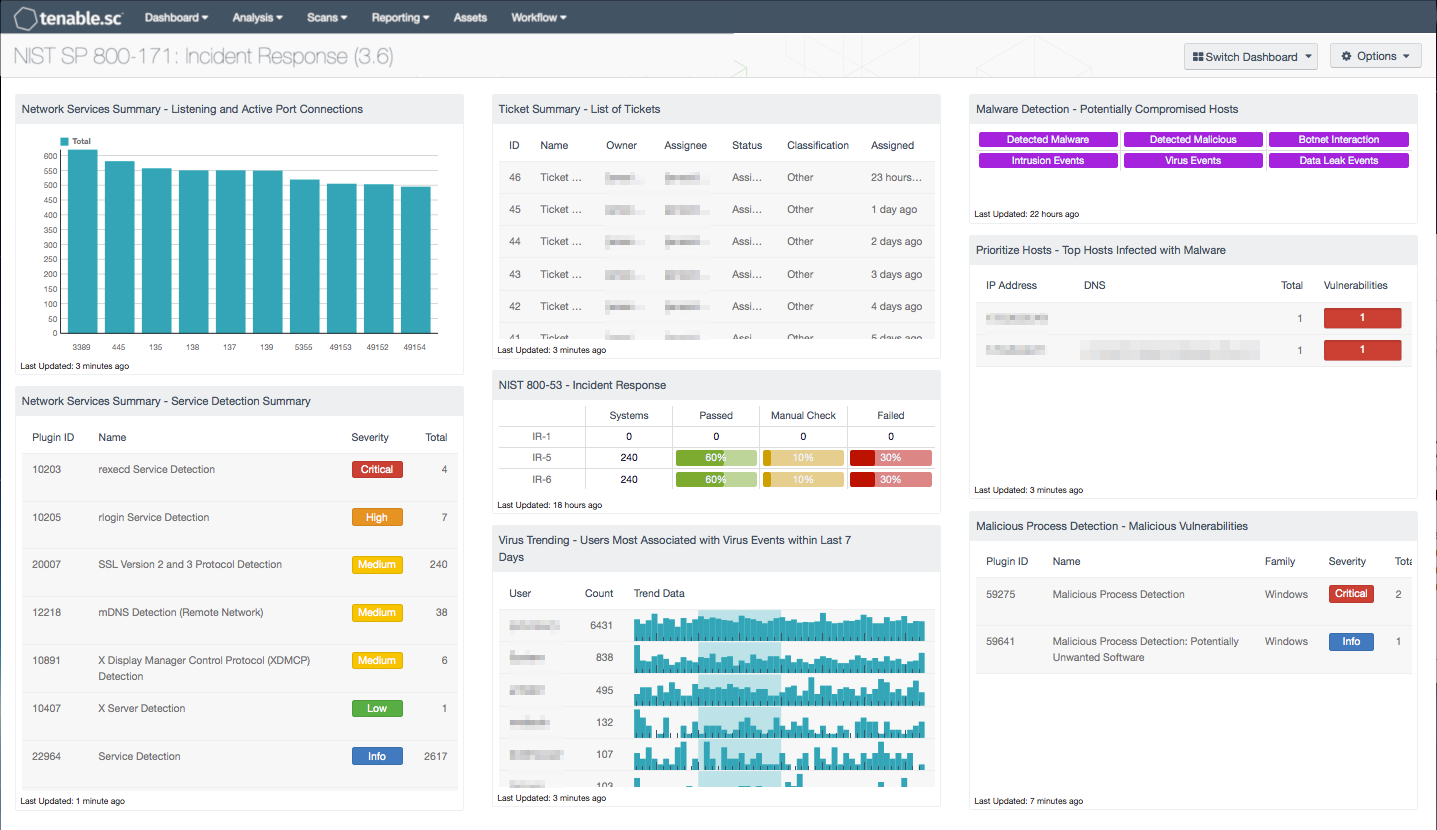
This dashboard aligns with the Incident Response family of security requirements in NIST SP 800-171 (section 3.6). These requirements focus on establishing an operational incident-handling capability for organizational information systems that includes adequate preparation, detection, analysis, containment, recovery, and user response activities. Using this dashboard, an organization will be better able to track and improve the overall incident response procedures.
Several components within this dashboard display information to assist the analyst in detecting potentially compromised hosts, intrusion events, and malicious processes. Additional components display compliance checks based on incident response audit findings, and ticketing details, which assist with tracking incident response efforts. This information will assist the organization in managing and properly restricting access to information systems that process, store, or transmit CUI. Analysts can use this dashboard to easily drill down into the data presented and gain more detailed information. If necessary, assets or subnet filters can be used to narrow the focus of this dashboard to only those systems that process, store, or transmit CUI.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment.The dashboard requirements are:
- Tenable.sc 5.4.0
- Nessus 8.4.0
- LCE 6.0.0
- NNM 5.9.0
- Compliance data
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in identifying, tracking and reporting incidents. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to find vulnerabilities, and can also make use of audit files to assess compliance. Passive listening provides real-time monitoring to collect information about systems and vulnerabilities. Host data and data from other security devices is analyzed to monitor policy and configuration settings activity. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to secure systems and safeguard sensitive information.
The following components are included in this dashboard:
- Network Services Summary - Listening and Active Port Connections: This bar chart presents the top 10 ports detected on hosts that are listening or have active port connections. Nessus provides several plugins that leverage the “Netstat” command to determine all listening and enabled connections on hosts. This component can be modified to include specific port connections per organizational requirements. Analysts can browse the component data to obtain additional information on hosts, services, and port activity.
- Network Services Summary - Service Detection Summary: This component presents a list of services detected on internal network hosts. Services presented within this table can include network protocols, databases, servers, remote desktop services, and more. Some of this information can also include insecure protocols such as FTP, Telnet, and SSL protocols. The table is sorted by severity which will allow for quick detection and remediation of insecure protocols by analysts. Analysts can modify the table to report on specific information per organizational requirements.
- Ticket Summary - List of Tickets: This table presents a status summary of tickets issued within the Tenable.sc Ticketing and Alert System. Tickets are a means by which tasks are assigned to users to perform important actions such as vulnerability remediation or incident response. Tickets can be created manually or automatically by a predefined set of conditions through the alerting functionality. Integration with any existing third-party ticketing systems is also supported, typically via email notification. This component displays the number of tickets in each ticket status.
- NIST 800-53 - Incident Response: The Incident Response family identifies auditable settings to support incident response efforts. This component provides a series of indicators for the NIST 800-53 controls. The first column provides a count of systems with compliant checks, while the other three columns reflect the status of audit check using the ratio bar. Passed means the scan found the check to be within the defined parameter, while red means the check was outside of the defined parameter. Orange means the check requires a manual review of the data to determine pass or fail. This component monitors the following NIST 800-53 audit controls: Incident Response Policy and Procedures (IR-1), Incident Monitoring (IR-5), and Incident Reporting (IR-6).
- Virus Trending - Users Most Associated with Virus Events within Last 7 Days: This component presents trend data for those users most associated with virus activity within the last 7 days, along with their associated event counts. The top 15 users with the highest event counts are displayed. This component provides insight into which users may be engaging in activity that exposes the network to viruses.
- Malware Detection - Potentially Compromised Hosts: This component presents indicators that highlight potentially compromised hosts. The top row of indicators highlight those hosts that have a high probability of being compromised, including hosts with detected malware infections, hosts with detected malicious activity, and hosts interacting with known bad IP addresses. The second row of indicators highlight hosts with suspicious activity that may indicate a compromise, including those hosts with intrusion events, virus events, and data leakage events. If an event or activity has been detected on a host, the indicator will turn purple. Analysts can drill down and obtain information on the hosts involved, event activity, and potential remediation solutions.
- Prioritize Hosts - Top Hosts Infected with Malware: This table displays the top hosts on the network that have actively or passively detected malware infections. The list is sorted so that the host with the worst malware problem is at the top. A count of malware detections and a bar graph indicating the severity of the malware are given for each host. Use this table to determine the hosts with the biggest malware problems on the network.
- Malicious Process Detection - Malicious Vulnerabilities: The Malicious Vulnerabilities component presents detections of malicious files, processes, or activity. Nessus can scan hosts for malicious activity and provide additional details that analysts can use to detect, mitigate, and prevent the spread of malware on the network. Information presented within this component includes detections of malicious processes, backdoors, known bad Windows AutoRuns, interactions with known bad IP addresses, and other types of malicious activity across Windows, Linux, and Mac OS X systems. This information can be useful in correlating malicious files that have been detected by anti-virus clients. Using the Vulnerability Detail List tool, analysts can drill down to obtain additional information.