by Josef Weiss
October 10, 2016
Protecting information system media containing Controlled Unclassified Information (CUI), and monitoring for the use of portable storage devices and removable media is essential to protecting the integrity of information systems. Monitoring organizational communications at external boundaries, as well as key internal boundaries is essential to detect attacks, and potential indicators of attacks. Removable media is commonly used to transfer electronic media from one computer to another. Users who place restricted information on removable media may inadvertently place organizations at risk for data theft or data loss. Access to CUI should be protected and limited to authorized users.
The federal government relies heavily on external service providers and contractors to assist in carrying out a wide range of federal missions. Sensitive but unclassified federal information is routinely processed by, stored on, or transmitted through nonfederal information systems. Failing to properly protect this CUI could impact the ability of the federal government to successfully carry out required missions and functions.
The National Institute of Standards and Technology (NIST) created Special Publication 800-171 "Protecting Controlled Unclassified Information in Nonfederal Information Systems and Organizations" to provide recommended requirements for protecting the confidentiality of CUI. Federal agencies should use these requirements when establishing contracts and agreements with nonfederal entities that process, store, or transmit CUI.
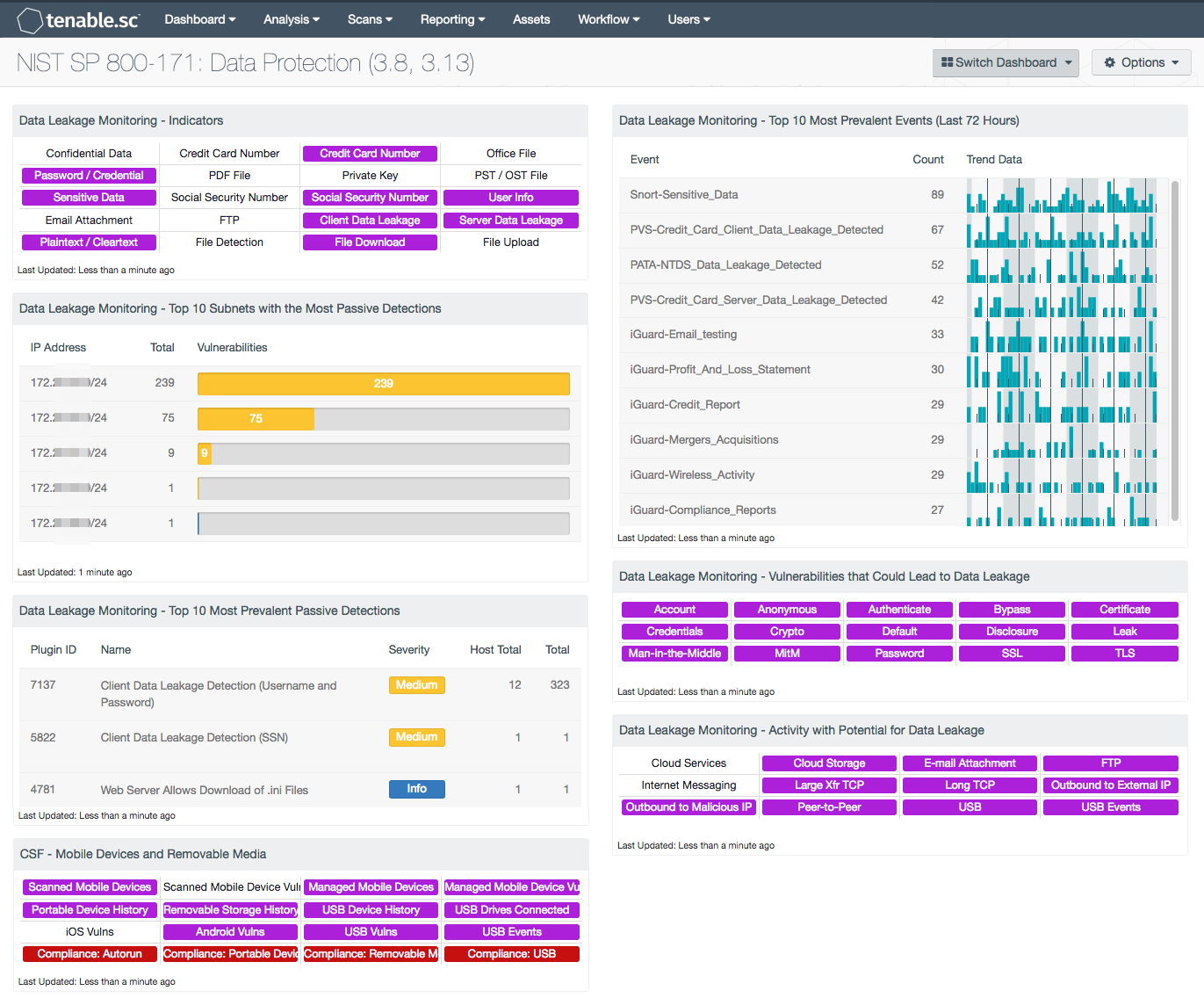
This dashboard aligns with the Media Protection (section 3.8) and System and Communications Protection (section 3.13) families of security requirements in NIST SP 800-171. These families are closely related and requirements focus on the monitoring, control, and protection of organizational communications at the external and key internal boundaries. Examples of key internal boundaries include information system media containing CUI, such as removable devices. Using this dashboard, an organization will be better able to identify the use of removable media on information system components, and identify cryptographic mechanisms used to protect the confidentiality of CUI. Organizations will also be able to monitor and protect communications (i.e., information transmitted or received by organizational information systems) at the external and key internal boundaries of the information systems, and take appropriate actions in response.
Components in this dashboard assist in the protection and the confidentiality of CUI in transit and at rest. This information will assist the organization in managing and properly restricting access to information systems that process, store, or transmit CUI. Analysts can use this dashboard to easily drill down into the data presented and gain more detailed information. If necessary, assets or subnet filters can be used to narrow the focus of this dashboard to only those systems that process, store, or transmit CUI.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.0
- Nessus 8.4.0
- LCE 6.0.0
- NNM 5.9.0
- Compliance data
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in detecting unauthorized and unintended information transfer via shared system resources. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to find vulnerabilities, and can also make use of audit files to assess compliance. Passive listening provides real-time monitoring to collect information about systems and vulnerabilities. Host data and data from other security devices is analyzed to monitor policy and configuration settings activity. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to secure systems and safeguard sensitive information.
The following components are included in this dashboard:
- Data Leakage Monitoring - Indicators - This component presents warning indicators to draw attention to types of data that may have been leaked and methods whereby data may be leaking.
- Data Leakage Monitoring - Top 10 Subnets with the Most Passive Detections - This table presents the top 10 Class C subnets with the most passive detections of data leakage.
- Data Leakage Monitoring - Top 10 Most Prevalent Passive Detections - This table presents the top 10 most prevalent passive detections of data leakage.
- CSF - Mobile Devices and Removable Media - This component assists an organization in monitoring mobile devices and removable media.
- Data Leakage Monitoring - Top 10 Most Prevalent Events (Last 72 Hours) - This table presents the most prevalent logged data leakage events in the last 72 hours.
- Data Leakage Monitoring - Vulnerabilities that Could Lead to Data Leakage - This component presents indicators by keyword for actively and passively detected vulnerabilities that could lead to data leakage.
- Data Leakage Monitoring - Activity with Potential for Data Leakage - This component presents indicators for activity detected on the network that has the potential for data leakage.