by Stephanie Dunn
May 16, 2016
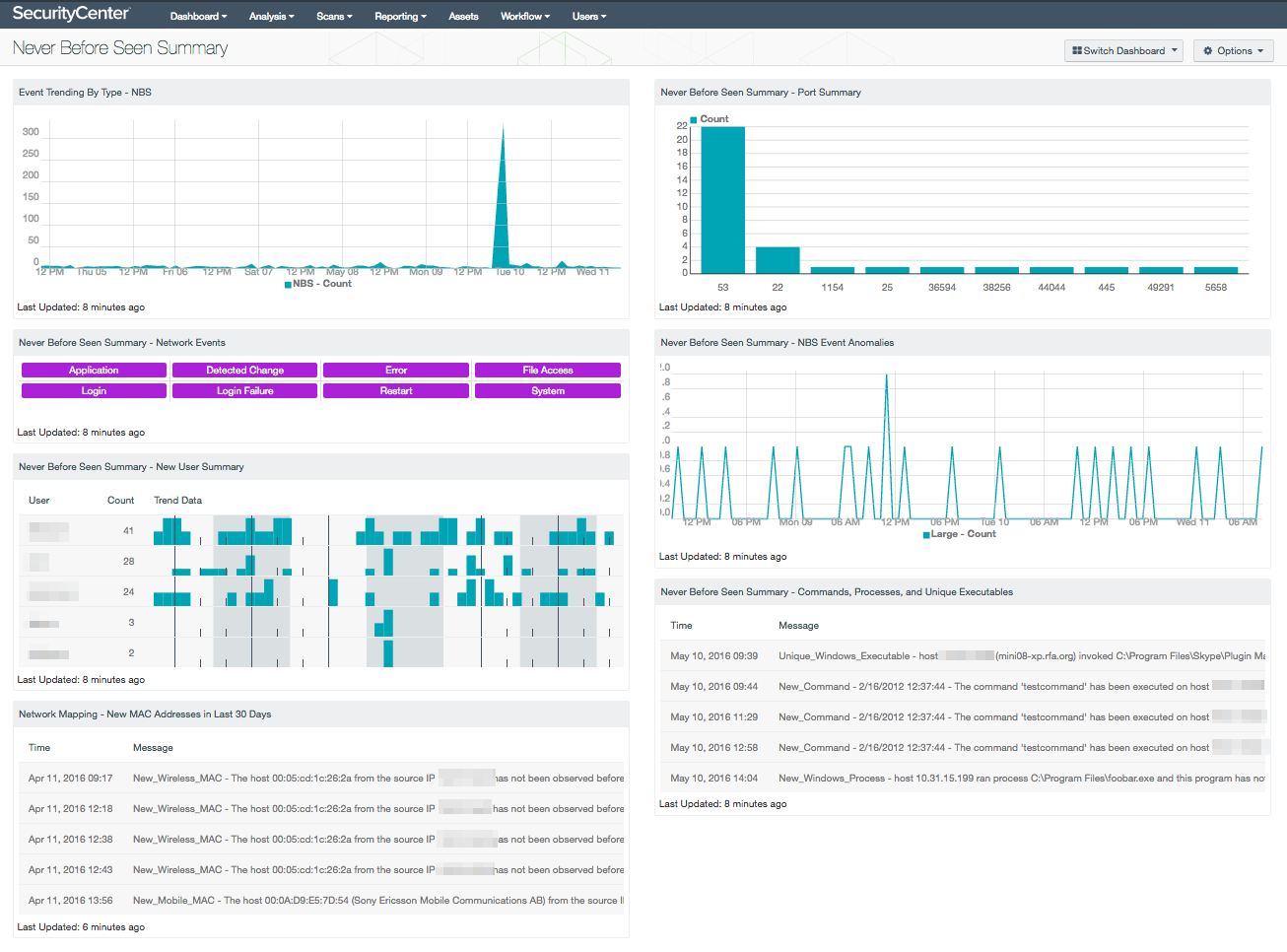
Log data provides valuable insight into new, unique, and events that have never been previously seen on the network. Organizations can produce a large amount of log data on a daily basis, and without a centralized log management solution in place, many newly detected events can be overlooked. This dashboard presents a summary of newly detected events on the network, which can assist in detecting targeted privileged user accounts, unauthorized login attempts, and network pivoting activities.
Never before seen events can highlight a wide variety of network activity both to and from a host. These types of events can also alert analysts to unusual login activity, which can help determine if any accounts are being used for malicious purposes. Monitoring new login attempts can help to identify unauthorized access or brute-force attacks against a host. Information on newly detected hosts can assist an organization in maintaining an accurate inventory, and can also assist in detecting any unauthorized mobile or rogue devices on the network. Network anomalies may indicate new applications being deployed, new types of network usage, and new user account changes. Having accurate information of newly discovered events can enable organizations to effectively monitor files, user accounts, and network hosts for suspicious events, while reducing overall risk.
This dashboard leverages the Tenable Log Correlation Engine (LCE) “nbs” event type, which provides valuable information on access attempts, file downloads, user account changes, and more. As logs are normalized, LCE will track the event and IP address that are associated with the log, and alert if the event has never been seen previously for that host. Several components provide a never before seen summary of port usage and network events. New user activity will present detailed information on both authorized and unauthorized login activity. New processes and command activity can identify specific commands used or programs accessed by end users. A summary of newly detected workstations, servers, mobile, and wireless devices will assist in maintaining an accurate asset inventory. Using this dashboard, organizations will be able to effectively monitor and manage never before seen events within the network.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Discovery & Detection. The dashboard requirements are:
- SecurityCenter 5.3.2
- LCE 4.8.0
Tenable SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. The Tenable Passive Vulnerability Scanner (PVS) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. The Tenable Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, PVS, and LCE, SecurityCenter CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
The following components are included in this dashboard:
- Event Trending by Type - NBS: This component provides a 7-day trend analysis of the Never Before Seen (NBS) events. The LCE tracks all normalized events that have occurred for each host. As new normalized events are logged for the host, the LCE will generate secondary events based on the event type. This is a core type of correlation performed by the LCE. For example, perhaps a Linux server is set up with SSH and has only ever had users login with passwords. The first time a user tried to login with an incorrect certificate, the resulting SSH-Failed_Publickey event would cause the LCE to generate a Never_Before_Seen-Login-Failure_Event.
- Never Before Seen Summary – Network Events: The Network Events matrix presents indicators of never before seen (NBS) activity over the last 72 hours. The LCE tracks “nbs” normalized events that have occurred for each host. As new normalized events are logged for the host, the LCE will generate secondary event information based on the event type. This information may indicate changes in access patterns and can indicate new logins, user removal, expired accounts, and new file downloads. This component can be customized based on organizational requirements.
- Never Before Seen Summary – New User Summary: The New User Summary table presents a trend of new user events detected within the last 72 hours. The “New_User” event records the first time a user logs in to a new host and/or a new account type on a host. The “New network user” event records the first time a user is ever seen on the network. The “New_User_Source” event records the first time a user logs in from a new host. The “New_SSH_User” event records the first time that an SSH username is detected that has not been previously detected on the host. Analysts can drill down to obtain additional information on the user account, and IP address associated with the event. All of these new user accounts should be verified to determine whether the account is authorized on the network.
- Network Mapping – New MAC Addresses in Last 30 Days: This table lists all the new MAC addresses that have never been observed before on the network, and that were first observed in the last 30 days. Tenable's LCE sets the New_MAC event when a new, never-before-seen MAC address is observed on the network. This table reports those New_MAC events, displaying the time observed and the raw syslog text, which contains the new MAC address and its associated IP address. Discovering new hosts on the network can assist an organization in maintaining an accurate inventory and detecting rogue devices.
- Never Before Seen Summary – Port Summary: The Port Summary chart presents a port summary of never before seen events within the last 30 days. Events are normalized by LCE and filtered on the event type “nbs.” This information will help analysts identify DNS changes, SSH activity, as well as any ports being used for malicious purposes. Analysts can drill down and set the tool to IP Address or Raw Syslog Events to obtain additional information on the specific event.
- Never Before Seen Summary – NBS Event Anomalies: The NBS Event Anomalies chart presents a trend never before seen (NBS) large statistical anomaly events that have occurred within the last 72 hours. Events are triggered when the LCE stats daemon has found an event spike that has never been seen previously on the network. For all events of this type being sent to the LCE, the stats daemon has compared this hour's event rate for each unique targeted IP address to the same hour in each previous day for the entire body of collected data. Anomalies can indicate new applications being deployed, new types of network usage, and new behaviors from existing users, or potentially from attackers or malicious insiders. A large anomaly would have between 100.0 and 999999.99 units of standard deviation. The formula for standard deviations is explained further in the Log Correlation Engine 4.4 Statistics Daemon Guide available on the Tenable Support Portal. This component can be modified to include specific or additional event information per organizational requirements.
- Never Before Seen Summary – Commands, Processes, and Unique Executables: This table presents a summary of new commands, processes, and unique executables that have not been previously detected on the network. This information may alert the analyst to new programs used for the first time, privilege escalation, or lateral movement by an attacker within the network. In addition, analysts can also use this information to identify systems with weak security policies in place. Analysts can drill down to obtain additional information about commands, processes, and applications accessed by end users.