by Stephanie Dunn
December 14, 2016
As mobile workforce demands continue to increase, organizations must provide a secure way to remotely access, connect, and exchange information without compromising network security. Many organizations allow mobile and portable devices to be used without any additional security controls in place that can protect corporate data from being misused. Mobility demands have also resulted in organizations implementing bring your own device (BYOD) policies to support mobility needs. These devices are usually running outdated operating systems, and contain vulnerabilities that can spread malware, leak confidential data, and infect other network assets. Enabling security controls that protect data-at-rest and data-in-motion will help to reduce overall security risks and support mobility requirements. This dashboard covers key concepts within the ITSG-33 guide that will assist analysts in managing mobile devices, tracking portable device usage, and monitoring usage of cloud-based services.
The Communications Security Establishment Canada (CSEC) developed a series of guidelines for security practitioners in managing information technology (IT) security risks for Government of Canada (GC) information systems. The Information Technology Security Guidance Publication 33 (ITSG-33), IT Security Risk Management: A Lifecycle Approach provides a comprehensive set of security controls that can be used to support a wide variety of business requirements. To support interoperability needs, the ITSG-33 guide is consistent with controls published in the U.S. National Institute of Standards and Technology (NIST) Special Publication 800-53. Data presented within this dashboard aligns with ITSG-33 security controls that support remote access security, mobile device activity, and monitoring portable devices usage. This dashboard aligns with the following controls:
- Remote Access (AC-17)
- Wireless Access (AC-18)
- Access Control for Mobile Devices (AC-19)
- Use of External Information Systems (AC-20)
Having the ability to access data remotely in today’s competitive marketplace is critical in an organization’s long term survival. Devices used to support the mobile workforce can include unmanaged devices that are often outdated and contain vulnerabilities that can leave critical systems or data at risk. Additional risks can include the usage of personal cloud-based services to store and access corporate data from anywhere. Organizations that fail to monitor and protect data from being stored in the cloud can lead to confidential information being inadvertently or intentionally exposed.
This dashboard will assist organizations with monitoring mobile devices, remote access solutions, access to cloud-based services, and detection of wireless devices on the network. Analysts can use the information presented to detect vulnerabilities on both scanned and managed MDM-based mobile devices. This information can be used to prevent outdated or unauthorized mobile devices from connecting to the network. Monitoring wireless devices and events can alert analysts to rogue devices or unauthorized wireless devices currently in use. Access to cloud-based services will help security teams identify and prevent corporate data from being stored outside of the network.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.1
- Nessus 8.5.1
- LCE 6.0.0
- PVS 5.2.0
Tenable's Tenable.sc Continuous View (CV) will provide continuous visibility enabling organizations to take decisive actions to secure the enterprise. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns on remote access solutions and portable devices. Passive listening provides real-time discovery of vulnerabilities on mobile and portable devices. Host data and data from other security products is analyzed to monitor the network for secure communications, remote access activity, and portable device connections. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to support workforce mobility requirements.
The following components are included within this dashboard:
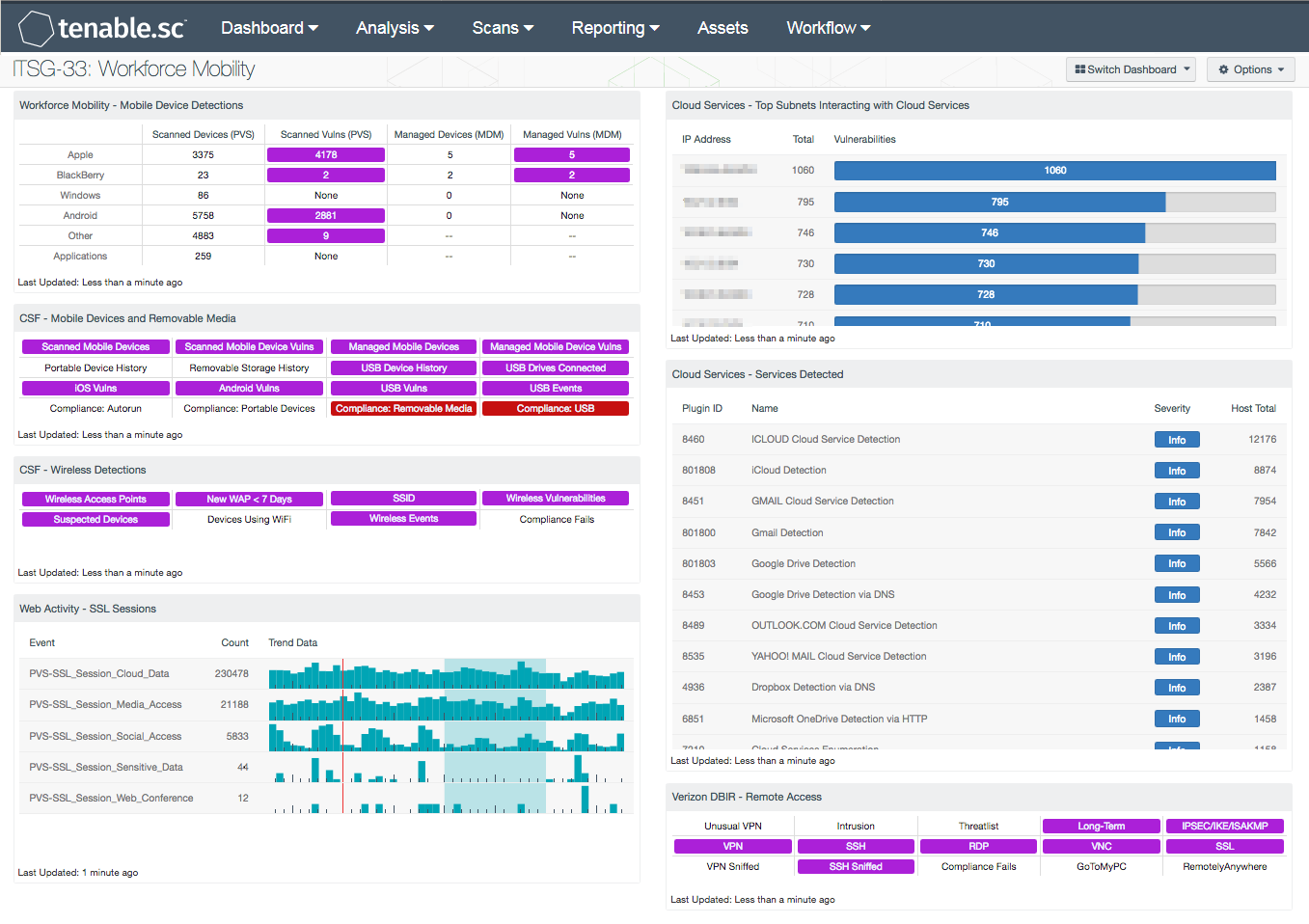
- Workforce Mobility - Mobile Device Detections: This component presents counts of mobile devices and associated vulnerabilities detected passively by the Tenable Nessus Network Monitor (NNM) and via Mobile Device Management (MDM) systems. The rows break down the detected devices by OS/Vendor. The last row presents those mobile devices and vulnerabilities detected via mobile applications. Clicking on a highlighted indicator will bring up the vulnerability analysis screen to allow further investigation.
- CSF - Mobile Devices and Removable Media: This component assists an organization in monitoring mobile devices and removable media. Indicators are highlighted purple for mobile devices detected through active and passive scans, and for mobile devices managed through an MDM server. Indicators are also presented for device connection histories, vulnerabilities, and USB events. Additional indicators are highlighted red for compliance failures related to portable devices and removable media. Clicking on a highlighted indicator will bring up the analysis screen to display details on the detections and events and allow further investigation.
- CSF - Wireless Detections: This component presents a breakdown of detected wireless access points, wireless vulnerabilities, and wireless event activity on the network. Indicators will turn purple when an event or vulnerability is detected. Analysts can drill down to obtain additional information, including IP addresses and MAC addresses. This information can assist an organization in maintaining an accurate inventory and detecting any unauthorized wireless devices.
- Web Activity - SSL Sessions: This component presents passive detections of SSL session traffic over the last 72 hours to various destinations, including cloud file storage access, access to services commonly used for sensitive data, and social media access. A count and trend is included for each of the events. Clicking on the Browse Component Data icon will bring up the event analysis screen to allow further investigation. Viewing the raw syslog of the events will show the SSL connection times and destinations.
- Cloud Services - Top Subnets Interacting with Cloud Services: This component displays the top Class C subnets with passive detections of interactions with cloud services such as iCloud, Google Drive, Dropbox, Salesforce, DocuSign, and others. Presenting these interactions by subnet allows easy understanding of which areas of the network are interacting most with the cloud, and if any areas of the network that are not supposed to be interacting with the cloud in fact are.
- Cloud Services - Services Detected: This table presents a list of passive detections of network interactions with cloud services. This information can be used to determine which cloud services are most used and if any unauthorized services are being used.
- Verizon DBIR - Remote Access: The Verizon DBIR notes that it is important to restrict remote access to systems. This matrix assists the organization in monitoring remote access activity across the network. Multiple indicators highlight VPN, SSH, RDP, VNC, and SSL traffic events within the last 72 hours, including potential intrusion events, events associated with known bad IP addresses (threatlist), and long-term events. The VPN Sniffed and SSH Sniffed indicators are highlighted purple if those protocols, respectively, are passively detected on the network. The Compliance Fails indicator is highlighted red if there are any remote access compliance failures. The GoToMyPC and RemotelyAnywhere indicators are highlighted purple if those applications are detected on the network.