by Cesar Navas
January 14, 2016
Required - IT-Grundschutz BSI-100-2 audit file.
The IT-Grundschutz Standards and Catalogues are a set of recommendations designed to assist an organization in achieving an appropriate security level for information throughout an organization. The Federal Office for Information Security (BSI) in Germany develops and maintains the BSI Standards, of which IT-Grundschutz is a part. IT-Grundschutz provides methods, processes, procedures, and approaches to information security management, risk analysis, and business continuity management.
The BSI Standard 100-2 progressively describes step-by-step how information security management methods can be set up and operated in practice. The IT-Grundschutz methodology provides detailed descriptions such as how to produce a practical security concept, how to select appropriate safeguards, and what is important when implementing the security concept. The IT-Grundschutz Catalogues not only explain what has to be done but also provides specific information as to what the implementation would look like. Organizations can adapt the BSI Standards to their own needs and requirements.
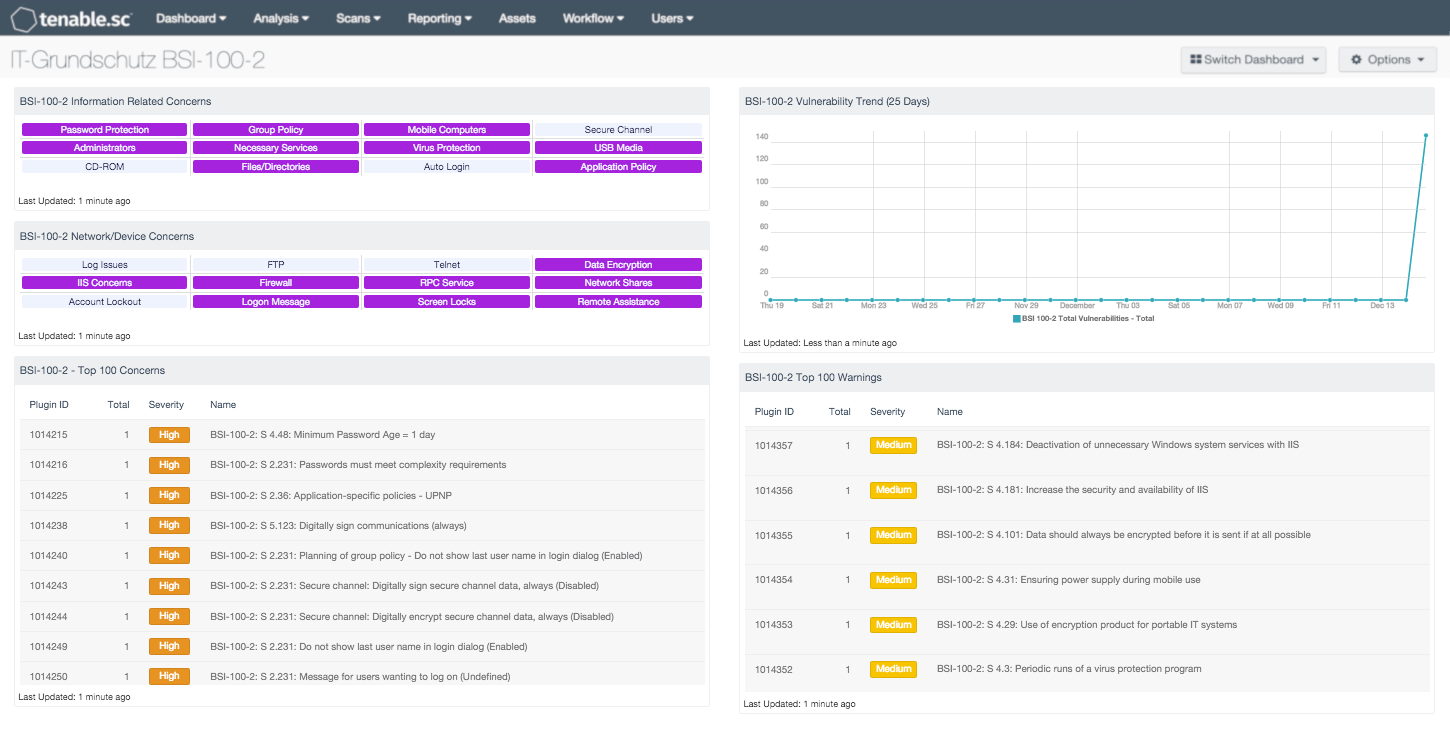
This customizable dashboard provides a quick view to assess compliance with IT-Grundschutz recommendations. This is achieved by utilizing cross-reference values within the components to sort and display vulnerability data associated with BSI-100-2 compliance results, without having to search manually through Nessus report results. The matrix indications and data present in this dashboard provide analysts with information to help organizations achieve IT-Grundschutz certification.
It is critical to utilize the BSI-100-2 Tenable audit file when conducting scans to produce BSI-100-2 vulnerability results.
Key benefits of this dashboard include the ability to continuously monitor devices on the network that may create organizational exposure. Additional benefits include compliance monitoring and analysis, identifying relevant assets, and limiting IT-Grundschutz audits to those assets. Thereby reducing time and resources required for regular scans.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance.
The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable.sc CV allows for the most comprehensive and integrated view of network health.
The dashboard contains the following components:
- BSI-100-2 - Information Related Concerns - This is an indicator style component that displays triggered vulnerabilities from IT-Grundschutz audits. Triggered indications are highlighted in purple.
- BSI-100-2 - Network/Device Concerns - This is an indicator style component that displays triggered vulnerabilities from IT-Grundschutz audits. Triggered indications are highlighted in purple.
- BSI-100-2 - Top 100 Concerns - This table displays the Top 100 triggered high/critical vulnerabilities based on results from IT-Grundschutz audits.
- BSI-100-2 - Vulnerability Trend (25 Days) - This component displays trend data over the last 25 days of the total count of IT-Grundschutz triggered vulnerabilities.
- BSI-100-2 - Top 100 Warnings - This table displays the Top 100 triggered warnings based on results from IT-Grundschutz audits.