by Stephanie Dunn
June 20, 2016
Vulnerabilities within web applications are typically the result of poor coding practices and security flaws that can be introduced throughout the software development lifecycle. Attackers can exploit these vulnerabilities to obtain customer account data, expose confidential information, and leave an organization with additional breach-related costs. The ISO/IEC27000 Secure Development dashboard can assist the organization by identifying vulnerabilities and events associated with weak programming practices.
The ISO/IEC 27002:2013 framework is a global security standard that provides best practice solutions in support of the controls found in Annex A of ISO/IEC 27001:2013. The framework establishes guidelines and general principles for initiating, implementing, maintaining, and improving Information Security Management Systems (ISMS). Each security control and objective provided within the standard can be tailored to specific business and regulatory objectives, and assist with maintaining overall compliance. This dashboard focuses on the ISO/IEC 27002 14.2 control that can be used to reduce or eliminate security flaws within source code.
Applying secure coding practices, code reviews, along with performing regular vulnerability scans and penetration tests can help to reduce negative impacts on an organization. Any coding changes must be strictly controlled, documented, and reapplied where needed. Organizations that outsource application development need to ensure that sufficient application testing is performed to address any potential security risks. Additional guidance on supplier relationships can be found within the ISO/IEC 27036:2014 guide.
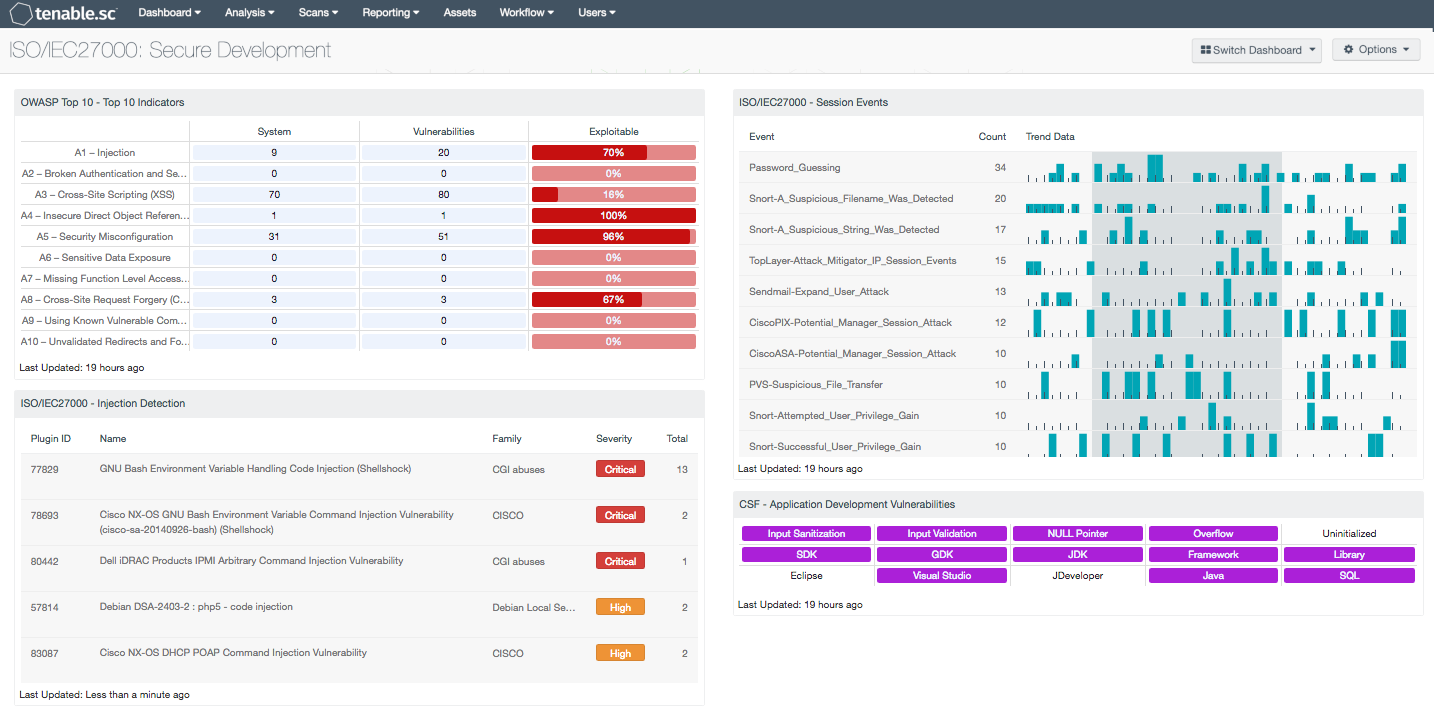
Security and development teams can use this dashboard to help stop attacks before they begin. The OWASP Top 10 web security flaws will detect threats such as Local File Inclusion (LFI), Remote File Inclusion (RFI), Directory Traversal, cross-site scripting (XSS), and web server vulnerabilities. Other components will detect injection activity; session attacks, repeated password guessing, and unauthorized privilege attempts. Both Nessus and NNM can detect specific vulnerabilities from development kits, frameworks, libraries, common IDEs, and development software. Together, this dashboard will assist organizations in strengthening overall coding practices by quickly identifying security flaws that impact critical applications.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring platform. Tenable’s Log Correlation Engine (LCE) performs automatic discovery of users, infrastructure, and vulnerabilities across more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. NNM provides deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable.sc CV, Nessus, Log Correlation Engine (LCE) and Nessus Network Monitor (NNM) scales to meet future demand of monitoring virtualized systems, cloud services, and the proliferation of devices.
This dashboard contains the following components:
- OWASP Top 10 - Top 10 Indicators: This component collects the vulnerabilities from the CGI Abuses, CGI Abuses : XSS, and Web Servers plugin families for both active and passive vulnerabilities. The CGI Abuses family Checks for web-based CGI programs with publicly documented vulnerabilities. These checks include SQL injection, Local File Inclusion (LFI), Remote File Inclusion (RFI), Directory Traversal, and more. For web-based CGI programs with publicly documented cross-site scripting (XSS) vulnerabilities, the CGI Abuses : XSS plugin family is used. For web server vulnerabilities, the Web Server plugin family can detect vulnerabilities in web servers such as Apache HTTP Server, IBM Lotus Domino, Microsoft IIS, and many more.
- ISO/IEC27000 - Injection Detection: This component presents a list of detected injection attacks on a network. Vulnerabilities within this table can include attacks such as SQL, PHP, and HTML based injections, which can uncover sensitive data and lead to loss of confidentially, integrity, and availability. Analysts can use this information to identify vulnerable web applications on a network.
- ISO/IEC27000 - Session Events: The Session Events component presents a table of suspicious session events on a network. Events are normalized by LCE and filtered on the event type of “intrusion”, which can include events such as session attacks, repeated password guessing, and unauthorized privilege attempts. This can allow attackers to compromise passwords, suspicious events, or to exploit other vulnerabilities to assume other users’ identities. Data provided within this table can assist analysts in detecting broken session events, which can assist in identifying and repairing security flaws within source code.
- CSF - Application Development Vulnerabilities: This component displays indicators for actively and passively detected vulnerabilities related to application development. Each indicator is highlighted purple if vulnerabilities with the given keyword(s) in their name are detected. The first row highlights common application development errors. The second row highlights vulnerabilities in development kits, frameworks, and libraries. The third row highlights vulnerabilities in several common IDEs and technologies. Note that because compliance failures are tracked as vulnerabilities, they will be included. An organization can develop its own Nessus or NNM plugins to discover vulnerabilities associated with its own internal software development; these detections will automatically appear here if the plugin names contain the appropriate keywords. New indicators can also be added as desired. Clicking on a highlighted indicator will bring up the vulnerability analysis screen to display details for the vulnerabilities and allow further investigation. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities are present. Setting the tool to Vulnerability Details will display the full details for each vulnerability, including a description, the solution to fix the vulnerability, and in some cases, links to more information.